A new iPhone threat is using nation-state, sophisticated capabilities to carry out financially driven “hit-and-run” crypto heists. The threat, dubbed DarkSword, breaks into iPhones through zero-click attacks, and in just minutes can steal your on-device data, iCloud data, and crypto wallet credentials. Here’s why it matters to all users, how it works, and how to stay safe.
Meet DarkSword, a nation-state commercial spyware used to steal crypto
iVerify, Google Threat Intelligence Group, and Lookout reported on a new threat active in the wild since November 2025. Like other types of commercial spyware and iPhone malware, DarkSword hides code inside webpages that, when visited, trigger a cyberattack. Unlike commercial spyware, DarkSword does not appear to persist on the device to spy on users. Instead, Lookout reported that it is a financially motivated “hit and run” threat.
![Shared by Lookout: HTML content of the DarkSword File Receiver endpoint previously located on sqwas.shapelie[.]com. This is the code hidden in iFrame that DarkSword was identified using in its campaigns.](https://moonlock.com/2026/03/HTML-content-of-the-DarkSword-File-Receiver-endpoint-previously-located-on-sqwas.shapelie.com_.webp)
So far, DarkSword has been found targeting iPhones in Saudi Arabia, Turkey, Malaysia, and Ukraine. However, what worries Lookout and iVerify is the shift to using highly sophisticated commercial spyware for financially driven cyberattacks.
So far, the threat exhibits signs of being used as a nation-state tool to disrupt, create confusion, and chaos, but Lookout reports that this marks a new phase, as highly guarded nation-state malware appears to have leaked out into the broader cybercriminal dark market.
“DarkSword represents a notable shift that we’ve predicted for years,” said Justin Albrecht, global director of mobile threat intelligence at Lookout.
“Advanced mobile malware has ceased to be a tool wielded solely by governments for espionage and is now in the hands of groups seeking financial gain,” said Albrecht.
It’s not the first time security companies have warned that spyware is broader than thought
iVerify has been warning for some time now that commercial spyware like Pegasus, thought to be reserved solely to go after high-value targets like politicians, human rights activists, and government opposition groups, is actually being used more broadly, and targeting average users. DarkSword represents the next step in this escalating trend.
iVerify called DarkSword a serious, widespread threat that has a “global blast radius, impacting millions of unpatched iOS devices.” The company added that DarkSword tools are readily available for reuse by other threat actors.
DarkSword cyberattacks start with social engineering
While DarkSword is technically a zero-click threat, its kill chain starts with social engineering. As documented by Google and Lookout, users are redirected to sites that contain hidden code within their HTML, specifically within iFrames.
To drive attack success rates up, the attackers have used fake sites that impersonate known brands and hijacked known websites as well. Because DarkSword starts with online social engineering, this technique is likely to remain the same.
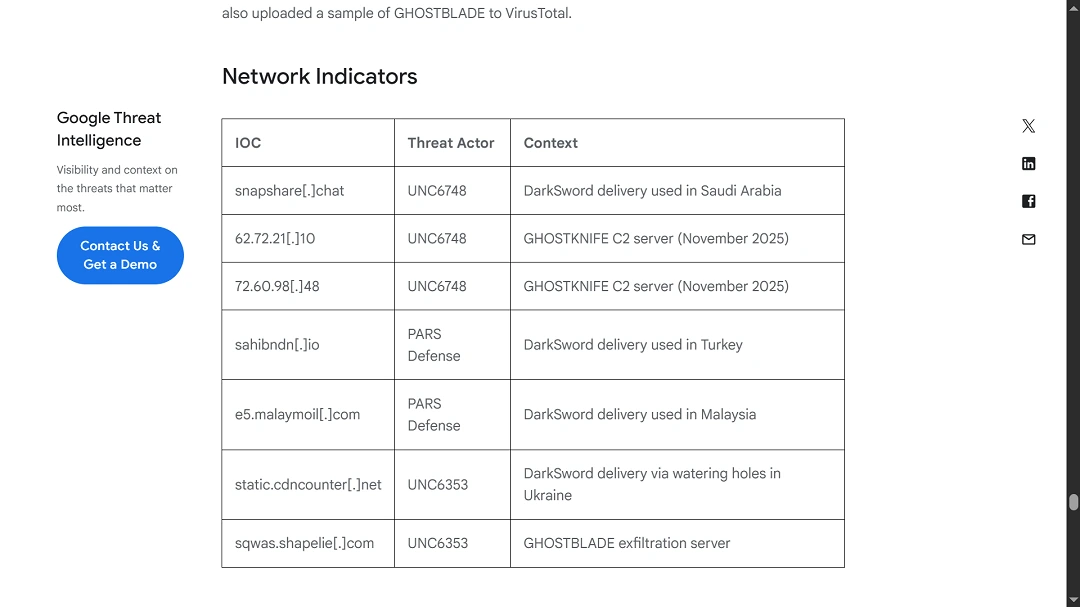
For example, in Saudi Arabia, cybercriminals created a fake “Snapchat” themed website at snapshare[.]chat. Meanwhile, in Ukraine, the threat actor UNC6353 hijacked government sites and a news site to deliver the malware. Google Threat Intelligence linked DarkSword to UNC6353, a well-funded suspected Russian espionage group previously observed using Coruna spyware.
![The news from Donbas, Ukraine novosti.dn[.]ua became temporarily unavailable after DarkSword threat actors used it to trigger iPhone infections.](https://moonlock.com/2026/03/x.webp)
How DarkSword steals your iPhone data in just minutes
DarkSword targets iOS versions 18.4 through 18.7 and uses 6 different vulnerabilities to deploy final-stage payloads known as GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER malware.
DarkSword works on Safari, Chrome, Firefox, and Edge. It can also breach iPhones through browsers used inside apps like Facebook, Instagram, or Snapchat (which use SFSafariViewController or WKWebView).
Once a user visits a site that DarkSword attackers fabricated or took over, the malicious iframe embedded into that web page loads without the user interacting with the page at all, as a zero-click.
DarkSword then breaks free from browser security restrictions, which sandbox code running on webpages to prevent different types of attacks. It breaks the browser isolation by leveraging WebGPU to inject into media playback.
DarkSword gains full kernel read/write access, which it uses to gain access to privileged processes and modify sandbox restrictions, gaining access to restricted parts of the iOS filesystem.
What happens next is that the main threat module, “pe_main.js,” orchestrates the download of several malicious payloads on your iPhone by connecting to threat infrastructure, which threat actors can rotate when security experts ring the alarm.
Each payload gathers and stages (collects and puts together) sensitive information such as passwords, keys, and other documents in accessible locations. To finish things up, DarkSword loads its final exfiltration payload module that transfers your iPhone data, including emails, cryptocurrency wallets, usernames, passwords, photos, and other files, to the servers operated by the attackers.
“After all the data has been exfiltrated, the staged files are cleaned up, and the process exits cleanly,” Lookout reported.
After all the data has been exfiltrated, the staged files are cleaned up, and the process exits cleanly.
The Lookout press release
The entire process, unlike commercial spyware or nation-state threats, is over in just minutes.
DarkSword uses a “‘hit-and-run’ technique to rapidly exfiltrate highly sensitive data—including credentials and cryptocurrency wallets—within minutes before erasing its presence to evade detection,” Lookout said.
What data does DarkSword go after?
Going into specifics, security experts from Google, Lookout, and iVerify said the following data can be accessed by DarkSword:
- SMS/iMessage
- Call history
- Address book
- Wi-Fi configuration and passwords
- Safari web history and cookies
- Location and location history
- Notes
- Calendar
- Health data
- Photos
- iCloud Drive
- Cellular and SIM information
- Emails
- Installed app list
- Saved passwords
- Telegram message history
- WhatsApp message history
- iCloud files
- Cryptocurrency wallets
Cryptocurrency exchanges targeted by DarkSword include Coinbase, Binance, Kraken, Kucoin, Okx, Mexc, etc. It also targets wallets such as Ledger, Trezor, Metamask, Exodus, Uniswap, Phantom, Gnosis Safe, and others.
How to stay safe from DarkSword
While DarkSword is a highly advanced threat, there are still several things any user can do to add layers of security to their digital environment and mitigate this threat.
Get the Moonlock app: It can help you strengthen your digital posture
While the Moonlock app is designed for Mac security, if DarkSword threat actors gain access to your iCloud data, along with other credentials, your entire Apple ecosystem can be compromised.
The Moonlock app will not only run live checks in the background for malware and spyware, but it also helps you turn your Mac security settings to the highest levels, and, through uniquely human-centered designed features, the app will give you security tips that are highly effective for Mac users in this current threat landscape.
You can try out Moonlock for free with a 7-day trial.
Secure your crypto wallets and accounts
Cryptocurrency theft is apparently the primary goal of DarkSword. If you are a crypto user, secure your wallet with MFA, biometrics, or authentication apps. You might want to consider having separate crypto wallets if you like having one on your browser, and only fund your browser wallet with a minimum.
Cold wallets are also a good option to explore to further enhance your security. Additionally, make sure all your personal accounts have another layer of protection besides your passwords, whether it be MFA, biometrics, or passkeys. This way, even if attackers get your password, they still cannot break in.
Keep your iPhone and all your devices updated
Google responded to the DarkSword threat with patches and updates made across Safe Browsing for iOS. Similarly, expect Apple to do the same. Keeping your devices updated gives you access to the latest security fixes that deal with these types of threats. While cybercriminals will find new exploits, updating is a must for enhanced security.
Use Lockdown Mode if you think you are being affected.
Apple designed Lockdown Mode specifically to deal with these types of zero-click threats affecting users. If you think you are being targeted by DarkSword or a similar sophisticated threat, enable Lockdown Mode to dramatically reduce your digital surface and lock attackers out of it.
Final thoughts
DarkSword is a novel threat that has broad implications. It uses commercial spyware malware capabilities but is not designed for ongoing surveillance. Instead, DarkSword takes on a multi-stage loader route after infection and includes features to target crypto wallets. This technique, coded for financial theft, is on the rise in the dark web macOS stealer industry, linked to Russian-speaking malware-as-a-service industry forums and seen in use by financially driven nation-state threat actors like North Korea in campaigns like Contagious Interview.
Despite the attribution complexities and sophisticated, advanced level of the malware itself, what you should know is that these types of threats may soon be targeting anyone and everyone. By taking simple actions and following the tips in this report, you can significantly level up your security posture to deal with what seems to be the start of a new era of nation-state, financially driven cyberattacks.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Apple Inc. Mac and macOS are trademarks of Apple Inc.








