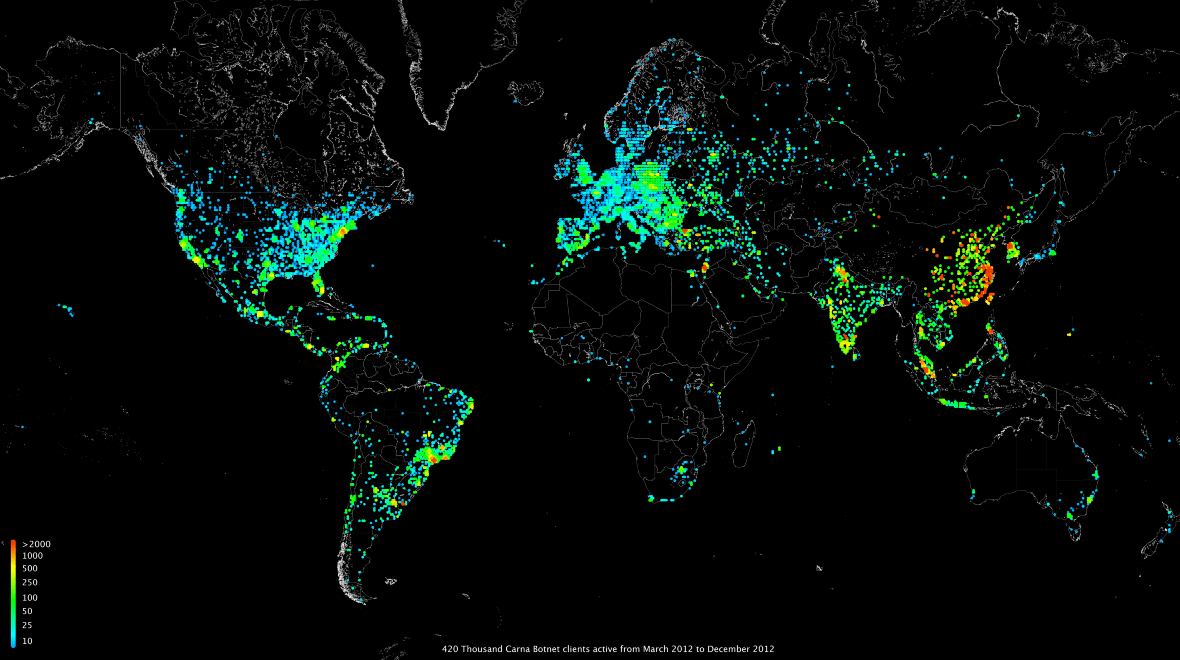
It’s been about two months since the Qakbot crackdown and what the FBI called the largest-ever U.S.-led international enforcement cyber takedown. But now, not only are two new malware botnets rising, but they act very much like Qakbot itself.
On August 29, the FBI announced that through an effort in coordination with international law enforcement, the Qakbot botnet infrastructure was shattered. The Qakbot botnet infected more than 700,000 computers and is reported to have collected at least $59.13 million in paid ransomware since 2007. But like most things in cybersecurity, when one attacker network goes down, one or two more emerge to take its place.
On November 20, Cofense reported that a new malware phishing campaign spreading DarkGate and Pikabot malware is now the most advanced active phishing campaign in the threat landscape. While there is no definitive evidence linking DarkGate and Pikabot to Qakbot, Cofense argues that the similarities are many.
Copycats? Or criminals that slipped through the FBI’s cracks?
Cofense explains that coincidentally, DarkGate and Pikabot emerged just as Qakbot activity was last seen. In a copycat style, the criminals behind this campaign use the same techniques that Qakbot used. They also seem to have picked up a new trick or two, leveraging new evasive tactics and anti-analysis techniques.
“This campaign disseminates a high volume of emails to a wide range of industries, and due to the loader capabilities of the malware delivered, targets can be at risk of more sophisticated threats like reconnaissance malware and ransomware,” Cofense said.
As mentioned, Cofense did not directly tie the new campaign to Qakbot. However, it did point out several similarities. If, indeed, DarkGate and Pickbot are the evolution of Qakbot, this would imply one of two things. Either cybercriminals linked to Qakbot are behind this new attack, or another group or groups have found inspiration in the recently infamously brought-down criminal network.
One thing is certain: Botnet malware since the raid has evolved, has improved, and is out in the wild wreaking havoc again.
Similarities between DarkGate, Pikabot, and Qakbot
Cofense says that Qakbot activity was last reported toward the end of June, while DarkGate emerged during July. But this is not the only coincidence they found.
Qakbot, DarkGate, and Pikabot both use:
- Hijacked email threads as the initial infection
- URLs with unique patterns that limit user access, usually limiting browser and regional location
- An infection chain nearly identical to what we have seen with Qakbot delivery
- Loaders (a loader is the software that drops the actual malicious content on the system)
- The capacity to add additional malicious payloads to unknown infected machines
This is how DarkGate and Pikabot operate and breach your device
Users around the world are becoming more aware of the techniques used in phishing emails, SMS, voicemails, and other types of communication scams and attacks. Responding to this trend, criminals are forced to level up their game, creating new ways to convince victims to download a malicious file or navigate to an unknown URL.
And that is what DarkGate and Pikabot do. They are considered high-level threats due to the level of sophistication of their tactics, techniques, and procedures (TTPs). Not only have they refined their phishing methods, but they have advanced their capabilities to deliver malware once the victim falls for the bait.
What is email thread hijacking, and why should you care?
To convince potential victims, DarkGate and Pikabot attackers are using email thread hijacking. Email thread hijacking is a technique where legitimate email conversations are intercepted and hijacked. The criminals then add malicious attachments or URLs to ongoing email threads.
Email thread hijacking is extremely effective for a simple reason. While users are told to be extra cautious when engaging with unknown or non-verified sources and emails, they are hardly ever warned that a phishing email may, in fact, be an existing threat that comes from within.
In email threat hacking, you might be talking to a business, a colleague, or even a friend and family, sending emails back and forth. And while the first couple of email exchanges may be legitimate, at some point, criminals can take over the conversation.
“The attackers hijack an existing email thread and carry on the conversation, injecting malware-laden attachments or URLs,” Cofense said, adding that leveraging the Microsoft Exchange Server vulnerability CVE-2021-26855, they were impersonating administrators.
However, email threat hijacking is not unique to DarkGate and Pikabot. In fact, this technique is considered one of the key signatures of Qakbot. Additionally, like Qakbot, this new campaign inserts URLs into hijacked emails that Cofense describes as “more than your average phishing URL.”
The URL links they insert add layers that help bad actors evade detection, narrow down targeted regions, and better control the attack. Layers added to these malicious URLs include the exclusive use of Google Chrome as a web browser to open the link and a location filter set to the U.S. — only those in that region can open the link.
The infection chain
According to Cofense, DarkGate and Pikabot attackers have been testing out different infection methods. Still, a preferred infection chain was identified.
The chain works as follows:
- An email threat is hijacked to bait users into clicking on an inserted malicious URL with added layers.
- Once the victim clicks on the URL, a ZIP archive is downloaded. (The ZIP archive contains a JS file, which is a JavaScript application used to reach out to another URL to download and run malware).
- Once this happens, the user has been successfully infected with either the DarkGate or Pikabot malware.
What can DarkGate and Pikabot do?
DarkGate and Pikabot malware are extremely dangerous and versatile. They can pull off all kinds of nasty tricks, including:
- Using your device for advanced crypto-mining
- Installing reconnaissance or spyware tools
- Deploying ransomware
- Spreading and installing malware and malicious files on your devices
- Stealing your credentials and data
- Remotely controlling your devices and digital life
The malware can also evade common cybersecurity techniques, including sandboxes and virtual machine evasion, as well as debugging techniques.
Staying in the clear from DarkGate, Pikabot, phishing, and botnets
The sheer size and powerful capabilities of new malware botnets are undoubtedly intimidating. However, average users like you still hold most of the cards.
You can follow the following simple advice to strengthen your security posture:
- Keep your software up to date: This includes your operating system, web browser, and other software. Software updates often include security patches that can fix vulnerabilities that could be exploited by malware.
- Install a reputable antivirus and firewall: These programs can help to block malware from infecting your computer.
- Be careful what you click on: Don’t click on links in emails or on websites that you don’t know and trust. These links could take you to websites that have been infected with malware.
- Be careful what you download: Only download files from websites that you know and trust. If you’re not sure whether a file is safe, don’t download it.
- Use strong passwords and MFA: Your passwords should be at least 8 characters long and should include a mix of uppercase and lowercase letters, numbers, and symbols. You should also use different passwords for different accounts and enable MFA.
- Be aware of email thread hijacking: When it comes to phishing, it is important to understand that the attack can come from unknown and known contacts alike. When engaging in email threats, make sure the person on the other side of the line is at all times who they say they are.
How to defend yourself from DarkGate and Pikabot
Cybercriminals will always try new tricks to get you to reveal personal information or click on a link. The best course of action is to trust your instincts and apply a zero-trust approach. Check the sender’s email address, be mindful of system warnings and links, and do not enter personal information on a site unless you are absolutely sure it is safe. Be especially careful when you’re prompted to download software.
Whether DarkGate and Pikabot are the evolution of Qakbot or the malicious creation of a new criminal network, by following this simple advice and increasing your layers of security, you dramatically increase your chances of coming out on the good side of a botnet attack. Remember, always play it safe, and stay updated with breaking security and privacy news.






