The classic definition of an email virus is a malicious email that includes code or a link designed to infect your device. It can then send copies of itself to everyone on your contact list. However, as threats evolve, their definitions tend to broaden.
Today, email malware is considered to be any email that is sent with a malicious purpose, whether it’s a phishing email or a virus email. This also includes any emails that contain malicious links, files, or hidden malware code.
Can you get malware from opening an email?
The straight answer is usually no. In most cases, whether you’re at work, at home, or on the go, opening an email is a harmless task, but there is a caveat worth understanding. An email virus or other type of malware can infect your system after some form of user interaction with the message in your inbox, but not from simply viewing it.
This wasn’t always the case — early email clients like Microsoft Outlook Express and Lotus Notes rendered HTML emails with JavaScript execution enabled by default, meaning a malicious script could run the moment a message was opened. Modern email clients have since disabled JavaScript in email rendering entirely — and as of 2026, this attack vector is considered obsolete.
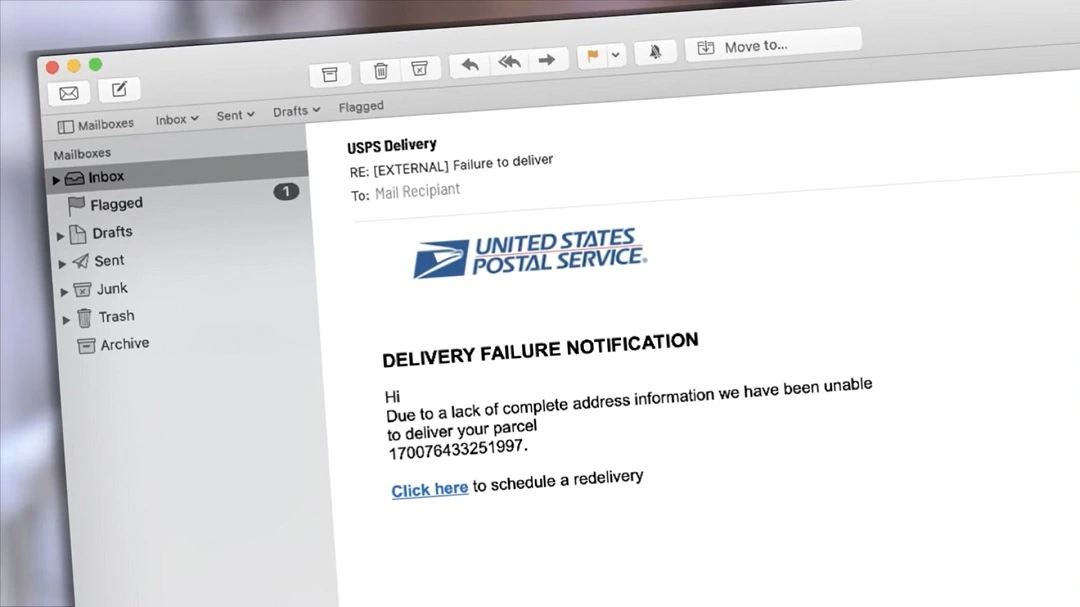
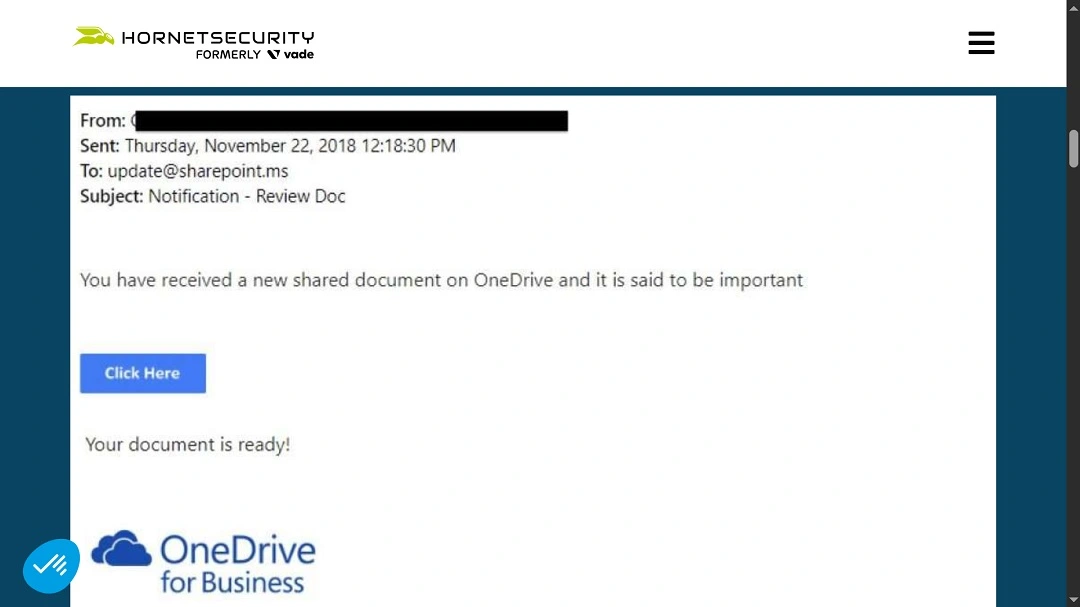
Cybercriminals can trick you into believing they are a familiar brand or person and lure you into taking action after reading a phishing email. This includes clicking on a malicious link that appears legitimate, opening an email with a PDF attachment containing a virus, downloading an image or file with hidden malicious code, or scanning a QR code that takes you to a phishing page (known as “quishing”).
Tracking pixels may also be present in some emails (small, almost invisible images sometimes called “white dots”), which are loaded when opening a message. Although tracking pixels do not leave malware, they can inform the sender that you opened the email and, in some cases, provide data about the time at which the email was opened and information about the device you’re using.
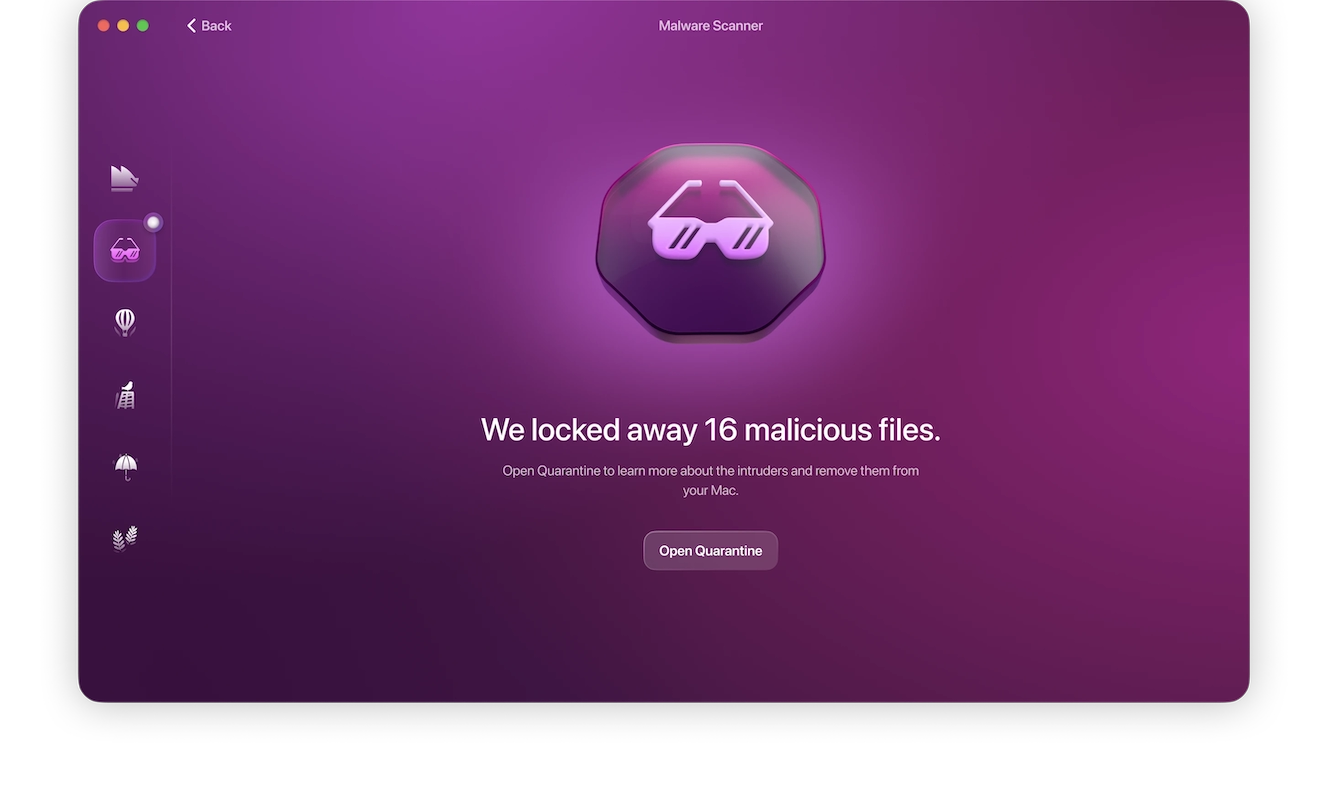
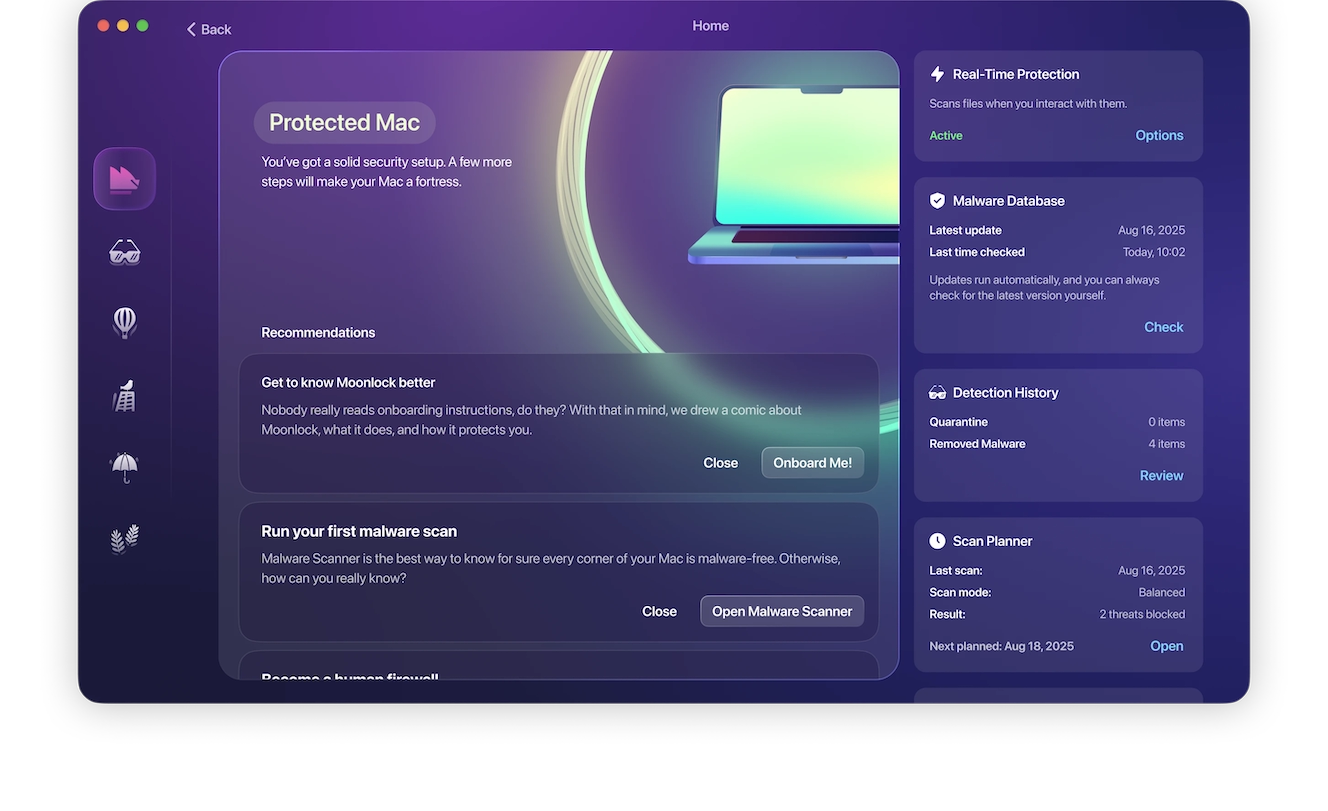
One of the practical ways to enhance your email security is to use a security tool such as Moonlock to scan your email for viruses, malware, tracking elements, and block them.
Zero-click attacks
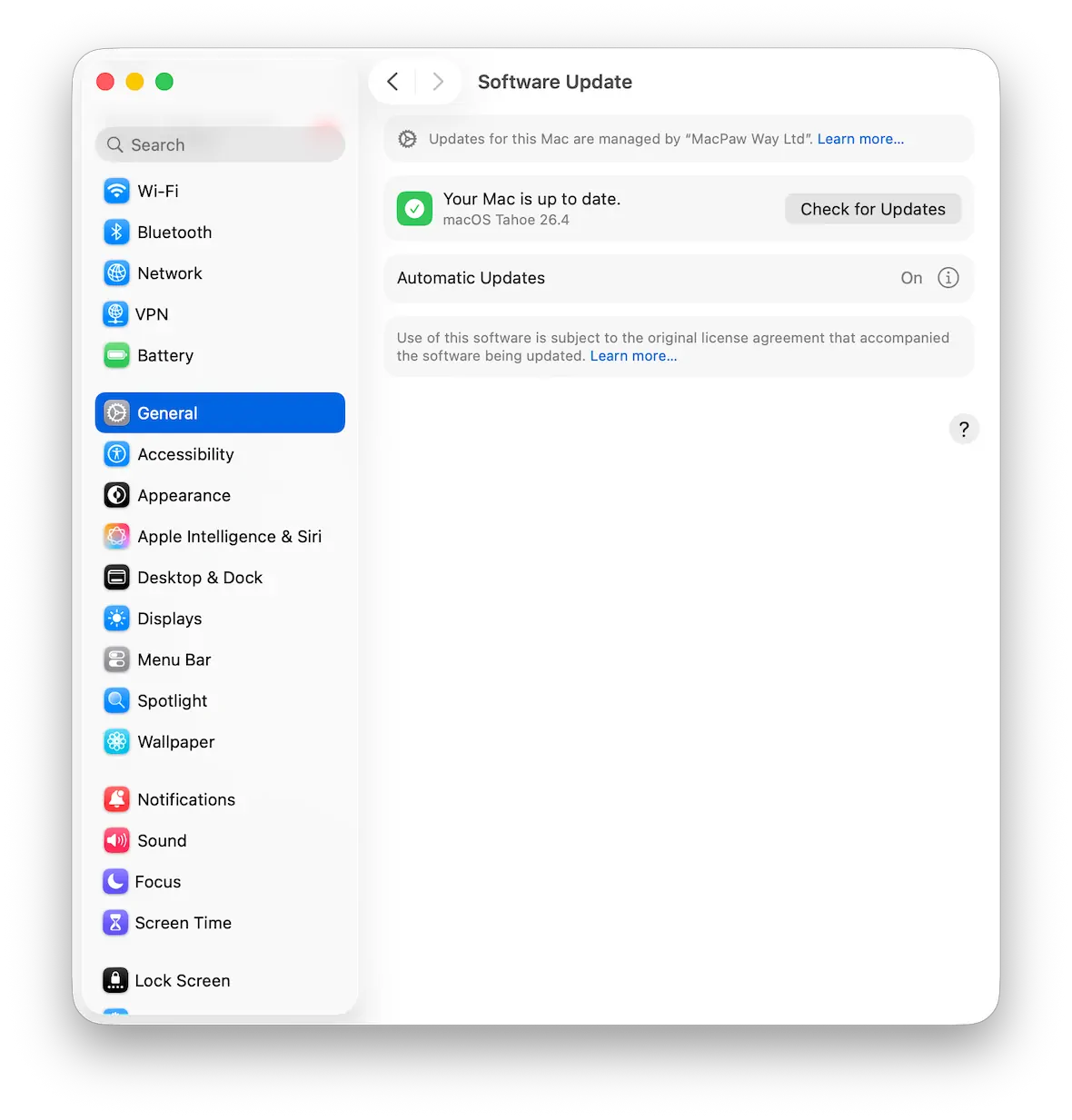
In very rare cases, simply opening an email can be enough — if your email client has an unpatched vulnerability, attackers can exploit it to run malicious code without you doing anything else. This is called a zero-click attack, an extremely sophisticated form of a cyber attack that requires no user interaction. Unlike the old “JavaScript in email” era where the vulnerability was by design, zero-click exploits target low-level bugs in parsing or memory handling — which is why they are far rarer and typically patched quickly once discovered.
While rare, real-world instances of zero-click attacks have occurred in the past. This happened in 2021 with Apple Mail on older versions of the macOS operating system (macOS Catalina 10.15.5 and under). The vulnerability enabled threat actors to launch malware after an email had been opened, access the mailbox, and steal the email account. The vulnerability was fixed, but the incident highlighted the need to keep software and apps up-to-date to minimize vulnerabilities.
What the latest 2026 data shows
In Cofense’s 2026 Annual Report, phishing emails delivering malware increased by 204% in the span of a year between 2024 and 2025, and statistics revealed that one malicious email was sent every 19 seconds. Verizon’s 2025 Data Breach Investigations Report also shows that phishing is still one of the leading initial access vectors (16% of breaches) and that 60% of breaches involve a human element.
Email is still a major source of malware, but most email attacks still require human intervention.
How damaging can email malware be?
As we have said already, malware in an email can be extremely dangerous and damaging.
The most common vectors of attack today are email and messaging. Emails can contain stealers, spyware, and other malware that can take over your computer.
The malware that is spread via email can steal your personal data, breach your browser, and steal your passwords and history. They also have the potential to encrypt your device, spy on you and your family, and do much more.
Which email attachments are most dangerous?
Not all attachments are created equal. Some are designed specifically to deliver email malware or trick users into running harmful files. These are among the most common risks to Mac devices, especially when files are disguised to look legitimate.
- Executables (apps and installers). Executables are apps or files that are installed on your Mac and then run code. They can range from app bundles to installer packages or legitimate-appearing apps that are actually trojan horses or backdoors used to embed persistent malware and remain on your machine.
- Scripts (JS, VBS, shell scripts). Scripts often automate tasks like running commands to execute system-level actions or downloading payloads. They can also be used to change system settings without getting detected. JavaScript (.js) files can execute system commands when run outside a browser, while VBS (Visual Basic Script) files are commonly used to silently download and run malware. Even a simple shell script file like “.sh” can act as a vector to deliver malware on macOS.
- Macro-enabled Office documents. Office documents like Word or Excel files with macros can execute code when enabled. Threat actors can use prompts like “Enable Content” to trick any user into running malicious code embedded in a document. That said, this mostly applies to Microsoft users. Apple users only face this risk when using Microsoft Office apps or enabling macros.
- Disk images and installer packages. These files are dangerous on macOS because they’re often used to distribute software. This feature is abused by attackers with trojanized installers, which hide malware posing as genuine software or software updates (e.g., web browsers). Malware is installed on your Mac when you run an infected DMG/PKG. File extensions are commonly abused on macOS. By default, the Finder doesn’t show file extensions, so “invoice.pdf.app” could look like a PDF. This, along with appropriate icons and names, allows DMG or PKG installers to be disguised and, thus, more likely to be opened by users.
- Compressed archives (ZIP, RAR). Archives can hide malicious files inside, making a threat appear ordinary and legitimate. Once extracted, the true payload is revealed. This payload is usually a strange-looking or unfamiliar filename or icon. A common attacker trick is to send password-protected ZIP or RAR files — since email security scanners cannot inspect encrypted archives, the malicious payload inside passes through undetected. The password is then provided in the email body, giving the appearance of a “legitimate and secure file share”.
- Phishing emails often contain PDFs. Although PDF files do not always contain viruses, they can still be a delivery vehicle — embedded links, auto-opening actions, and JavaScript supported by some PDF readers can redirect you to phishing pages or silently trigger a download of a malicious file.
What is an email virus? Types of email malware and examples
As mentioned, due to the many online threats that exist today, email malware comes in different shapes and forms. Let’s look at the most popular types of email malware.
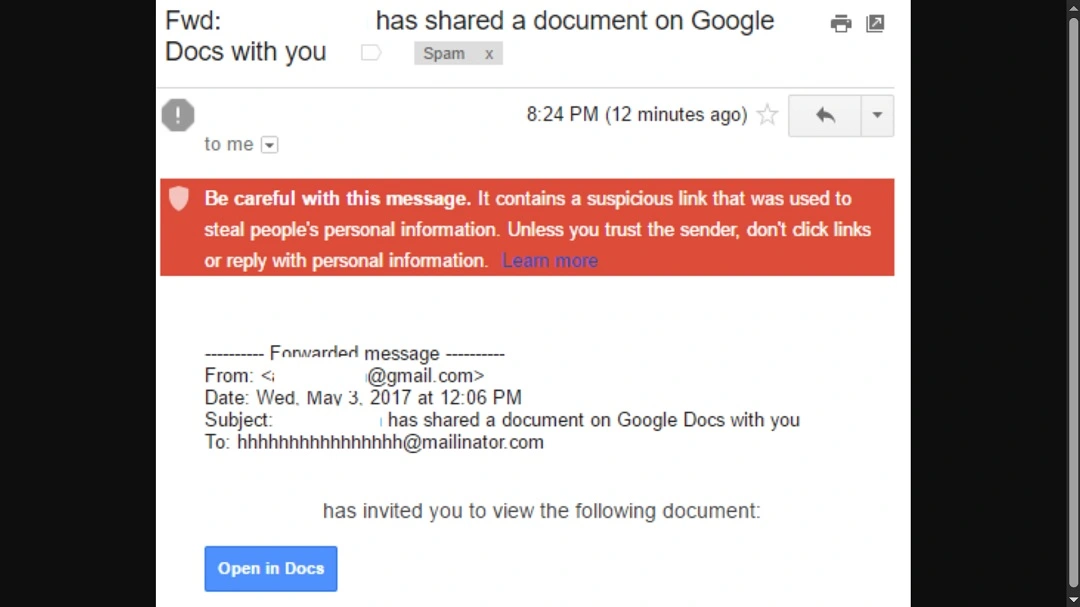
Phishing
Emails designed to deceive users into revealing sensitive information, such as login credentials or financial data, are considered phishing emails.
In the 2017 Google Docs phishing attack, cybercriminals sent emails that appeared to be invitations to a Google Docs document. Users who clicked the link were directed to a fake Google login page, where their credentials were stolen.
Ransomware
Emails containing attachments or links to malicious software that can encrypt files on a victim’s computer are known as ransomware. The attackers subsequently demand payment for the files’ release.
In the WannaCry Ransomware Attack (2017), emails containing infected attachments were used to spread WannaCry, which locked users’ files and demanded a ransom payment in Bitcoin for decryption.
Trojans
Emails offering fake legitimate software or apps, often impersonating well-known brands, may trick users into downloading trojan malware. These can steal information, install ransomware, or spread other malicious software.
The 2018 Emotet Trojan Campaign was spread through phishing emails disguised as invoices or shipping notifications, tricking users into downloading malicious attachments that installed the trojan and other malware like ransomware.
Viruses
Emails containing malicious programs that spread through attachments or links, often infecting the system once opened, are considered viruses.
In the case of the ILOVEYOU virus in 2000, a malicious email attachment was disguised as a love letter. Once opened, it spread rapidly through email systems and infected millions of computers worldwide, causing widespread damage.
Email malware with hidden code (invisible text or JavaScript)
Malicious code hidden within the body of the email, such as invisible text or embedded JavaScript, can execute harmful actions when the email is viewed or clicked.
The 2020 zero font campaign used emails that contained hidden JavaScript in invisible text, which executed malicious code when the email was opened. The code was designed to steal personal information or deploy malware onto the victim’s system.
Spear phishing
As a more highly targeted form of phishing, spear phishing uses personalized information to deceive specific individuals or organizations.
The 2016 Democratic National Committee (DNC) spear phishing attack saw hackers send emails to DNC staff members impersonating Google, warning of a security breach and asking them to change their password. The link led to a fake Google login page, allowing attackers to steal sensitive information.

It is important to understand how phishing and email threats evolve. For example, a recent cybercriminal campaign managed to trick users into believing that their Mac was blocked. This type of phishing attack can happen while users are simply navigating the internet, so always stay updated on these sorts of things.
How to scan your email for a virus
There are automated ways to scan your inbox for malware or suspicious contacts. Most of these, however, are paid services built into anti-malware solutions.
A quick note: If you plan to use anti-malware software, make sure it is respected in the industry and has great reviews. Refrain from free online scanning or new and unverified companies offering these services.
There are also ways to manually check if there is malware on your email account, but these methods are very time-consuming. Nevertheless, several tips can help you build healthy habits that, with time and consistency, will secure your inbox.
Use anti-malware software
When it comes to malware disguised as email attachments, anti-malware software is your first and best line of defense. Moonlock can automatically scan Apple Mail attachments, ensuring that all files are free of malware threats.
Check links carefully
Before clicking on any link in an email, even if it looks legitimate, hover over it to see the actual URL. Many malicious emails use links that look similar to trusted websites, but they lead to phishing sites or malware download pages.
Enable email security features
Many email providers (such as Gmail, Outlook, and Yahoo) have built-in security features that can help detect phishing and malicious attachments. Make sure these features are enabled. Spam filters and email malware protection can help reduce phishing attempts.
Avoid opening unknown attachments
Never open attachments from unfamiliar senders or emails that look suspicious, even if they claim to come from a trusted source. Malicious attachments may be disguised as innocent-looking documents (PDFs, Word files, images, etc.) but could contain hidden malware or viruses.
Verify suspicious emails
If you receive an unexpected email asking for personal information, financial details, or login credentials, proceed with caution. Verify the sender before taking action. Contact the person or organization directly using their official contact information (not the one provided in the email).
What are some ways to recognize if an email has a virus?
In most cases, the trained eye can immediately sense if there’s something “off” about an email. And the truth is, the signs are not that difficult to notice.
Be on the lookout for anything that breaks the routine and does not behave like your inbox behaves on a daily.
Here are a few quick tips:
- Watch out for fake security alerts: If you see a pop-up or message claiming to be an Apple Security Alert, be cautious. Apple does not send security warnings through web pop-ups or random messages. These alerts are often scams.
- Double-check the sender’s email address: Is something wrong with the source of the email? Check the email address for any slight discrepancies or oddities.
- Think twice about attachments: These days, a file attached to an email can carry major risks. Even if the person sending you the file is someone you know, they might have been hacked. Check all attachments for malware. (Yes, that means scan them.)
- Don’t click links without checking them: How do you know if a link will really lead you where it claims? Hover over links to see if the URL is that of a legitimate website. Avoid clicking on suspicious links.
- Beware of urgency: Is the sender contacting you regarding an “emergency”? Be wary of emails that pressure you to act quickly or threaten negative consequences. These techniques are designed to trick users into taking rash action.
- Pay attention to normal inbox routines: If something in your inbox feels off and breaks the “normal” routine you experience with your email account on an average day, identify it, report it, and delete it.
- Carefully examine requests for personal information: Legitimate companies won’t ask for sensitive info like passwords or credit card numbers via email.
- Look out for odd branding: Inconsistencies in logos, fonts, or design may indicate that an email is fraudulent.
How to get rid of an email virus
While you might be able to keep an eye on suspicious email attachments, zero-click attacks are much harder to mitigate, especially when they hit via email.
As an average user, you probably won’t ever come across this type of malware, as it’s difficult to fabricate and tends to exclusively target politicians, military organizations, or enterprise leaders. You’re more likely to encounter threats through malicious links, mail attachments, or threats that automatically open fake pages on your browser or download additional files.
Even after receiving your email, the attachment is still stored on the Apple Mail servers and not your device. This means your device will only get infected if you download and run the suspicious file.
Remove malware from emails using Moonlock

For Apple Mail, Moonlock can scan and flag malware before you even tell it to. But don’t worry if you use another email client. You can still use Moonlock’s Malware Scanner to detect and remove all threats that might have come with a recent download or email attachment.
Here’s how to find and remove malware that has been downloaded from email:
- Sign up for a 7-day trial of Moonlock.
- Open Moonlock, then click on Malware Scanner from the left sidebar.
- If this is your first scan, you’ll need to configure your scan preferences. For that, click on the drop-down menu, then select Configure.
- In the new window, under “Scan type,” you can choose between Quick, Balanced, and Deep scan, with each scan type’s Speed, Depth, and Purpose listed below them. We recommend selecting a Deep scan and including all optional file formats: archives, disk images (DMG), and packages (PKG).
- Once you’re happy with your selection, exit the window. Click Scan.
Moonlock will proceed to sift through all the files on your Mac, looking for anything that might constitute a threat, whether it was a malicious email attachment, spyware, or adware. If it finds anything, it’ll capture and isolate it in Quarantine, away from the rest of your system, before fully and safely removing it.
What to do if you accidentally open a suspicious email
If you have opened a suspicious email or a message you didn’t realize was malicious, the sender or attacker will be informed that your email account is active and in use. This may make them target you even more and proceed to spam you with phishing emails or spam messages. Acts like replying to messages or opening files should be discouraged. In general, do not continue communicating with the message.
Don’t click anything else
Do not follow any links, even those that seem to be legitimate, and don’t download any files. A URL can be checked on Virus Total to determine whether it is malicious or not. If you have already clicked or downloaded something, turning off your Wi-Fi can help prevent malware from reaching out to other servers and spreading.
Delete or isolate the email
Either delete the email (move it to the trash) or forward it to a spam/junk folder so you don’t re-interact with it accidentally in the future. You can also use your mail app’s Move to Junk or Block Sender feature (available in Apple Mail) to help filter similar phishing emails in the future.
Scan your device
Scan your email with a trustworthy security tool to identify virus or malware threats, suspicious files or processes, and unauthorized changes. To carry out a complete scan for email viruses and to enhance your email malware protection, use an email malware scanner or email virus scanner such as Moonlock.
Check your accounts
If you have entered any credentials or connected to a login page, change your passwords and enable multi-factor authentication (MFA) on the accounts that have been compromised as soon as possible. This is one of the most critical measures toward protecting against email threats and recovering email accounts.
Review recent activity
Be aware of unexpected logins, emails you did not send, or any account activity that was not authorized by you. Through this, you may be able to determine whether an email virus or malware infection has propagated.
Update your system
Make sure your macOS and software are up to date. The latest versions of operating systems and software often include security patches for known vulnerabilities. This fixes vulnerabilities in your OS that otherwise remain exploitable until updated. Updates are among the simplest steps to take to protect your Mac from cyber threats.
Monitor for follow-up scams
Attackers may continue to send emails once they know that your address is active, so stay alert for similar or repeated messages. Watch for signs of phishing or a recurring virus email campaign, especially if the messages look familiar or if they reference previous ones. Use a security tool to scan your email for viruses, scan for malware in future messages, and block suspicious senders.
What else should you do if you suspect that an email contains a virus?
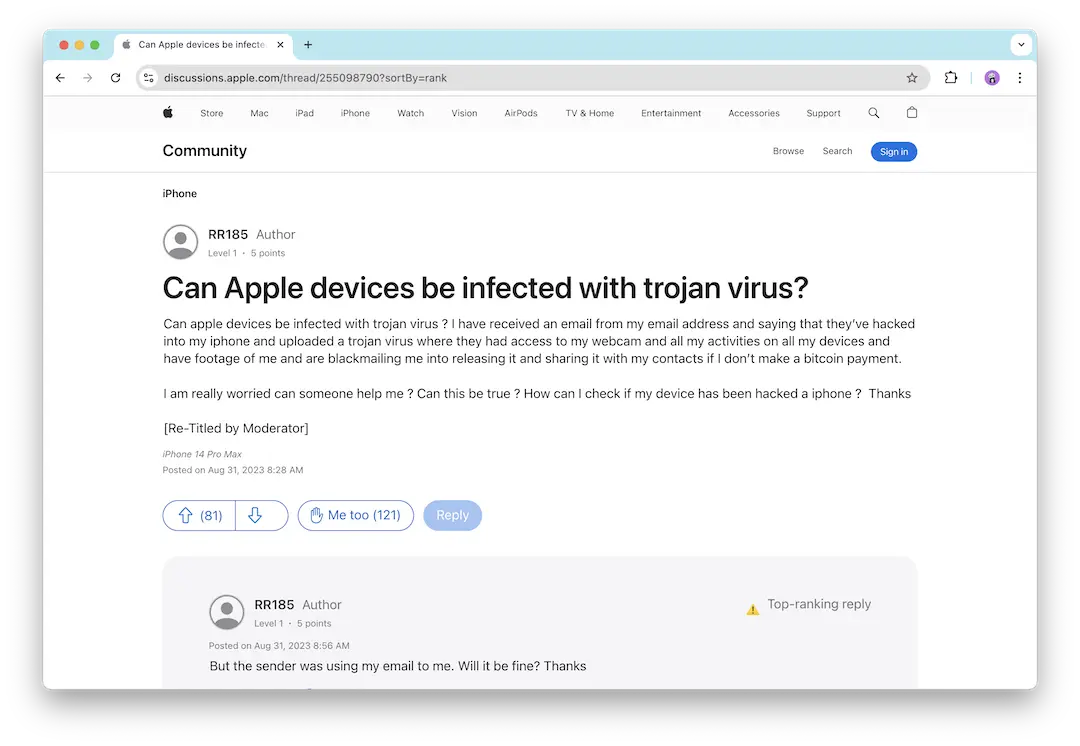
While we have covered most of the ground on what to do about email viruses and malware on your Mac. However, many users spend more time accessing email via their mobile phones. You might be wondering, can email malware infect an iPhone?
The short answer is yes. Cybercriminals are well aware that people often use their mobile devices to open emails. Consequently, malware can infect your iPhone just as easily as your Mac, so be certain to follow the tips listed above when accessing email on your phone.
Other common questions about email malware:
- Do email providers have anti-phishing? Yes. Gmail, Apple Mail, and others have built-in protections to catch phishing emails.
- Should I get an anti-phishing tool? If you’re serious about staying safe, an additional anti-phishing tool can help block threats that manage to sneak through.
- Are strong passwords and 2FA enough? Sadly, no. Hackers can still find clever ways around them. However, strong passwords and 2FA can add a layer of security.
- Are phishing scams getting smarter? Absolutely. Phishers use AI and tricks to make emails look legit, scale attacks, and conceal malware.
FAQ: Email viruses, phishing, and staying safe on Mac
Opening an email on a Mac is generally safe, but email is still one of the most common ways cybercriminals deliver phishing, email malware, and viruses. Below are commonly asked questions about these threats and how to spot suspicious messages, avoid a virus email, and stay safer on your Mac.
Generally, no, because iOS blocks most email-based viruses from executing. The danger comes from clicking links, opening attachments, or engaging in other interactions with a suspicious email.
No. Opening an email is usually safe because modern email clients don’t support active content like scripts. However, there are rare zero-click attacks that could work on older systems.
Yes. Previewing an email is safe, just like opening an email in most email apps. Just be wary of any attachments, unverified links, and suspicious messages.
Cybercriminals are now using AI to mimic real writing and make emails sound more convincing, along with realistic branding and targeted messages. This helps attackers avoid obvious mistakes, making a virus email easier to miss.
Replying to an email can signal that your email address is active and valid, and you may receive more targeted phishing or scam emails as a consequence. It can also result in further social engineering attacks.
In most cases, no, opening a spam email won’t infect your Mac. Links, attachments, and installers, however, can expose your Mac to email malware.
How to protect yourself from malware in email attachments
For those who have an email sitting in their inbox with an attachment and want to know if it contains malware, here are some simple tips to help you:
- Unknown senders can carry email viruses: This is true even without attachments. In general, if you didn’t expect it, just skip it. Random attachments are like uninvited guests — some just won’t leave.
- Enable Moonlock’s real-time protection: Moonlock can monitor all activity on your Mac, scanning new files and downloads for threats.
- An odd file type is a red flag: If the file extension is .exe, .zip, or .bat, it could indicate a not-so-fun surprise. Proceed with caution.
- Take advantage of built-in security tools: Let your email provider scan email for virus threats automatically. Turn on those built-in security features and let your email provider flag suspicious attachments.
- Hire a digital bouncer: Shop for a good anti-malware tool and let it scan attachments before you dive in to help keep your inbox safe.
- Contact the sender directly: If in doubt, text or call the sender. Trust your gut — it’s better to ask than to regret it later.
Finally, if you are getting too much spam, there might be something off with your configurations or settings. Read our guide on how to stop getting spam emails to rapidly fix the eternal spam issue.
Staying safe from email threats is all about being cautious and aware and using the right tools. Whether it’s phishing, malware, or sneaky links, following simple steps like verifying the sender, checking links and attachments, and keeping your security software up to date will keep you one step ahead.
By staying vigilant and making smart choices, you’ll avoid falling for common email traps and keep your digital life safe.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Apple Inc. Mac and iPhone are trademarks of Apple Inc.