Once again, cybersecurity researchers have identified sites impersonating DeepSeek for malicious purposes. For the past months — since the Chinese AI DeepSeek jumped to international fame — scammers, phishing actors, and malware distributors have been abusing the brand’s popularity to drive their cyberattacks.
Malwarebytes recently warned that the trend of targeting DeepSeek users is still active, with a new campaign distributing trojan malware through a fake site. Moonlock followed up on this investigation and found that Google Ads platforms are once again running malicious and risky ads.
Malwarebytes identifies another malicious DeepSeek impersonator
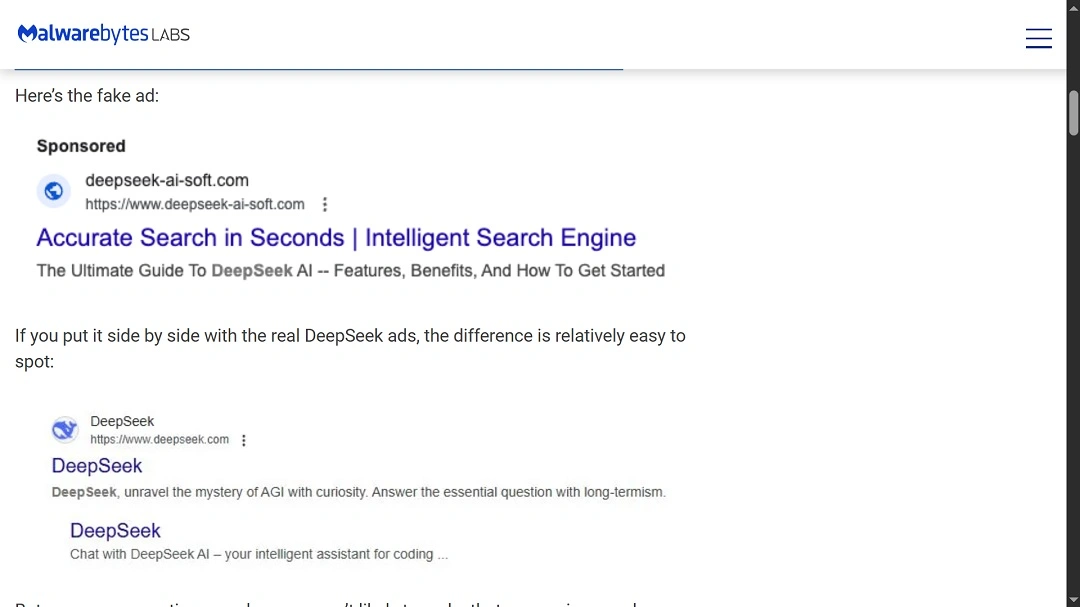
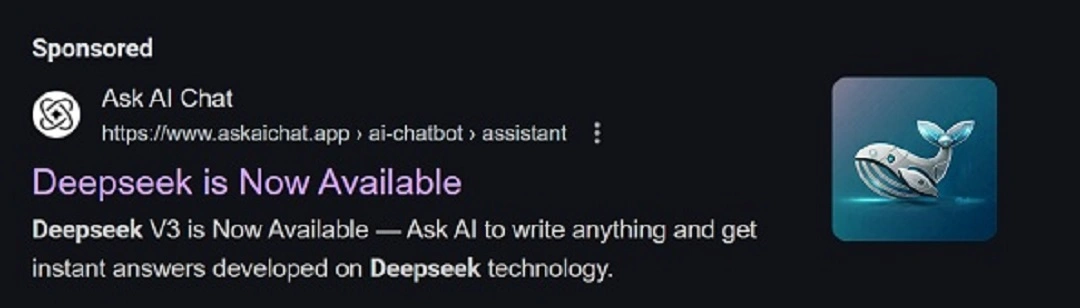
Recently, Malwarebytes’ Senior Director of Research, Jérôme Segura, identified a new campaign impersonating DeepSeek to distribute malware. Segura uncovered that the threat actor was abusing Google Ads platforms to deliver top-of-page, web-sponsored fake ads that redirect users to malicious DeepSeek impersonation sites.
Malwarebytes said that the privacy and cybersecurity questions that the AI startup DeepSeek has faced due to its ties to the Chinese government and how it shares data with it aren’t the only serious problems emerging from this AI global war.
“Cybercriminals are also using it (DeepSeek) as a lure to trap unsuspecting Google searchers,” Malwarebytes said.
In the report, Malwarebytes identified the site www.deepseek-ai-soft[.]com as a well-crafted fake domain that was being promoted through the Google Ads platform.
Clicking on the download link on that website triggered a trojan programmed in Microsoft Intermediate Language (MSIL): Malware.AI.1323738514.
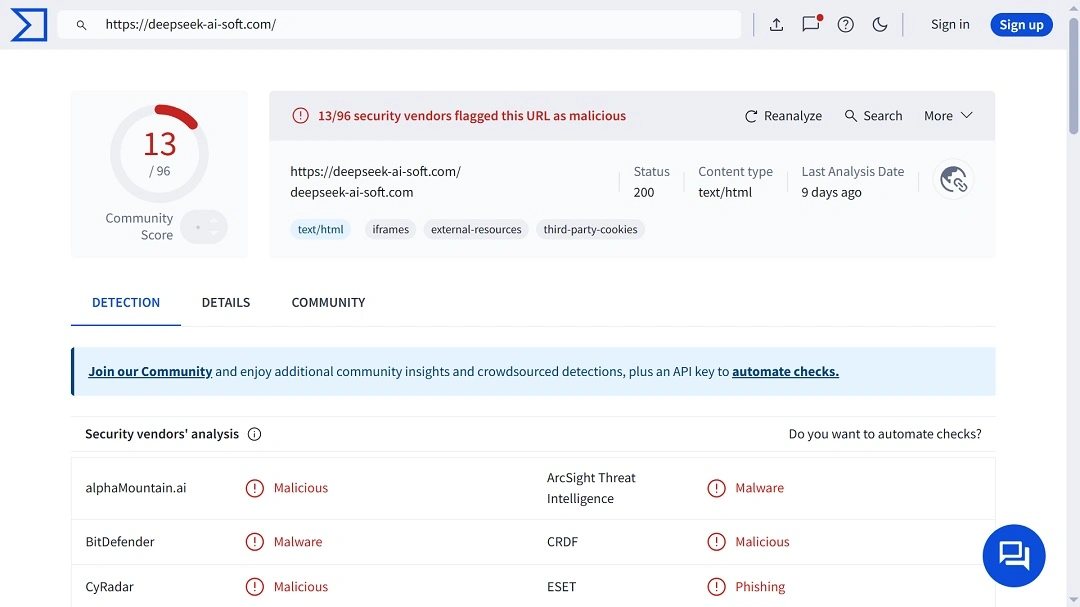
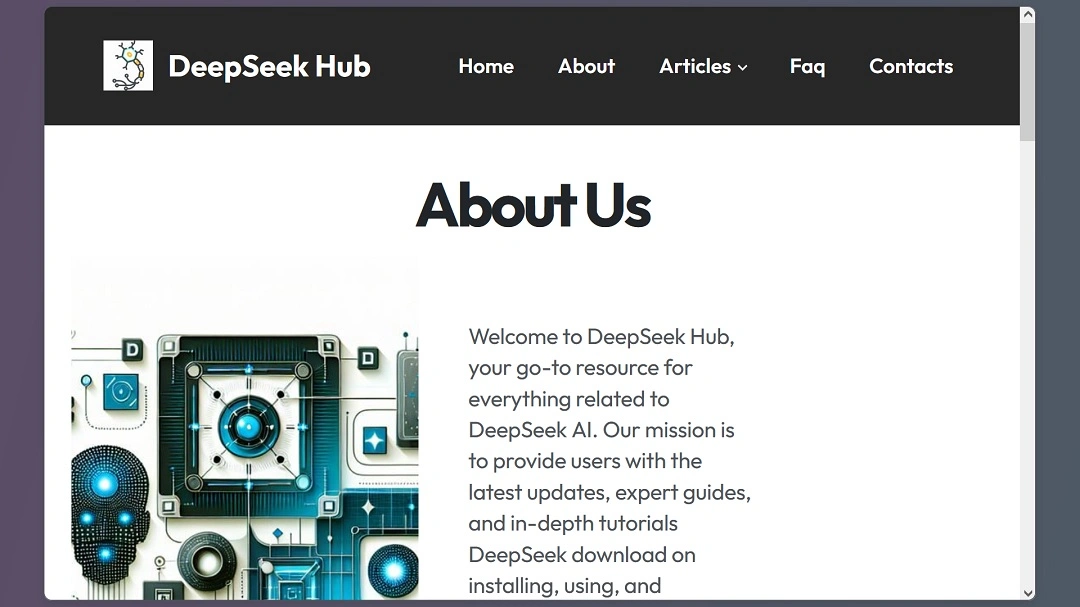
Moonlock checked the site a couple of days later and found that the download link had been removed, and the site had been updated to appear as a DeepSeek “community” site, offering no download. This modification of the page is likely due to the exposure of the report issued by Malwarebytes.
DeepSeek’s popularity leads to a wave of fake and fishy sites
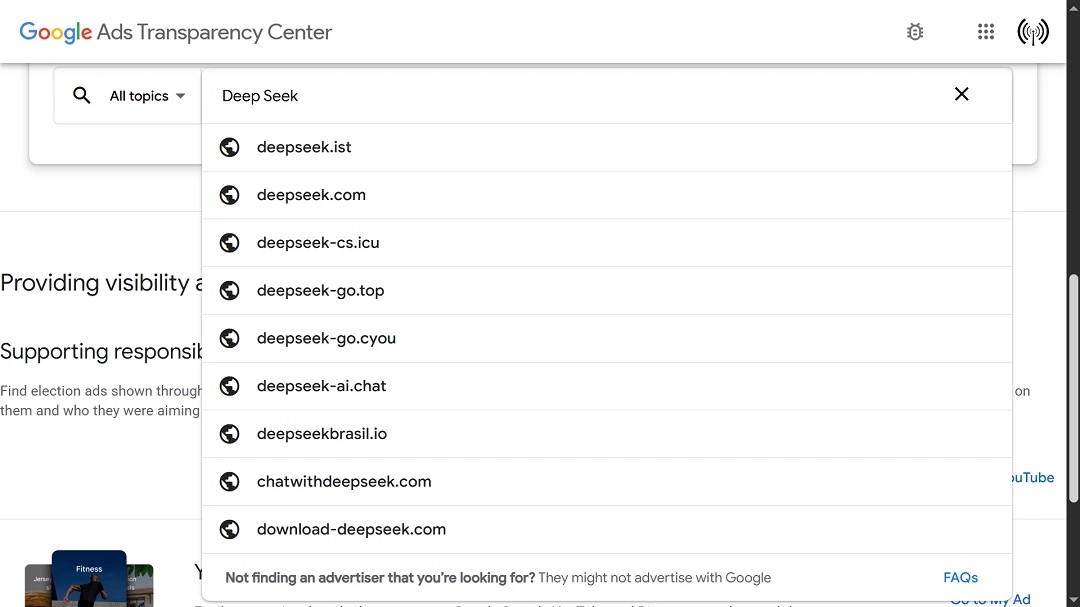
Moonlock’s search on Google Ads Transparency Center and other resources revealed that there are a number of organizations or individuals running DeepSeek ads via the Google Ads Platform that are not connected in any way with the legitimate DeepSeek.
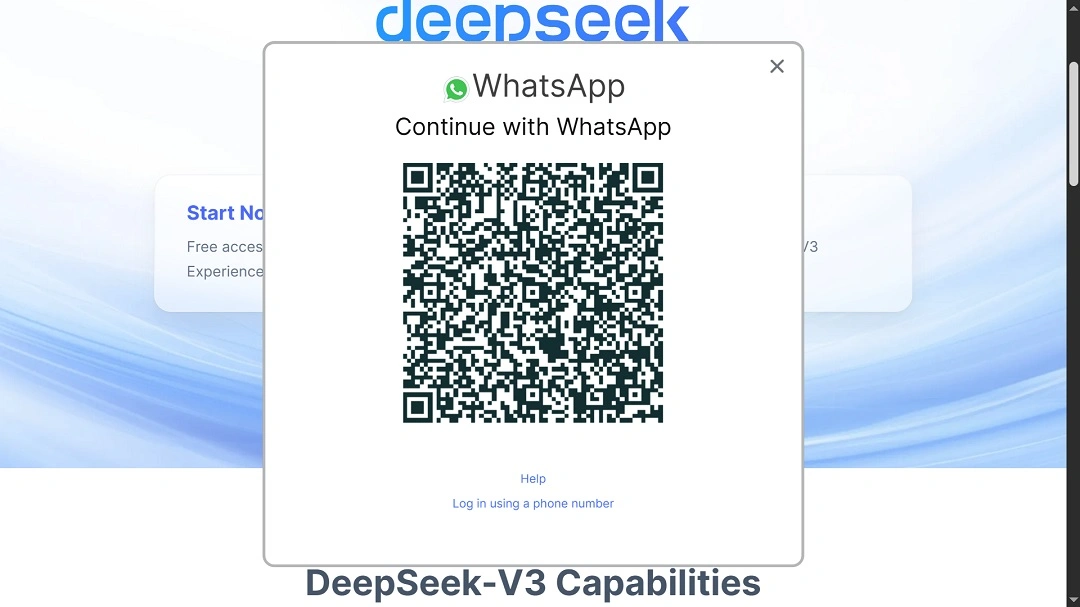
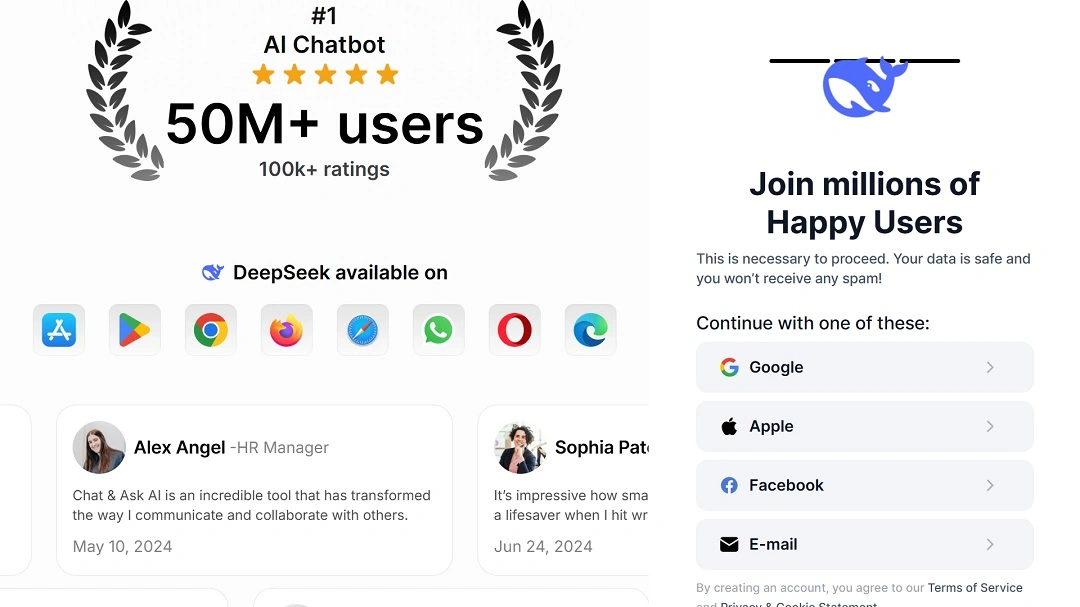
While not all of these sites are malicious, they still pose risks for users. Moonlock found several online DeepSeek community sites that offered DeepSeek downloads but requested that users link their WhatsApp with fishy QR codes. Others asked users to log in using Google or Apple account data.
There are also several online sites that are capitalizing on the success of different AI models and allow users to chat with different models. These sites integrate all of these models into the same service. However, it is difficult to assess just how safe these multi-model chat sites are. One thing is certain: They are rising in great numbers.
It’s open season for cybercriminals abusing AI popularity
Earlier this year, in February, cybersecurity researchers uncovered a multitude of fake, malicious DeepSeek sites. Researcher Dominic Alvieri tracked over 50 active websites that posed a threat to users.
That same month, Zscaler researchers found a DeepSeek-themed malware campaign that used clipboard injection to deliver malicious PowerShell commands, ultimately deploying the Vidar information stealer. The Vidar stealer is a Windows stealer that is often distributed by threat actors along with the Lumma stealer to target macOS users.
In the campaign discovered by Zscaler, threat actors used legitimate platforms like Telegram and Steam to set up their command-and-control (C2) communication servers. This is where they extracted the data from victims.
To understand the volume of the DeepSeek impersonation trend, we share Zscaler’s IoC lists of domains, plus some new sites:
- presales-deepseek[.]com
- www.deepseek-ai-soft[.]com
- deepseakr[.]com
- deepseekpg[.]bet
- deepseekaiagent[.]live
- deepseekjulebu[.]shop
- deepseekr1[.]club
- deepseekonchain[.]com
- deepseek-v3[.]xyz
- deepseek-pro[.]cloud
- deepseekai[.]club
- deepseekpepe[.]site
- deepseekai[.]global
- deepseekpepe-eth[.]com
- deepseeksol[.]com
- trydeepseek[.]com
- sale-deepseek[.]com
- deepseekpumpfun[.]com
- deepseektrump[.]xyz
- deepseekaiclaim[.]live
- deepseek2025[.]xyz
- deepseekfree[.]xyz
- deepseekai[.]today
- deepseek-adverting[.]icu
- deepseekclaim[.]live
- deepseekt[.]org
- deepseek-trump[.]xyz
- deepseek4youtube[.]com
- deepseekaigames[.]site
- deepseek[.]express
- deepseeksky[.]com
- deepseekfart[.]xyz
- chatdeepseek[.]app
- deepseekaieth[.]com
- deepseekcaptcha[.]top
- deepseek[.]top
- deepseekai-eth[.]fun
- deepseek[.]app
- deepseek[.]art
There are several threat combinations that threat actors who run these types of impersonation campaigns can deploy to steal user data. This includes running malicious scripts, offering QR codes, fake login, fake CAPTCHAs, and guiding users to specific ways to download malware and bypass security controls.
How to protect yourself against DeepSeek and other AI impersonators
If you are looking to chat with different AI models, we recommend Duck.AI, a service created and managed by DuckDuckGo, a web browser focused on privacy and security. On Duck.AI, users can chat safely with Mistral Small 3, o3-mini, Claude 3 Haiku, Llama 3.3 70B, and GPT-4o mini.
Naturally, we recommend that you do not provide information or link your messaging apps to any site to download DeepSeek. We also strongly urge all users to download a respected and trusted ad blocker and integrate it as a browser extension.
Because Google Ads platform abuses have been ongoing for years, with little to no action from Google itself to moderate these malicious ads, the only advice we can offer is to never click on a Google Ad, no matter how legitimate it seems to be.
Links on Google Ads can even display the correct URL address but redirect users to a different domain when they click on it.
Malwarebytes seems to share our recommendation regarding Google Ads.
“Unfortunately, we are getting so used to sponsored Google search results being abused by criminals that we advise people not to click on them,” Segura said.
If you are thinking about downloading the DeepSeek app, we recommend that you only do so through official app stores, official download links, or open-source verified sites.
Final thoughts
DeepSeek’s popularity will continue to be exploited by cybercriminals. Users should take preventive measures, making sure they do not fall into the malicious AI ecosystem that is growing day by day.
The solution is simple and lies on the user’s end. Don’t click on sponsored ads. Get a professional Ad Blocker and only download AI from official channels.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Google LLC. Google Search and Google Ads are trademarks of Google LLC.