In the past years, ransomware has skyrocketed to become one of the most popular cyberattack techniques, impacting small, medium, and large organizations alike. Cybercriminals, constantly developing new ransomware variants, challenge even the brightest security experts and malware detection programs. And by the time a variant is known or the decryption key is made available to the public, new ransomware malware comes along.
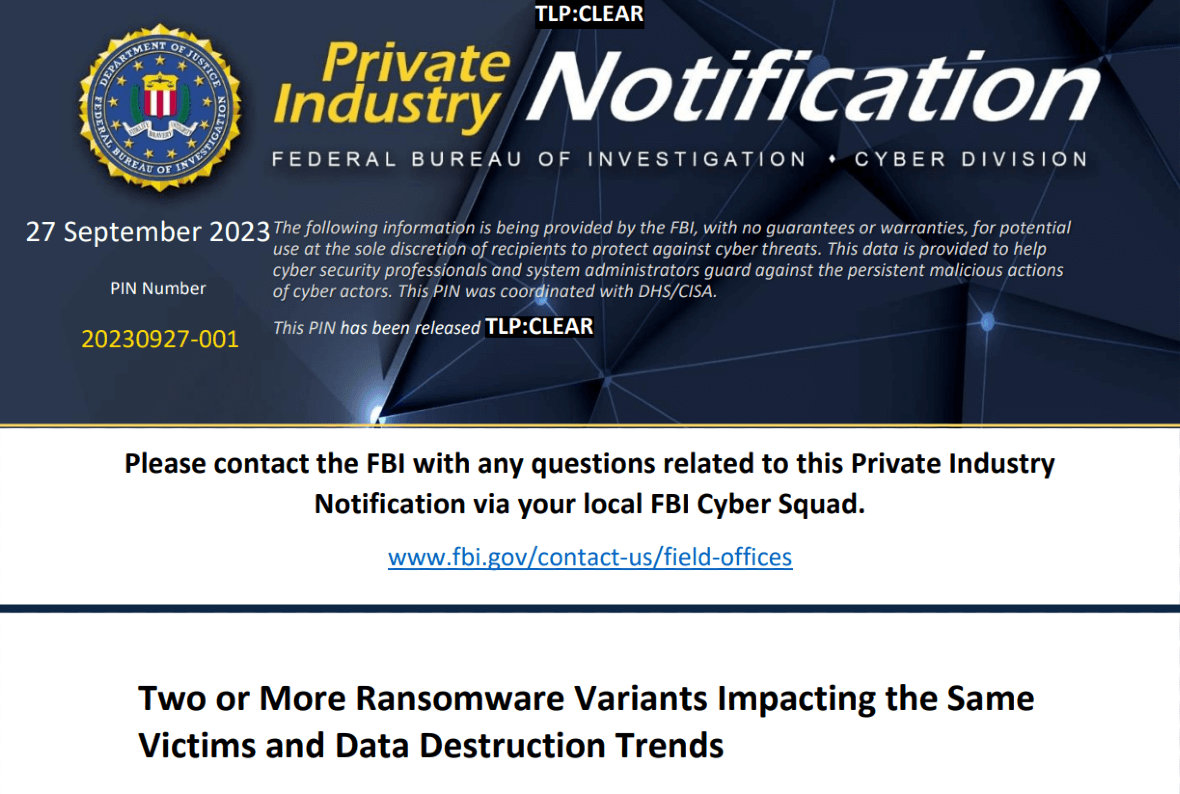
On September 27, the FBI issued an official warning regarding two trends emerging across the ransomware environment. The first involves new data destruction tactics. The second is a series of double ransomware attacks against the same victims, one attack after another. These are the trends that individuals and businesses should be on the lookout for, the FBI says.
Double back-to-back ransomware attacks: How it works
The FBI explains that since July 2023, they have been noticing multiple ransomware attacks being launched in close proximity to another attack.
“Second ransomware attacks against an already compromised system could significantly harm victim entities,” the FBI explains.
This is how this type of ransomware attack works:
- The victim’s system is breached either by phishing, account takeover, brute force, or other means.
- Once inside the system, cybercriminals launch ransomware malware that encrypts all of the victims’ data and files.
- Closely after this attack, another ransomware malware is launched on the victim’s system.
- This double ransomware attack allows criminals to encrypt and exfiltrate data (extract it from the system). They can then demand ransom payments from companies and individual users alike.
Some of the ransomware malware being used in this new trend include variants of AvosLocker, Diamond, Hive, Karakurt, LockBit, Quantum, and Royal. Bad actors deploy the malware one after the other, using different combinations.
Attackers have leveled up their data destruction tactics
Not only are criminals breaching systems to install two ransomware variants, but they are also leveling up their data destruction abilities. The FBI noted that since early 2022, several ransomware groups have increased the use of custom data theft malware, wiper tools, and malware that affects systems to pressure victims into paying a ransom.
Data theft tools and wipers are being re-coded by attackers for several reasons. It is done to increase efficiency, avoid detection, and execute advanced persistent threat (APT) attacks.
In these APT attacks, the data theft and wipers are installed into a breached system. There, they remain dormant until a set time when they will begin corrupting data in alternating intervals. These new features make the work of security teams extremely difficult.
How you can stay safe from the new ransomware attacks
For most types of cyberattacks, good anti-malware and strong security practices are enough. But to beat ransomware, several steps must be taken. These steps include:
Backups: Data and systems need to be backed up regularly. Businesses should keep a copy offline isolated in air-gap systems (not connected online).
Encryption: All data needs to be encrypted. That includes data that is being stored or data that is in transit. All data must also be protected against modifications or deletions.
Third parties: Your systems may be top of the line, but if you outsource digital services to third parties, such as cloud providers or password managers, you must make sure they have a strong ransomware cybersecurity strategy in place.
Anti-malware solutions: Trusted anti-malware software is critical to detect phishing attempts, malicious files, links or websites, and any malware that might breach your first layers of security. Anti-malware solutions can rapidly flag, alert, shut down, and remove ransomware malware before they can do any damage.
Companies also need to have a solid ransomware recovery plan. On the other hand, individual users must put their own security cultures into practice. Always be suspicious of unknown contacts and use strong passwords, along with multi-factor authentication.
Businesses that run more advanced digital operations should read the full technical recommendations released by the FBI for double ransomware attacks.
The ongoing fight against ransomware
Ransomware cybercriminal groups will never stop innovating. They will continue to find new ways to breach systems, create more damage, and pressure people, organizations, and businesses to pay costly ransoms.
If you’re the owner of a small, medium, or large business, it is highly recommended that you contact law enforcement when you are hit by a ransomware attack. Law enforcement can offer assistance and support and may even help you resolve the incident.
Cybersecurity experts agree that paying a ransom in no way guarantees that criminals will return your data to you. They still may leak it or sell it down the line to the best bidder on the dark web.
The best protection that users have against ransomware is preventive cybersecurity. Follow this guide to keep your accounts secure. Stay on top of new trends to understand how ransomware is evolving and can impact you.