The Moonlock Lab Team has identified a new macOS stealer active in the wild. At the time, infections have been detected in Thailand, Vietnam, and Spain, but the stealer could spread fast, as it is promoted on the dark web by top macOS black market players.
The new stealer is linked to a malware developer formerly known as 0xFFF, currently going by the alias alh1mik. The Moonlock Lab Team has been tracking alh1mik since 2023. And despite having a tumultuous history, alh1mik’s connections within Russian-speaking dark web forums are a sign that this new stealer could scale fast.
Protect your wallet from the new stealer
Beyond its presence on the dark web and all the flair, this stealer introduces some new capabilities that all Mac users should be aware of.
NotnullOSX, a new stealer that all Mac users should be aware of
Recently, Moonlock Lab reported on a new macOS stealer dubbed notnullOSX. The stealer is making waves on the dark web and is actively being distributed in the wild.
At present, notnullOSX developers appear to only be giving this malware to operators who are targeting users with more than $10,000 in their crypto accounts. However, the floor could lower, and the stealer could become even more widespread.
Besides setting a $10K baseline, this stealer’s modular architecture makes it more agile, resilient, and responsive (in real time) than other stealers like MacSync. At the time, notnullOSX was found being distributed through fake sites displaying ClickFix instructions and fake Google Documents that tried to trick users with a fake Google API Connector driver update.
To read the full technical analysis of notnullOSX, check out the Moonlock Lab Team report.
How NotnullOSX social-engineers its way into your Mac
While elements of the social engineering attack chain of notnullOSX are likely to change, let’s look at how the malware has spread and infected users to date.
The Moonlock Lab Team has found that notnullOSX attackers are using Google Ads and promoted YouTube videos to reach users and lure them into installing the malware. These ads direct users to fake sites where ClickFix instructions are hosted.
Additionally, Moonlock Lab also found a campaign where notnullOSX was distributed as a fake Google API update, taking a more technical path. In that campaign, users were directed to download via an official Google link that contained a document.
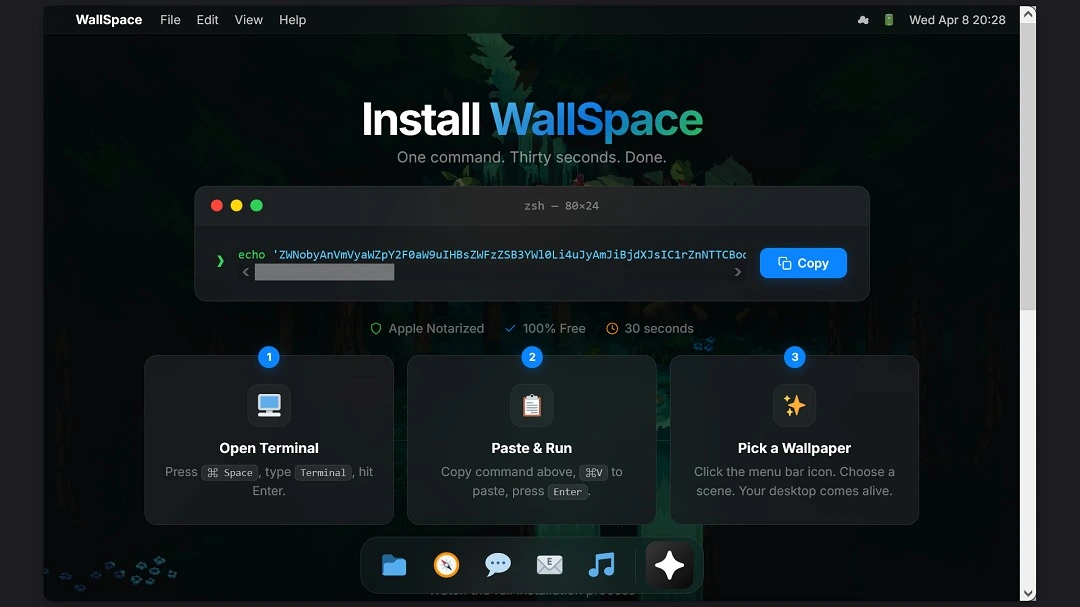
The document was encrypted and, therefore, locked. Users who opened the document then saw an outdated driver, “document decryption error,” and were given fake ClickFix “solutions” to fix it. Copying and pasting the command on a Mac Terminal triggered the launch of the malware.
How the notnullOSX ClickFix attack works
Another social engineering infection chain, detected by the Moonlock Lab Team, shows that users were directed to download a disk image. When the disk image is installed on a Mac, the Terminal is automatically opened, while a ReadMe file gives users a malicious ClickFix script to copy there.
This is a notable infection chain. If attackers manage to automate the ClickFix process by opening your Mac terminal and automatically copying and pasting the script (which, at the present time, they cannot do), ClickFix’s success attack rates will skyrocket.
Bottom line, macOS stealer developers are always finding new ways to streamline the copying and pasting of scripts. Therefore, ClickFix is constantly evolving and becoming more difficult to spot. A terminal window opening up by itself is an attempt to do exactly that.
Multiple notnullOSX attack campaigns detected
Another interesting and notable aspect of the ClickFix element of this campaign is that the script, when decoded, shows hxxp://111[.]90[.]149[.]111:8080/installer as the domain where the bash installer of the malware is hosted.
This type of domain, containing an IP in plain numbers, hxxp://111[.]90[.]149[.]111:8080 raises fewer red flags than others observed in ClickFix attacks, which point to www. domains that look more suspicious.
![A screenshot of the Google search result: wallspaceapp[.]com, "Install WallSpace — Live Wallpapers for macOS."](https://moonlock.com/2026/04/Search-results-mac-wallpaper.webp)
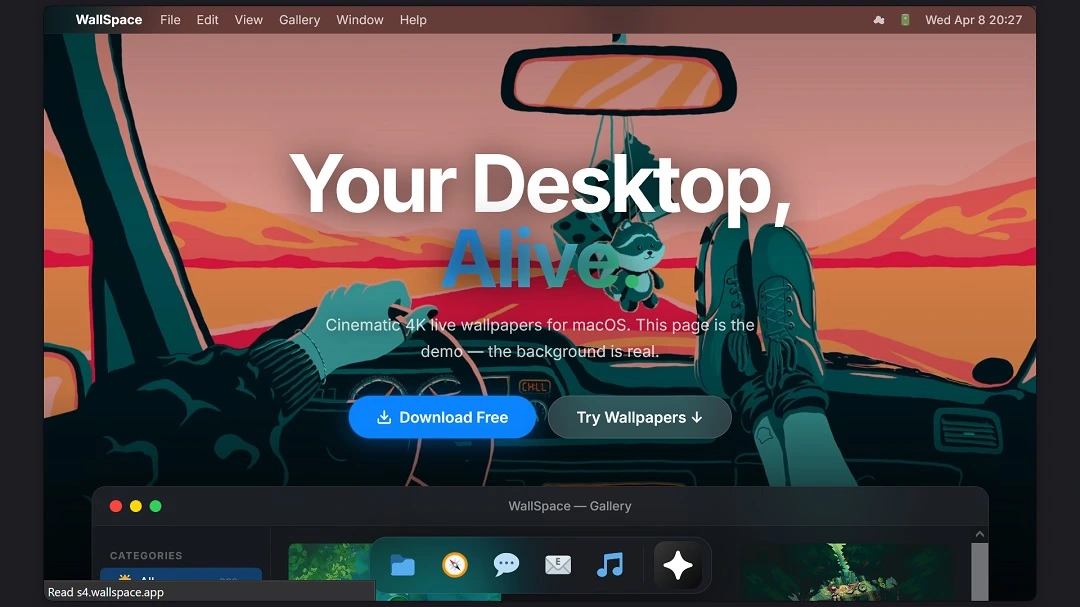
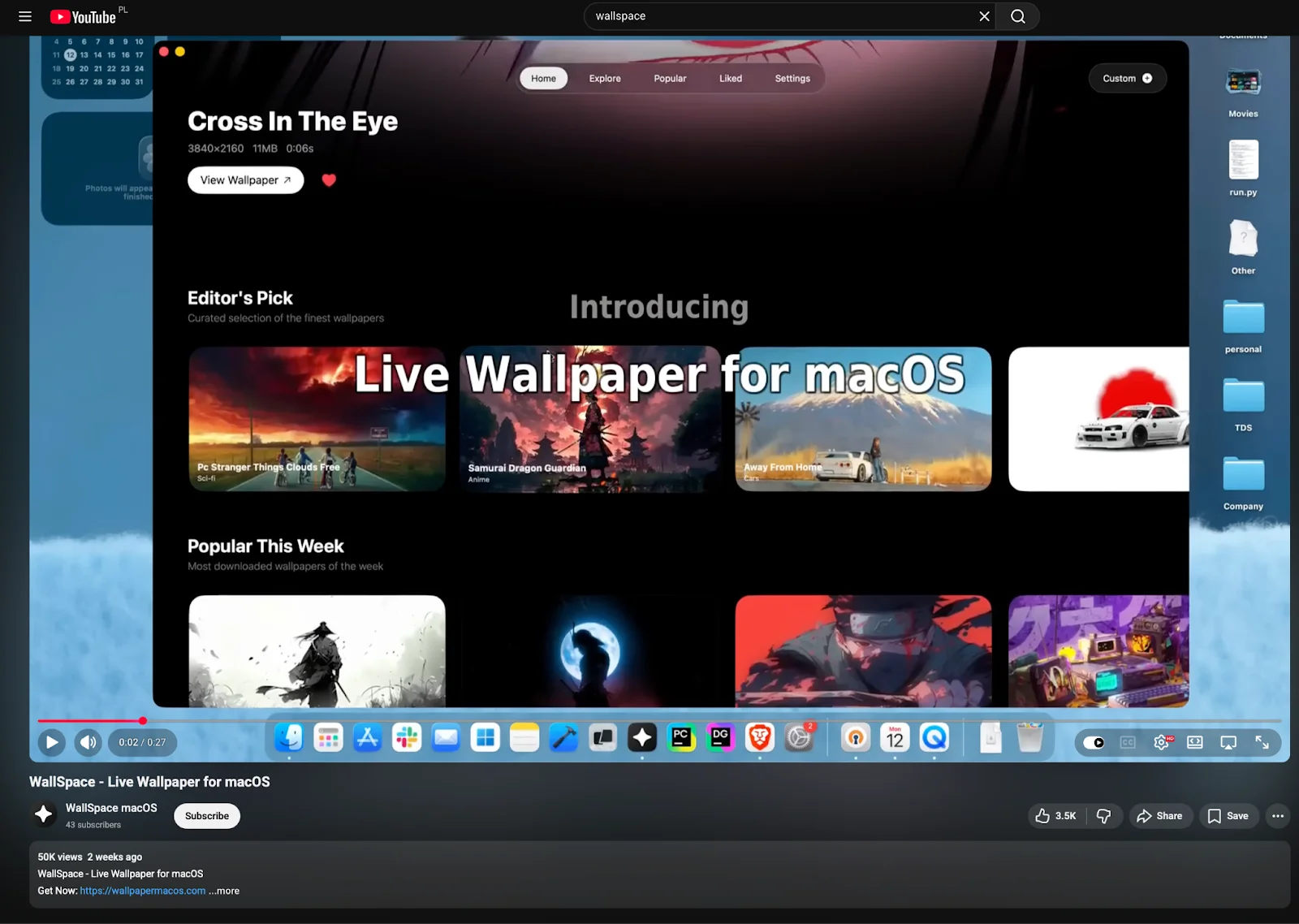
Besides automatically opening your Mac Terminal (a new trick) and cleaner domains in ClickFix scripts, another notnullOSX campaign detected by the Moonlock Lab Team targets less tech-savvy users via harmless-looking sites.
In this case, the site offering Mac wallpapers, hosted on wallpapermacos[.]com and wallspaceapp[.]com, and promoted on Google Ads and YouTube, acts as a highly convincing lure due to its innocuous-looking nature. On the sites, users are also given ClickFix instructions when they click on “Download for Mac.”
What NotnullOSX can do: System password, full disk access, crypto, developer credentials, Mac data, and live WebSocket
NotnullOSX is not actually bypassing Gatekeeper and Apple’s TCC security protections on your Mac. Instead, it is asking you to give it full privileges to operate. Once running on your Mac, the stealer will prompt you for your system password and ask for full disk access (FDA). Once the stealer has full disk access, it goes after your system info, iMessages, Apple Notes, and Safari Cookies.
Targeting Safari is another notable capability of notnullOSX, as macOS stealers often target other browsers and leave Safari out due to its enhanced security. However, notnullOSX goes after Safari data because it already has full disk access, making extraction easier.
We have seen stealers requesting full disk access from users before. For example, in a recent campaign, threat actors leveraged the OpenClaw AI agentic tech hype to infect users with a stealer. The stealer in that campaign also requested full disk access.
With full disk access, the notnullOSX stealer also goes after crypto wallet credentials, browser history, and Firefox and Telegram data. Plus, it uses an exclusive module to replace your hard wallet apps with a fake crypto app (more about this module in the section below).
Developers appear to be a target of interest for notnullOSX operators. The stealer is coded to steal credentials from GitHub, Microsoft Azure Cloud, npm, Terraform, and other developer platforms.
Looking into notnullOSX modular grabbers and how they steal your data
Moonlock Lab notes that notnullOSX “operates through a modular architecture, which means individual binaries downloaded from C2 and staged in /tmp, each responsible for a specific data category.”
For example, notnullOSX CryptoWalletsGrab (image below) hits desktop wallets such as Bitcoin Core, Electrum, Wasabi, Exodus, Atomic, and others, copying raw data files without decryption.
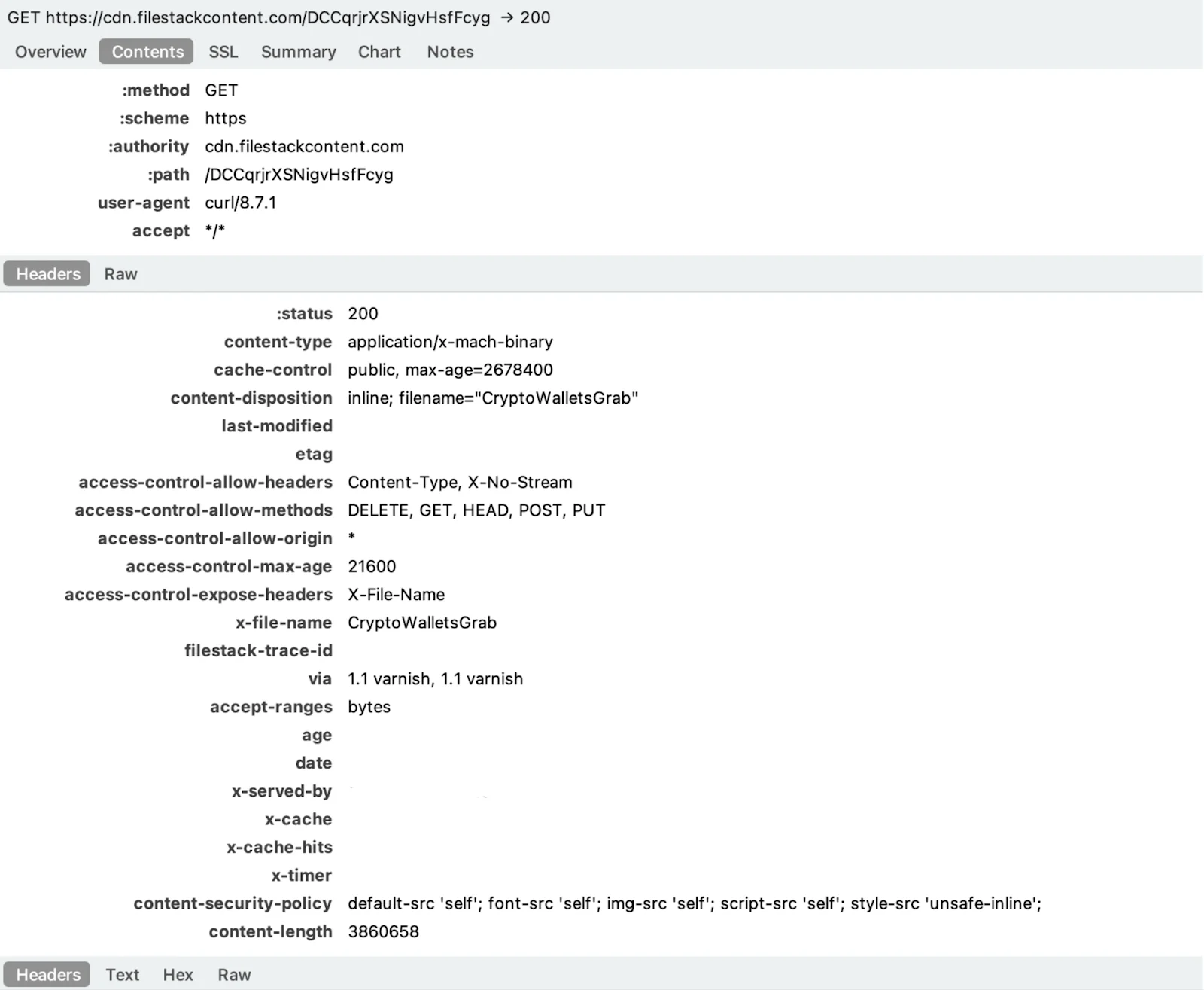
“It also sweeps browser extension profiles against a hard-coded list of 30-plus wallet extension IDs, targeting the IndexedDB subdirectory where the encrypted seed phrase vault lives,” said the Moonlock Lab Team.
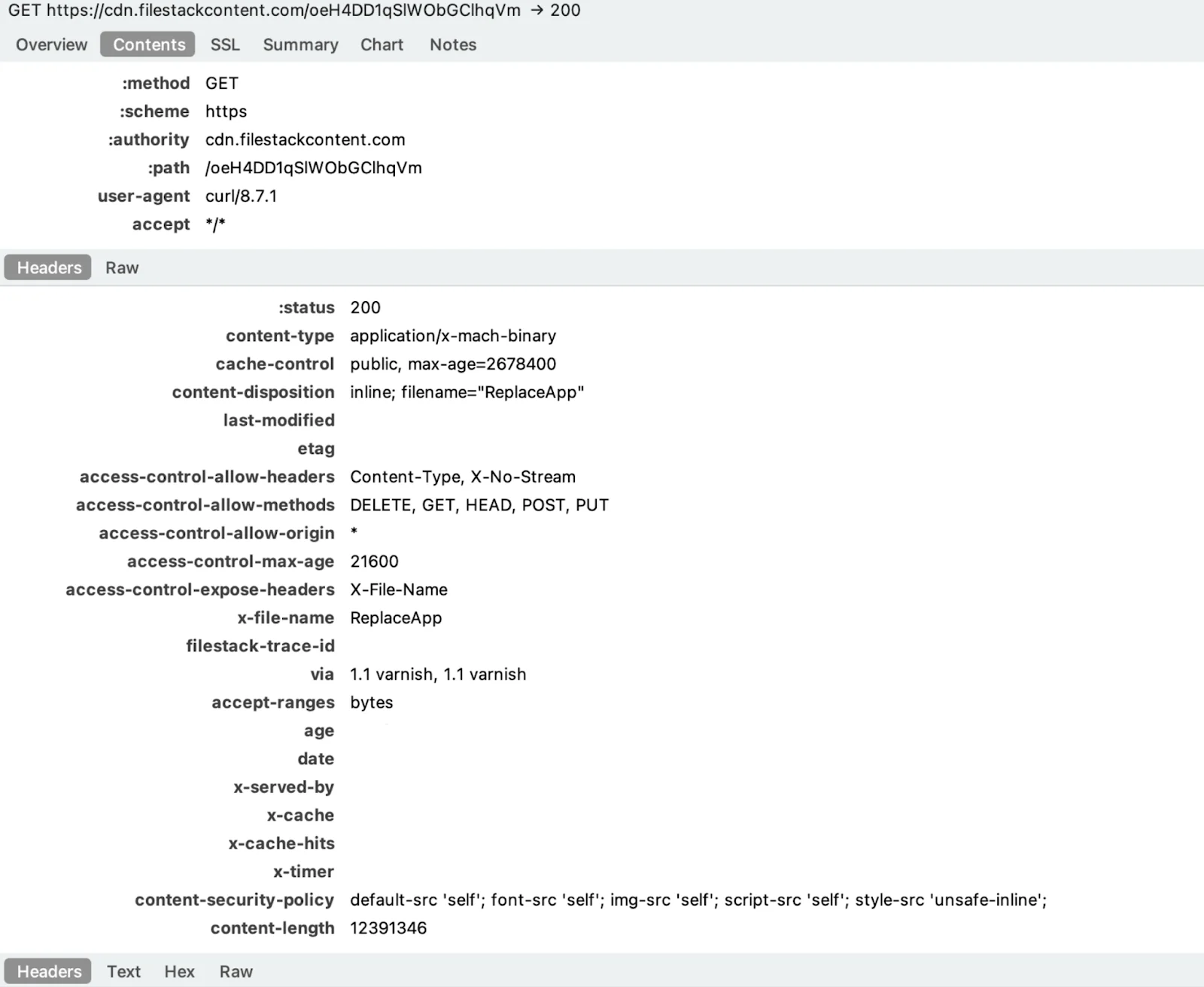
Another example of the modular agility of notnullOSX is the Replace App module (image below). This module is coded to swap hardware crypto wallet apps, such as Ledger Live or Trezor, and replace those with a trojanized version of the legitimate app. Using this fake app, the attackers can intercept the seed phrases you enter.
A rare live WebSocket to control your Mac in real-time
NotnullOSX has a live WebSocket channel back to C2. This means that operators using this stealer can send commands in real time to the users they breach.
The live WebSocket caught the attention of the Moonlock Lab Team. “This is not how a stealer normally behaves,” they said.
While traditional macOS stealers collect, transmit, and exit, notnullOSX has a persistent bidirectional channel with a “keep-alive heartbeat” indicating command-and-control capability, the Moonlock Lab Team explained.
This gives the malware operator the capability to send instructions live when connected.
The stealer is not only a backdoor but also persistent malware. It is not designed for “hit-and-run” heists, but will live on, hidden in your Mac.
NotnullOSX is coded for stability and “error-handling.” Why should this matter to you?
The Moonlock Lab Team’s dark web investigation shows that the developer of notnullOSX spent years refining his approach, reappearing in 2026 with a much more advanced piece of malware.
The developer seems obsessed with stability and error-handling, and the code of this malware shows that. This matters to all Mac users because it makes this stealer meticulously efficient. It also makes it more difficult to spot, as it will generate less “noise,” glitches, crashes, or Mac performance issues that normally alert users that something is wrong.
NotnullOSX is also a multi-programming language threat. It is written in Go but executes diverse functions in other programming languages that are native to your macOS.
How to stay safe from the new notnullOSX stealer
Below, you’ll find some tips and advice on how to keep yourself safe from the notnullOSX stealer and other similar malware that can bypass your Mac’s built-in security features.
Get the Moonlock app. It can flag notnullOSX before it breaches your Mac.
Not only was notnullOSX first tracked and analyzed by the Moonlock Lab Team, which updates Moonlock’s malware database, but Moonlock’s telemetry has already identified notnullOSX samples in Mac computers in different countries. This is good news because it means that the Moonlock app can identify, flag, and notify you if notnullOSX files attempt to breach your Mac.
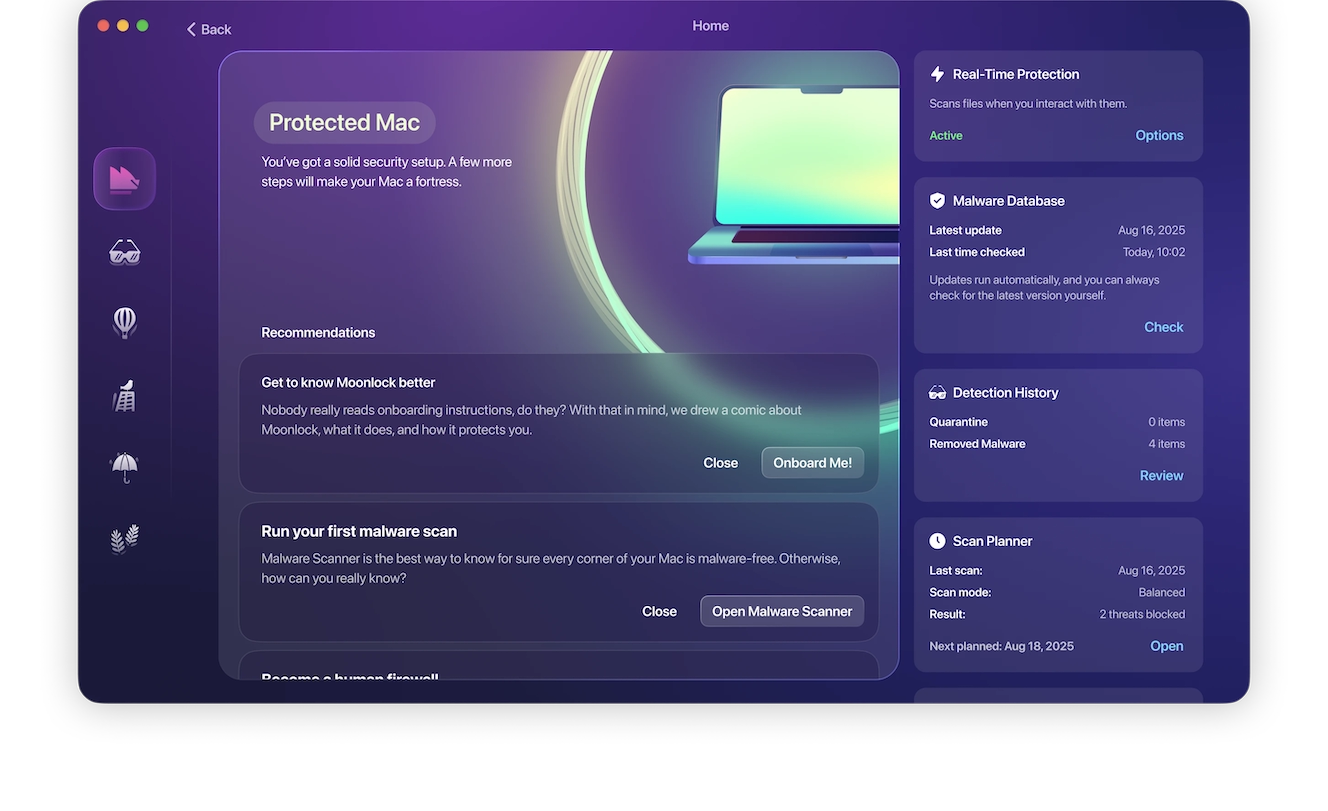
The Moonlock app accomplishes this by running silently in the background, checking everything you interact with. Moonlock checks your files, apps, and even Mail attachments at all times, so you know for sure that your computer is safe.
You can download and test-run the Moonlock app with a free trial today.
ClickFix and a novel type of social-engineering: Watch out for them
NotnullOSX, like other macOS stealers, relies on ClickFix techniques to breach your Mac. It combines ClickFix instructions with fresh, new social-engineering tactics to make the instructions appear less suspicious.
Additionally, attackers use Google ads, social media, emails, YouTube videos, and other channels to direct you to fake sites. Knowing these techniques gives you an edge and can help you spot a ClickFix attack a mile away.
Tips for safer crypto wallets, no matter what your balance is
No matter how much crypto you are holding in your wallets, cybercriminals will empty them out. To stay safe, there are some tips you might want to follow.
First, keep in mind that browser extension crypto wallets are easy to hack for macOS stealer operators. Keep browser extension crypto wallets funded with only the minimum amount of crypto you need. Keep your main crypto balance account on a separate device or offline.
Cold wallets are a good alternative and are considered the standard in security. These wallets are kept completely offline. If a cold wallet seems like overkill for you, another alternative is choosing an online crypto wallet platform that has a high level of security reputation and offers biometrics as multi-factor authentication (MFA). You can keep those off your Mac as well.
Final thoughts
This new macOS stealer appears to be targeting a select group of users: those holding more than $10,000 in crypto and those working as developers. However, it may pivot to expand on this target group. Follow the advice in this report, stay up to date with notnullOSX in the news to stay one step ahead of it, and keep your Mac, your crypto, and your data safe.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Apple Inc. Mac and macOS are trademarks of Apple Inc.







