In yet another creative move, cybercriminals have found a way to leverage Google’s free services to target victims. Avanan, a CheckPoint company, has released the findings of a new investigation uncovering how cybercriminals are using Google Looker Studio and Google Slides to initiate and launch attacks.
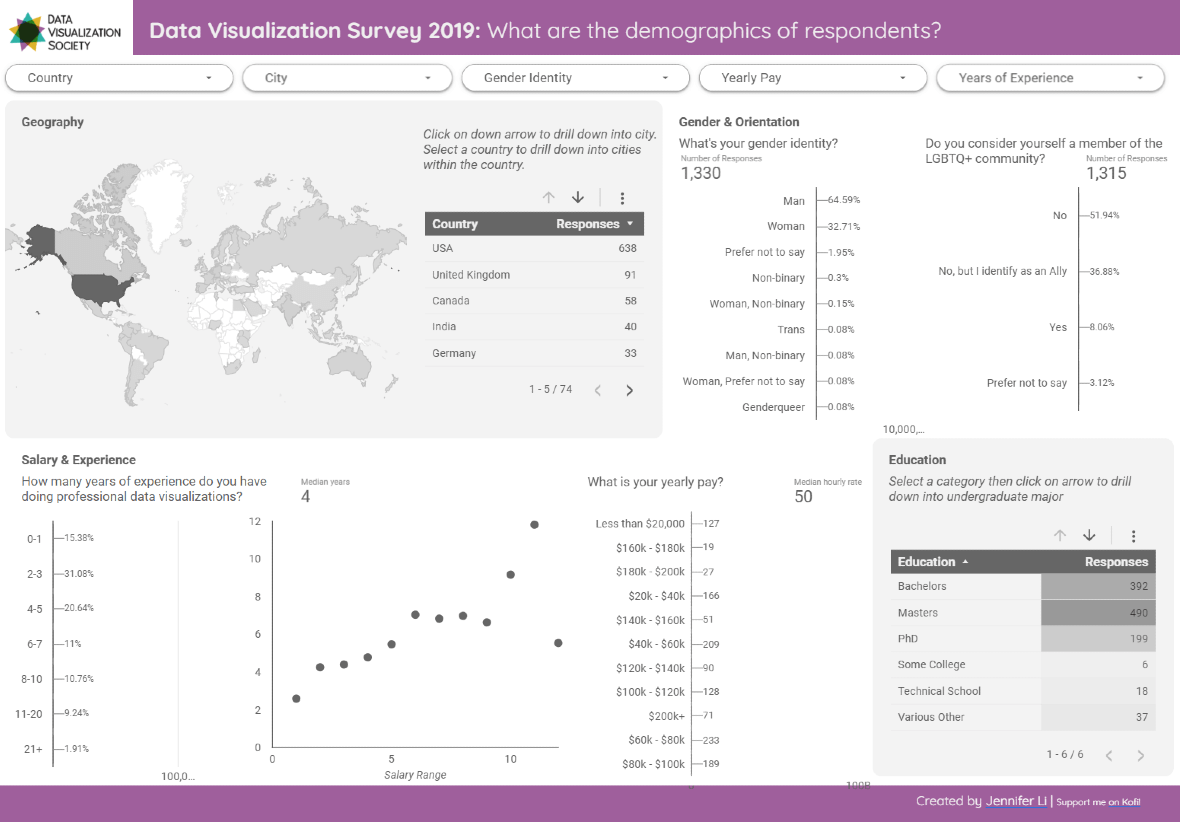
Similar to Google Slides, Looker Studio is a free data visualization tool used to create and share presentations. Now, malicious hackers are creating fake presentations with the tool and then sending out emails designed to steal credentials. Let’s break down how these attacks work and what you can do to stay safe.
How Google Looker Studio attacks play out
Understanding how Google Looker Study attacks work is the best way to avoid falling for this scam.
This is how the attack works:
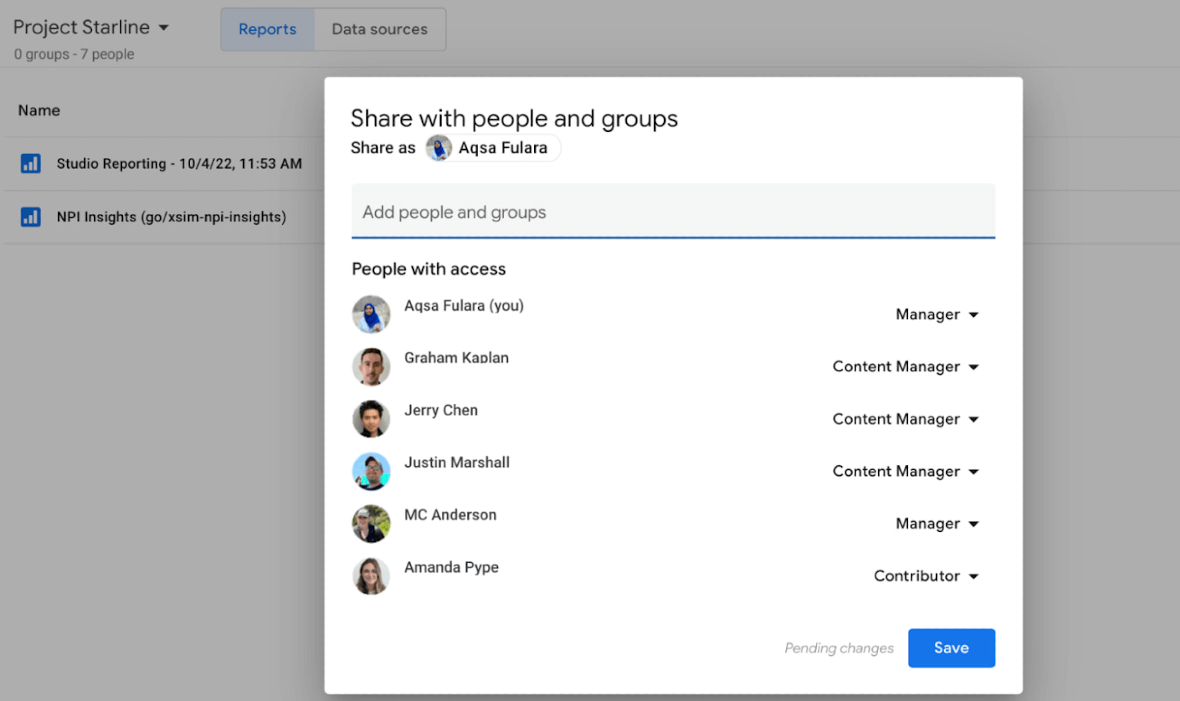
- Cybercriminals create a free Google Looker Studio or Google Slides account and build content designed to convince victims. Usually, they design some sort of fake financial project (blockchain or crypto-related).
- Once the content is created, bad actors use a Google Looker feature that allows them to share the presentation with potential victims via email. Because the email comes from Google, it lands directly in your inbox, bypassing security filters without being flagged as a suspicious message.
- A victim opens the email, suspecting nothing, as the email sender is Google. The email contains a message inviting the victim to check out the Google Looker Studio presentation, again convincing them that they will be financially benefited.
- The victim clicks to view the Google Looker Studio or Google Slide presentation, which itself is legitimate. But somewhere within it, a malicious link is hidden.
- When users click on the link, they are asked to log in to their account. It’s at this point that the malware instantly steals their credentials.
Why is the Google Looker Studio attack so dangerous?
This newly discovered vector of attack is dangerous because, unlike other attacks that use email or messaging to guide victims to malicious sites, this one is launched and executed using legitimate Google services.
Traditionally, experts advise users to look closely at the email address or at the URLs to keep them safe. But this advice can be thrown out the window in this case, as both the email and the URL are from Google itself. As a brand, Google is widely trusted. Thus, users are unlikely to be suspicious of an email that has been sent by Google.
Criminals are neither hacking a Google account nor spoofing a Google site. Instead, they have simply found a security weakness that they can use to their advantage.
Do this to protect yourself from the Google Looker Studio attack
You may be wondering, if the email comes from Google and the URL is from them too, how can you see this attack coming? How do you take action before the damage is done?
Fortunately, there are several things you can do. First of all, you now know that these platforms are being used by cybercriminals. So, if you get an email inviting you to view a Google Looker Presentation or Google Slides document and you don’t use these platforms, do not click on the link. You should also report the email.
On the other hand, if you do use these Google platforms and you receive a link, ask your colleagues, family members, or friends if they have sent you the invitation before you open it.
How to spot a Google Looker Studio scam
Fortunately, despite the apparent legitimacy as a Google service, there are ways to spot this scam.
The examples that Avanan released in their investigation prove that although cybercriminals may be skilled in using these Google services, their emails are not very realistic or convincing.
Emails from attackers will usually start by claiming that you have an open crypto account that you haven’t logged in to for some time. They will then try to convince you that during the time that you were logged out of the account, you generated substantial gains. This is a dead giveaway. If a message sounds too good to be true, it probably is.
It’s important to note that there is no danger in opening these types of emails or even viewing the presentations. That said, interacting with them is not recommended. The danger comes when you click on the malicious link that is embedded within the Google presentations. Follow the advice in this article, and you will stay safe.