One of the best ways to thwart online attackers is through encryption. Cybersecurity professionals use encryption to protect email, messaging, and applications and keep data private. However, you must understand that there are two types of encryption: symmetric and asymmetric.
Keep reading this guide to learn more about the difference between the two types of encryption, which is more secure, and how it all works.
Add asymmetric encryption to your browsing
What is symmetric encryption?
Symmetric encryption is a security technique that uses a single key to lock and unlock data to keep it private. The key encrypts plaintext and then decrypts it when it arrives at its destination.
Symmetric encryption is widely used and is also one of the oldest security methods, with variations of it dating back to the Roman Empire and Julius Caesar. Today, it is used in many industries, including banking, healthcare, and military applications to secure data.
Common symmetric encryption algorithms
Some of the most common symmetric encryption algorithms include:
- AES: Advanced Encryption Standard (AES), also known as Rijndael, is the most widely used form of symmetric encryption because it is very secure and works on virtually any platform. The military uses AES.
- Salsa20: Along with its many variants, this algorithm is modern, fast, and very secure. Salsa20 uses an initial input stream of 128-bit or 256-bit symmetric secret key plus a randomly generated 64-bit nonce. It then combines that with a stream of data (unlimited length) and produces an output the same length as the input stream.
- DES: The Data Encryption Standard (DES) uses only a 56-bit key size and is highly vulnerable. It can be broken by brute force and is rarely used anymore.
- Serpent: This modern encryption technique uses a secure symmetric-key block cipher (key size: 128, 192, or 256 bits).
- Twofish: This is another modern algorithm with a secure symmetric-key block cipher (key sizes: 128, 192, or 256 bits).
- IDEA: This secure algorithm uses a secure symmetric-key block cipher (key size: 128 bits). It was patented in 2012, but it is now royalty-free.
What is a symmetric key?
The term “symmetric key” refers to a cryptography mechanism that both encrypts and decrypts data. Symmetric cryptography means that anyone wishing to view the data must use the same key to enter it.
How does symmetric encryption work?
Symmetric encryption uses either a stream or block cipher. A stream cipher converts plaintext into ciphertext one byte at a time, whereas a block cipher converts blocks of plaintext into ciphertext based on a predetermined length (128, 192, or 256 bits). Although it sounds complex, all of this encryption and decryption happens automatically and instantly on your device or with a piece of software.
The pros and cons of symmetric encryption
Symmetric encryption has positives and negatives. The list of pros and cons are as follows:
Pros:
- Fast: Uses the same key for both encryption and decryption
- Efficient: Can encrypt large amounts of data efficiently
- Secure: Cracking an AES algorithm could take a billion years or longer
Cons:
- Key management: Sender and receiver need access to the same key
- Key distribution: It can be challenging to distribute the same key to large groups of people
What is asymmetric encryption?
Asymmetric encryption is another security method that uses public and private key pairs to encrypt and decrypt data. Instead of a single key, two linked keys are used. Plaintext is still converted into ciphertext. The difference is that the unique key pairs are encrypted and decrypted asymmetrically.
Common asymmetric encryption algorithms
Some of the most common asymmetric encryption algorithms used include:
- RSA: The Rivest–Shamir–Adleman (RSA) cryptographic algorithm factors the product of two prime numbers and uses that to encrypt a key with 1,024 bits or 2,048 bits. It would take more than 1,500 years to crack it.
- ECC: Elliptic-curve cryptography (ECC) uses a complex mathematical equation based on an elliptical curve to create a secure key. Due to its complexity, it is virtually impossible to crack. It can produce a 15,360-bit RSA key when used at its highest setting.
What is an asymmetric key?
An asymmetric key is a public key used to encrypt data and share it with a recipient with a private key to unlock it. In asymmetric cryptography, the private key is also called a secret key.
How does asymmetric encryption work?
The device encrypting the data creates a public/private key pair. The public key encrypts the data and turns it into ciphertext. Once it arrives at its destination, the secret key decrypts it and turns it back into plaintext so the recipient can access it.
The pros and cons of asymmetric encryption
As with symmetric encryption, using asymmetric encryption has its advantages and disadvantages:
Pros:
- Sharing: High security for sharing data in motion
- Secure: Excellent for signatures and secure documents
Cons:
- Slower: Takes more time to encrypt and decrypt
- Complex: More difficult to implement
What is the difference between symmetric and asymmetric encryption?
There are quite a few differences between the two types of encryption. For one thing, they use different mathematical equations and methods. Overall, asymmetric encryption is slower and more secure, and symmetric encryption is quicker but less secure.
The most significant difference, however, is that symmetric encryption uses one key, and asymmetric encryption uses two (key pairs) to encrypt and decrypt data.
One vs. two keys
Symmetric encryption uses one key to lock and unlock data, whereas asymmetric encryption uses a key pair to lock and unlock data.
Speed
Symmetric encryption is faster because it uses only one key to encrypt and decrypt the same data.
Efficiency
Asymmetric encryption uses more complex algorithms, which are slower and less efficient.
Security
Although more complex, asymmetric encryption is more secure and cannot be broken by brute force. Depending on the key size, some symmetric encryption is vulnerable to hackers.
Why is symmetric encryption faster?
Because it only uses one key to convert plaintext into ciphertext, the data doesn’t have to undergo as many steps.
Why is asymmetric encryption better than symmetric?
Asymmetric encryption uses a much more complex and larger key that remains nearly impossible to crack. However, due to the large, cumbersome processing required in asymmetric encryption, sometimes it’s more practical to use symmetric encryption. Each option has its place.
Where are the two encryption types used?
Symmetric and asymmetric encryption are used for specific purposes. They each have a role to play. The following are some of their common uses.
Web traffic security
Asymmetric encryption is used to secure web traffic through SSL certificate technology. It protects payment gateways and shopping experiences.
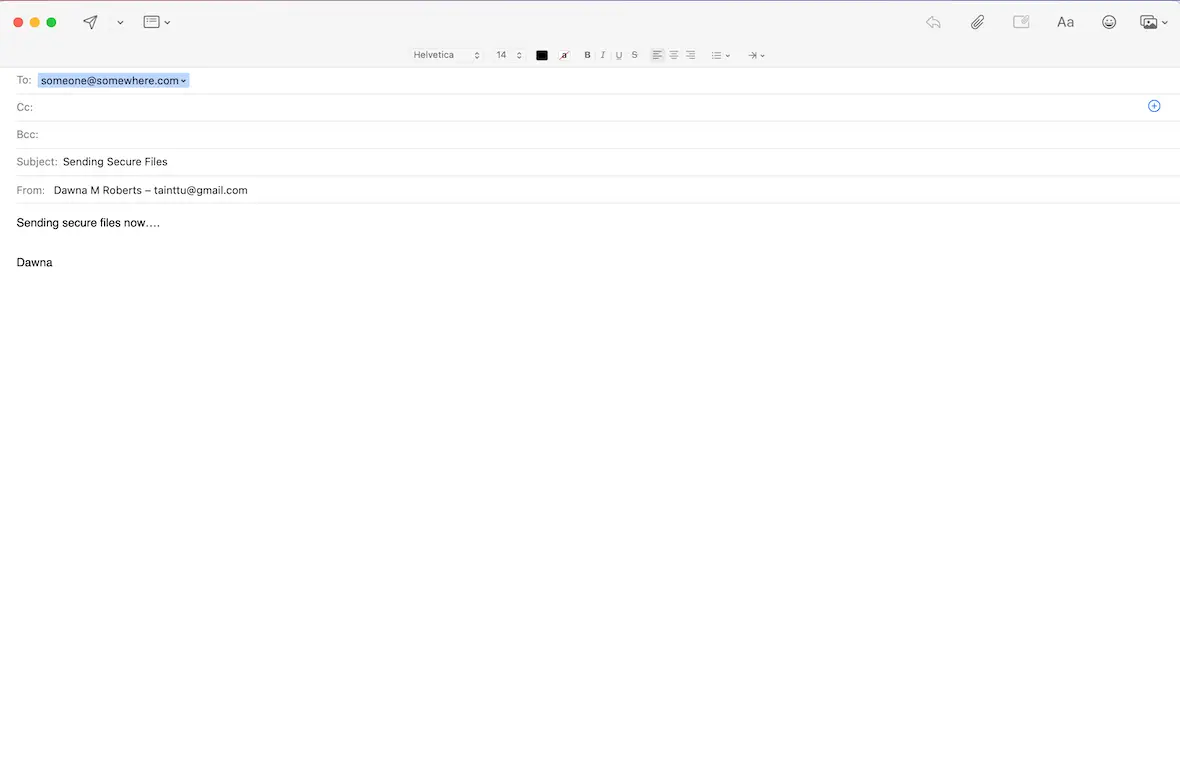
Email providers use TLS (asymmetric encryption) to keep incoming and outgoing mail safe.
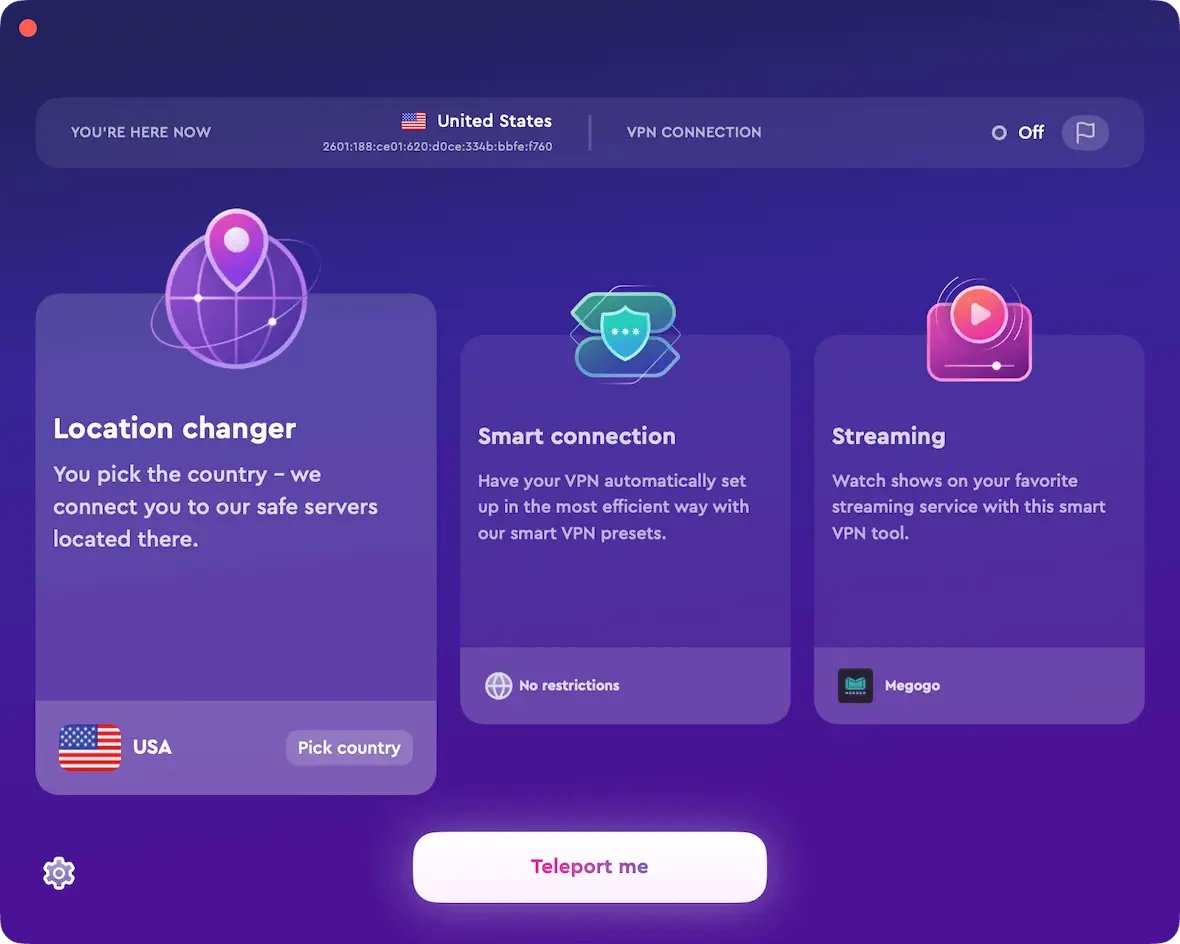
VPNs
VPNs are secured using asymmetric encryption to protect data in both directions and keep private information safe.
Banking
Much of the banking industry uses symmetric encryption due to its faster speed and performance. It is used to protect payment card transactions and identity verification.
Digital signatures
Asymmetric encryption is used for digital signatures to keep them as secure as possible and avoid corruption or interception.
Can you use both symmetric and asymmetric encryption?
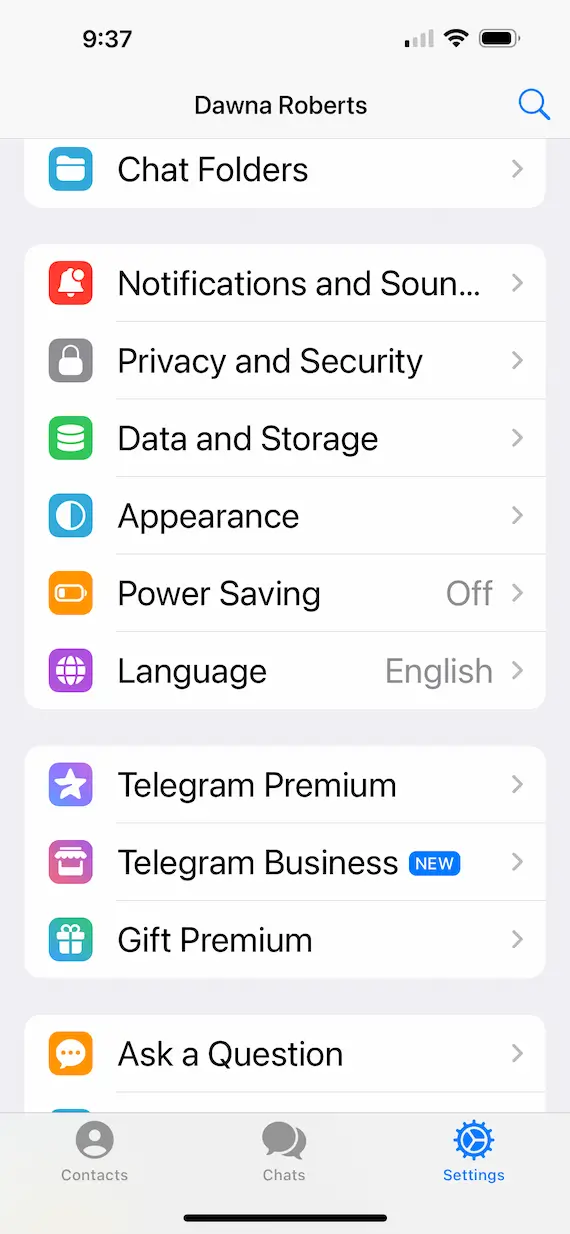
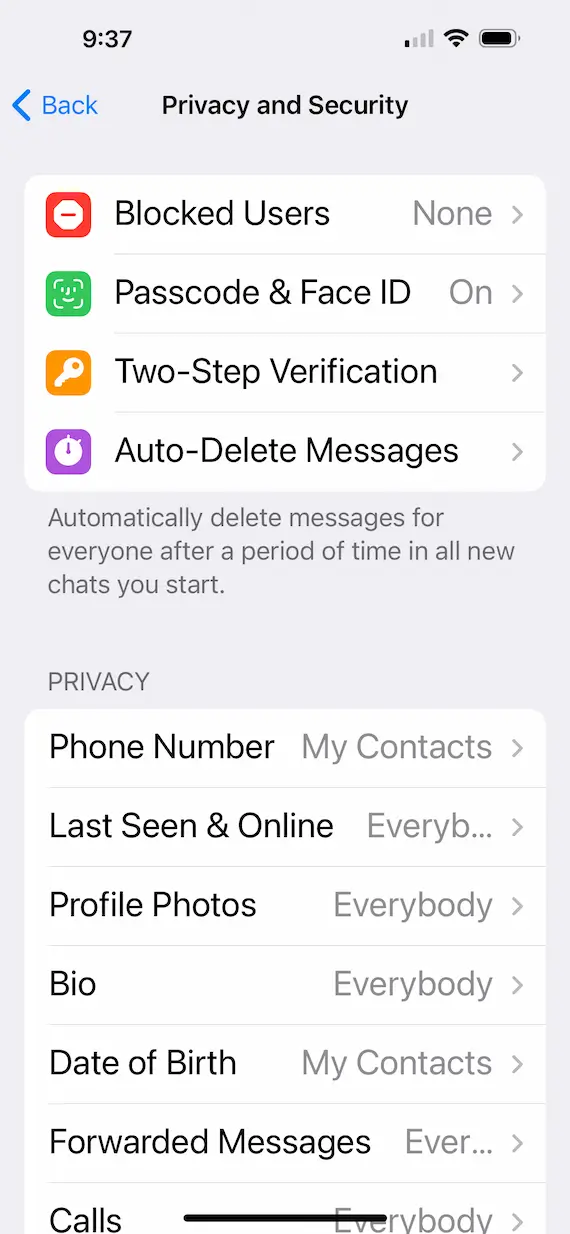
Many messaging applications, such as Telegram and WhatsApp, use both types of encryption simultaneously to keep data secure. Typically, Asymmetric encryption is used to initiate the connection between parties, and symmetric encryption then keeps the resulting data safe and ongoing.
These two types of encryption, symmetric and asymmetric, are used every day to keep your emails, files, and personal information safe. As you browse online, send and receive emails, and message friends, cryptography is constantly at work behind the scenes.