While software, web, apps, and API exploits rely entirely on malware and malicious content to launch attacks, hardware vulnerabilities can be more dangerous, as they cannot be virtually patched so easily.
Researchers from the University of Illinois Urbana-Champaign, the University of Texas at Austin, Georgia Institute of Technology, the University of California, Berkeley, the University of Washington, and Carnegie Mellon University recently released the findings of their GoFetch attack.
The GoFetch attack exposes vulnerabilities in Apple’s M1, M2, and M3 chips. These vulnerabilities are unpatchable and allow attackers to extract secret cryptographic keys and steal sensitive data from Apple users.
GoFetch attack key takeaways and findings
Modern processors like the M-series chips of Apple use caches — temporary storage areas for data that’s used frequently. Caches make programs run faster and reduce latency.
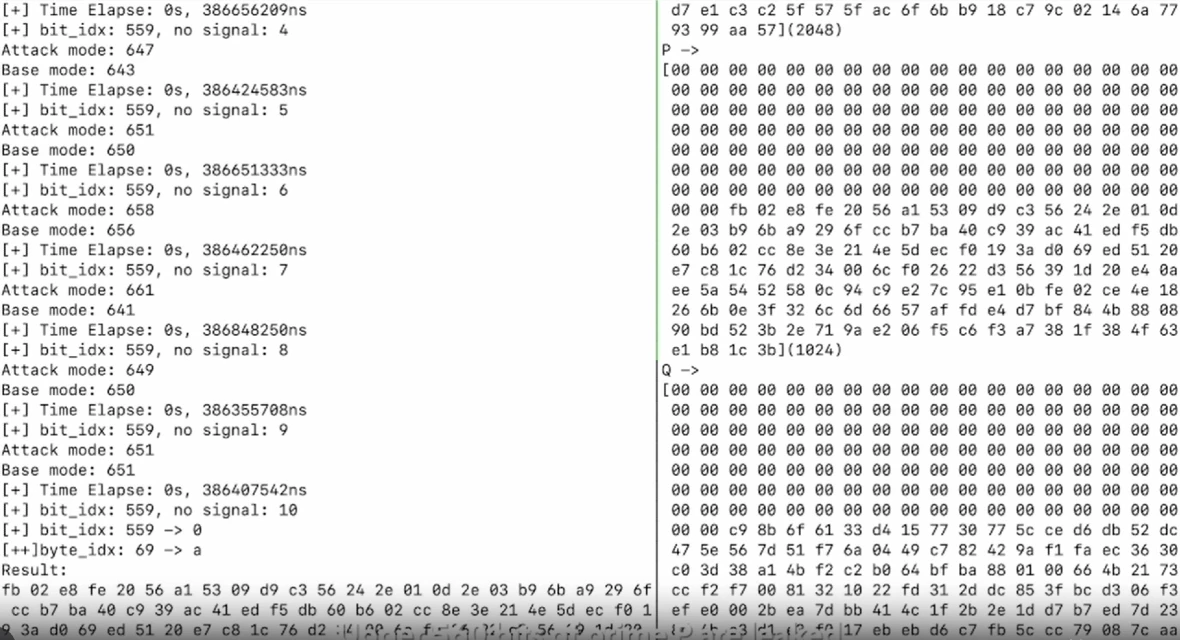
The GoFetch attack, which researchers disclosed to Apple in December 2023, proves that the design of the Apple M chips breaks a vital rule in programming by mixing data with memory access patterns.
“Attackers co-located to the same machine can monitor the cache’s state to deduce a victim’s access pattern,” the researchers said.
Breaking down DMP vulnerabilities in Apple M-series chips
The GoFetch attack is based on a CPU feature called data memory-dependent prefetcher (DMP), present in the latest Apple processors.
Using this CPU feature can exploit the system and steal secret keys from devices with Apple M-series processors.
Here’s a breakdown of the key points:
- Type of attack: The attack is a microarchitectural side-channel attack. This means it takes advantage of the unintended consequences of how the processor itself is built to leak information.
- Target: The attack specifically targets the secret keys used in cryptographic implementations. These keys are crucial for securing information, so if stolen, it could allow access to encrypted data.
- Method: As previously mentioned, the attack leverages data memory-dependent Prefetchers (DMPs) present in Apple M-series CPUs. DMPs are a performance optimization feature, but GoFetch exploits them to influence how the CPU accesses data and steals information about the secret keys.
- Impact: The researchers were able to use GoFetch to steal keys from various cryptographic libraries and implementations, including OpenSSL Diffie-Hellman, Go RSA, CRYSTALS Kyber, and Dilithium.
What types of data and processes does GoFetch comprise?
Overall, GoFetch is a serious vulnerability that undermines the security of cryptographic operations on Apple M-series processors. Let’s dive deeper into the cryptographic libraries and implementations that this attack targets to understand what’s at stake for Apple users.
GoFetch compromises OpenSSL Diffie-Hellman, a widely used protocol for establishing a secure communication channel between two parties. OpenSSL Diffie-Hellman allows users to agree on a secret key without exchanging it directly over an insecure network.
In contrast, Go RSA, also impacted by the attack, refers to the implementation of the RSA encryption algorithm written in the Go programming language. RSA is another popular public-key encryption scheme used for secure communication and digital signatures.
Thirdly, the compromised CRYSTALS-Kyber and CRYSTALS-Dilithium resources are relatively new post-quantum cryptography (PQC) algorithms. PQC algorithms are designed to be secure against attacks from quantum computers, which pose a significant threat to traditional cryptography like RSA in the future.
Data that can be stolen using GoFetch
If the cryptographic operations detailed above are compromised, attackers can gain access to the “keys” that unlock that data.
This means the attacker can steal or access:
- Encrypted files
- Encrypted communications
- Password managers
- Encrypted disks
- Locally stored backups
- Cryptocurrency and digital wallets
- VPN connections
- Web browser extension data
- User data (including financial data)
Limitations and challenges of the GoFetch attack
Unlike malware or cyberattacks discovered in the wild, exploitations such as GoFetch, developed by the academic community, tend to be complex to execute.
Cybersecurity studies and trends reveal that cybercriminals generally prefer to take the easiest way into a system. This is why fileless attacks (using stolen credentials bought on the web), malware-as-a-service (buying malware and support to launch attacks), and phishing are among the top criminal trends. These popular hacking techniques require fewer technical coding skills and less investment, and they are not as time consuming as others.
Additionally, academic research on cyberattacks and vulnerabilities often reverse-engineer hardware and software. This technique requires advanced technical skills and access to specific resources and components.
Furthermore, the GoFetch attack requires an established level of access to an M-chip-powered device. This means the attack requires direct access to the hardware itself and cannot be executed remotely.
To run this attack, criminals also need to master cryptography and hardware, as well as the skills to code data that can manipulate the cache and its behavior, forcing the cache to leak secret key bits.
How to mitigate the risks
While the GoFetch attack exploits a hardware vulnerability in certain Apple M-series processors (M1, M2, M3) and potentially Intel’s Raptor Lake chips, there are steps you can take to mitigate the risk.
Keeping your software up to date is crucial. Software updates often include security patches that address vulnerabilities. Make sure you install updates for your operating system, web browser, and other applications as soon as they become available.
Additional measures can be implemented for developers of cryptographic libraries. In some processors, setting the DOIT or DIT bit can disable the data memory-dependent prefetcher (DMP) that the GoFetch attack exploits. Additionally, a technique called input blinding can be used in certain cryptographic schemes. This helps prevent the creation of intermediate values that an attacker could manipulate to leak secret key bits.
Another way to reduce the risk is to avoid sharing hardware with untrusted users. Since GoFetch likely requires some level of access to the system, this makes it more difficult for attackers to launch an attack remotely.
By following these recommendations, you can help protect yourself from attacks and keep your data secure. It’s important to note that researchers are continuously working on improving security measures, and new techniques may emerge in the future. Staying informed about the latest security threats and updates is an ongoing process.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Apple Inc. Apple is a trademark of Apple Inc.