Not all skills used by hackers and cybercriminals relate to computing. In fact, when coding gets a hacker nowhere, they turn to a classic technique used by scammers and con artists: social engineering. There are several ways to trick people into giving out information, and vishing is an increasingly common one. So let’s dive deeper into vishing and learn how you can protect yourself from it.
What is the meaning of “vishing”?
The term “vishing” is a combination of “voice” and “phishing.” It is a social engineering technique that hackers employ when they need to get data or information from a targeted user.
Cybercriminals will call a victim and impersonate an organization like your bank, your work, or even law enforcement agents. Vishing attacks are rarer than phishing, during which millions of emails can be sent out, but they can reap more benefits for hackers.
In a vishing attack, black hat hackers usually target a specific person. Criminals will often do online research about the person they are calling beforehand. Or they may obtain some of the victim’s data through hacking or purchase on the dark web. For example, they might have your credit card number and ask you over the phone to corroborate your data. At the end of the call, after confirming the data they already know, they might ask you for your pin number, which they do not have.
Looking for new cyber knowledge?
The best defense against vishing is common sense and awareness of how these scams work.
The difference between phishing, vishing, and smishing
The cybersecurity industry often uses the word phishing to describe any attack, scam, or fraud perpetuated by criminals interacting with victims via email, social media, phone calls, or SMS. However, attacks done over email differ from those done over phone calls. Therefore, terms like phishing, vishing, and smishing are used to better categorize these threats.
Under this terminology, phishing refers strictly to attempts to steal data via email. Smishing is reserved for attacks done using SMS. And vishing is only used when hackers target victims via voice calls, including robocalls.
There are several other differences between the three besides the channel they use. The reach of the campaigns is the main difference. Email scams and spam phishing campaigns can target millions of users, often randomly or within an organization. By contrast, while SMS and robocalls can be automated for a broad reach, vishing and smishing often target specific individuals.
Another main difference is the technology each technique uses. In phishing, hackers use VPN programs to hide their location, bulk email senders, and email design apps to give their messages an authentic look. Smishing and vishing calls can employ automated technologies, but in many cases, they are executed manually by the hacker.
Finally, vishing sets itself apart because criminals get personal with the victim and have to use social skills to convince them. This requires the experience of an expert con artist. Only a master manipulator can convince victims to voluntarily give away data like passwords, pin numbers, bank data, and other information.
Examples of vishing attacks
Voice over IP, war-dialing, robocalls, and spear vishing are the main examples of how vishing attacks are done. Using Voice over IP, hackers can automate processes, hide their location, and make it difficult for law enforcement agencies to track them.
War-dialing
War-dialing was used in the past to locate computers connected to phones. Today, cybercriminals use this technique to get numbers and dial thousands of calls automatically. Combined with robocallers that are previously programmed, attackers can present a specific fraud to a wide range of people.
Spear vishing
Spear vishing is when hackers have done their research and know precisely who they are after. This is a common and popular vishing technique because it is so effective when properly executed. Hackers will pose as the IRS, your bank, or top-level executives from your work in order to convince you to take a specific action designed to either breach, damage, or steal data or financial resources. Spear vishing takes more time to develop but is considered a high-risk, high-return investment for cybercriminals, as they target victims with valuable data.
Caller ID spoofing
Caller ID spoofing is also used in vishing. Using specialized software, hackers can make their phone number appear as someone else’s number when it appears on your phone. Usually, they will spoof a phone number you know. This gives the call increased authenticity, as the number of an incoming call is the first thing one usually sees when answering the phone. Plus, it mitigates the chance of people screening their calls and lowers the possibility of the victim simply hanging up.
Finally, to create a sense of urgency and pressure, criminals may threaten a victim with possible legal action or claim that their accounts, funds, or data are at risk.
Common vishing themes used in calls include:
- Claims of compromised bank or credit card accounts
- Unsolicited loan or investment offers
- IRS tax scams
- Medicare or social security scams
- Lottery winner scams
- False requests from the victim’s workplace
- False requests from cybersecurity teams
- Tech support impersonation
- Bank impersonation
- Telemarketer impersonation
- Tech sales
- Computer virus threats
How to spot a vishing attack
There are several ways to quickly identify if you are being targeted in a vishing attack. Remember, common sense and relying on your gut feeling are your best allies here.
The caller asks for personal data
Always remember that law enforcement agencies, government organizations, and financial institutions will never ask you for personal information via phone. So if someone calls you asking you to verify your information and claims they need your password, social security number, or card PIN, never give it to them.
The caller creates an irrational sense of urgency
To persuade you to take action, criminals often create elaborate fictional scenarios that build a sense of urgency. The urgency is only there to give you less time to think about what the scammer is asking you to do. Always remain calm, no matter how urgent a phone call may seem to be.
The caller threatens you with legal action
Another classic technique hackers use to rush you into giving away data is to threaten you with legal action. A caller might claim that your credit card has been stolen and used for criminal purposes. Or they may claim they are from the IRS and that an error has occurred, which you need to correct to avoid legal action. Once again, no matter how elaborate a plot may sound, never give your data to anyone.
Caller ID is blocked or unknown
Before, during, and after a suspicious call, always check the number. Criminal organizations can use several tools to hide their location. And while an incoming number may appear to be from within the US, some may be operating from abroad. Nevertheless, a phone number can tell you a lot.
Do you recognize the phone? What area code is it? Is it blocked? Has your cell phone alerted you that the call is possibly spam or dangerous? Legitimate calls from real organizations and real people will not appear blocked, flagged, or have odd numbers.
A call comes out of nowhere
If you receive a phone call during strange hours — for example, someone from a bank during non-working hours — or if you get a call that surprises you from a company or organization that never calls you, be suspicious. While hackers will try their best to mask their vishing campaigns as everyday events, trust your instincts. You will often know when something is wrong.
The caller offers prizes, gifts, or other freebies
It is true that some people do win the lottery. And a lucky few really are sent gifts or given a significant discount on their next vacation. But the chances that this happens to you out of the blue are slim. If a call sounds too good to be true, it likely is. Unfortunately, free coupons or claims that you have won a prize are among the most popular and effective types of robo-vishing calls. These scams trick victims by the thousands every year.
How to prevent vishing
There are several things you can do to avoid getting hit with a vishing call or shutting it down as soon as it begins.
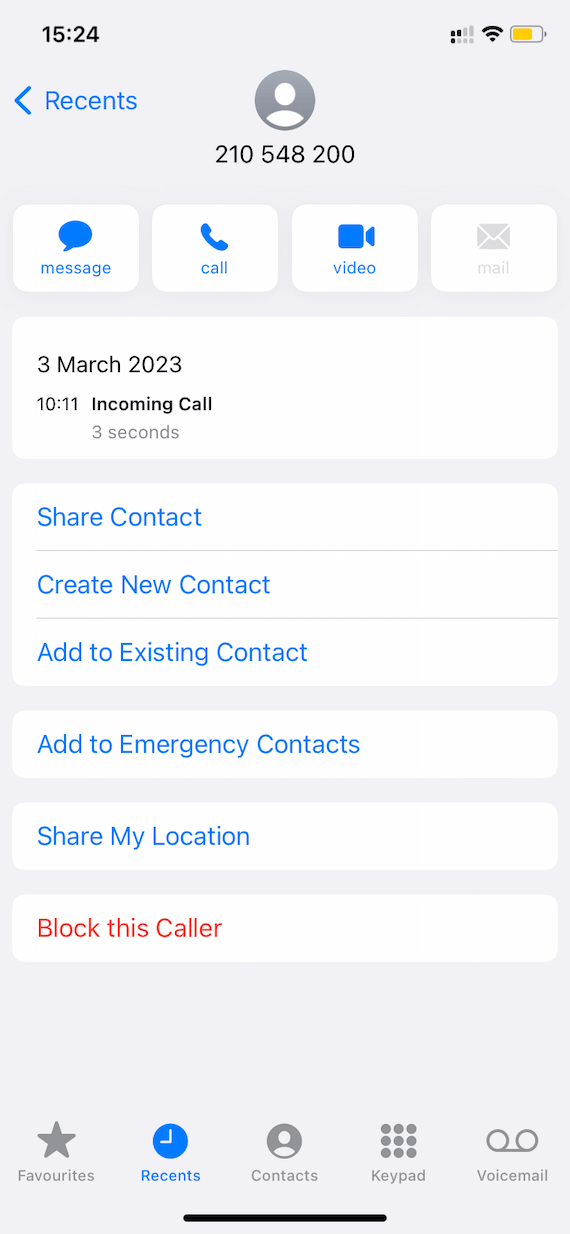
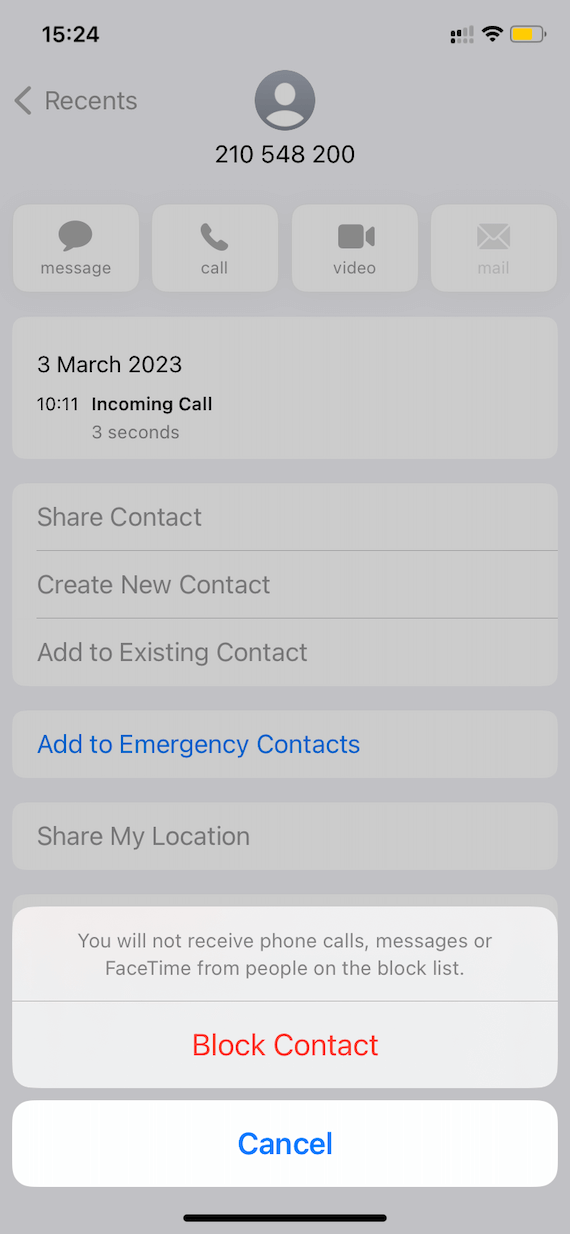
Hang up, block, and report
If someone calls and asks you for personal data or if something sounds suspicious, do not engage in a conversation. Hang up the phone, block the call, and report the caller.
Don’t take calls from unknown numbers
Even better than hanging up on a stranger is never talking to one in the first place. Screen your calls. Only take calls from contacts you know or are expecting. If an unknown number calls you, let it go to voicemail and see what they have to say. Then decide if you want to return the call or not.
Don’t share your phone number online
Hackers can get your phone via automated or targeted online searches. Never post your phone number on your social media or online. Protect your privacy as much as you can. When it comes to personal data, it can be used against you in an attack.
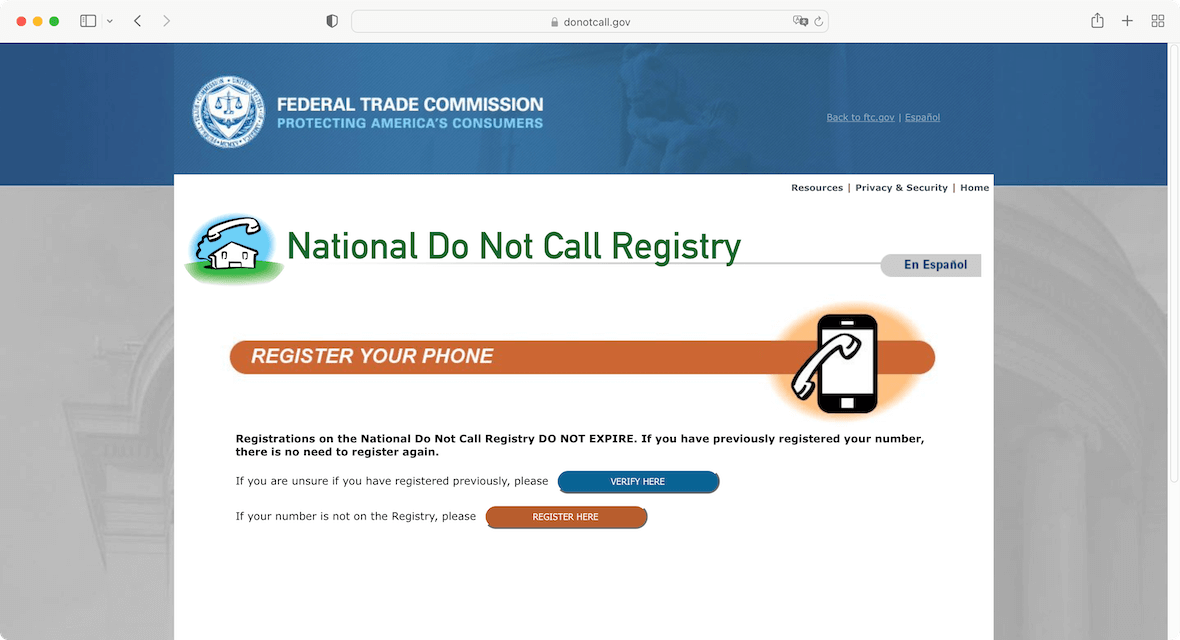
Join the Do Not Call Registry
If you live in the US, you can join the National Do Not Call Registry. This registry is a database managed by the federal US government. Listing your phone on this site drastically reduces the chances of being called by telemarketers and robocallers.
Never buy anything over the phone
You might be tempted to buy something over the phone using your bank information, credit card, or debit card. However, paying over the telephone requires that you input all the data a hacker needs to steal your money. And even with automated payment systems, don’t buy things over the phone.
Don’t press buttons, click links, or download anything
A caller may try to convince you to head to an official-looking website, click on a link they send you via SMS, or run you through automated phone systems. When dealing with suspicious calls, don’t press any buttons except the one required to hang up. And never click on links or download anything. These can be gateways for malware designed to steal your data, spy on you, or breach your system and devices.
Vishing may sound like something you would never fall for, but it is commonly used because when the time comes, many people go straight into the con’s play. Like any other cybersecurity threat, vishing can happen to you. Fortunately, it is easy to deal with if you have the right information and know what to do.