Picture this: You’re checking your email or texts, moving fast, and you click a link. A second later, it hits you: “I just clicked on a phishing link.” Whether the accident occurred on your Mac, through your email provider, or on your iPhone, the sinking feeling in the pit of your stomach that follows is real.
Phishing can be defined as a type of social engineering that involves attackers posing as well-known companies, services, or even individuals with whom you have some kind of acquaintance in order to persuade you to divulge personal details or to get you to do something malicious. In this article, we’ll cover what to do if you clicked on a phishing link.
How to tell if you’ve been phished and how to spot phishing links
Before you assume the worst, the first step is to determine whether, in fact, your click revealed anything. The following steps will help you evaluate the situation.
You landed on a login page and entered your credentials
The majority of phishing attacks are aimed at stealing your login information. The page might have appeared to be a login screen for Apple, Microsoft, or your bank, but the web address could have subtle differences, such as an added letter, a replaced character, or a new domain.
If you entered your password on a webpage that you now believe to be a fraudulent one, consider your credentials compromised. The same goes if you were redirected to a login page after scanning a QR code, an activity that is becoming more and more popular known as quishing.
A file downloaded to your Mac
If a file suddenly appears in your Downloads folder after clicking a suspicious link, treat it as a warning sign. On a Mac, malicious downloads often come as .dmg, .pkg, .zip, or .mobileconfig files, but attackers can also disguise threats inside documents, disk images, or fake update installers.
Cybercriminals frequently label these files as software updates, invoices, security alerts, or document previews to make them look legitimate. If you opened or installed the file, assume that your risk has increased, and scan your Mac immediately.
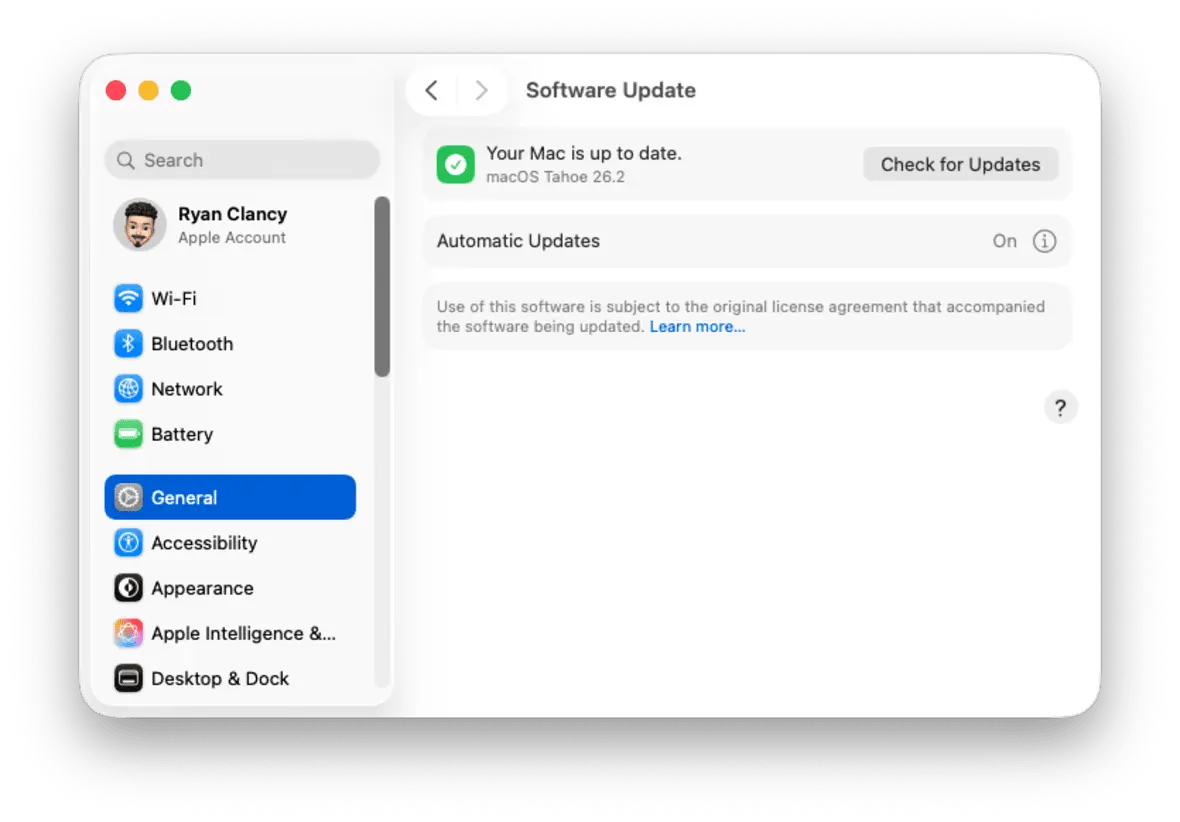
You were asked to install a configuration profile
There are phishing websites that tell you to add a configuration profile in System Settings. A profile has the ability to modify DNS settings, reroute your traffic across attacker-controlled servers, install malicious root certificates, or impose browser restrictions in such a way that you might find it difficult to reverse such changes.
On your Mac, go to System Settings (or System Preferences on older macOS versions), and go to General, then review Device Management or Profiles. Examine the list carefully and remove anything you don’t recognize.
You approved access to a third-party app
Not all phishing attacks steal your password. Some of them redirect you to a legitimate-looking permission screen and ask you to grant access to your account via an app.
Be sure to download applications only through reliable sources like the Mac App Store or trusted developers, and never give authorization to applications that you did not intentionally install.
Your accounts or browser behave differently
Your first indication that something is wrong may be strange behaviors. Watch for:
- Email notices to reset passwords you did not ask to be reset
- Login notifications in unrecognized locations
- Unexpected logouts
- New browser extensions
- Webpages that take you to other websites that you are not familiar with in Safari or Chrome
Active session tokens can also be stolen by modern phishing kits, which can provide temporary access to an account without re-entering credentials.
If any of these is the case, do not wait. The next step is critical. Run a full system scan with Moonlock for Mac to start checking your Mac for malware immediately.

What really happens when you click a phishing link?
When you click on a phishing link, several things can happen behind the scenes, and not all of them are obvious. Here’s how it typically unfolds.
Redirect chains begin
The link takes you through several tracking domains before leading to the last malicious page. This assists the attackers in concealing the actual destination and evading detection.
A fake website loads
A majority of phishing attacks result in duplicated login sites that replicate Apple, Microsoft, Google, or banking websites near perfectly. Others now apply AI-generated layouts and dynamism to appear even more believable, a trend in the rise of AI-driven phishing and scam tactics.
Credential harvesting triggers instantly
If you enter your login details, the site records the information in real time. Most attackers automate the process and try to log in to accounts within minutes.
Session cookies may be stolen
More sophisticated phishing kits don’t just harvest passwords. They steal active session tokens from your browser that may enable temporary access to your accounts without requiring your credentials again.
Malware may download silently
If you clicked a phishing link on Mac and a file has been automatically downloaded, it could either install itself or wait until you open it.
Drive-by scripts may run
Sometimes, all that’s required to start an attack is to visit a malicious website and then run the associated scripts that favor outdated web browsers or system weaknesses. This is much rarer on full versions of macOS. However, an unpatched system renders your system more vulnerable.
Keeping macOS and iOS updated significantly reduces this risk.
I clicked on a phishing link. What should I do now?
Step 1: Run a malware scan immediately
If you have clicked a phishing link on Mac, scan the system with a reliable security software. Sign up for a free 7-day trial of Moonlock for Mac in order to detect any malware and phishing attacks.

If you want to check manually, follow this guide on how to check for malware on Mac. If the scan identifies anything, delete it at once by following the instructions to remove malware from Mac.
This should be done prior to password changes. It’s no use updating credentials on a compromised device.
Step 2: Disconnect from the internet (if you installed something)
In case you have downloaded and installed a file, disconnect temporarily from Wi-Fi. This restricts outbound communication in case the malware is running. Reconnect to the internet after scanning and removing detected threats.
Step 3: Change your passwords and enable 2FA/MFA
If you entered credentials after you click on a phishing link, change the passwords immediately. Use strong and unique passwords (using at least 8 characters) and turn on 2-factor or multi-factor authentication (2FA/MFA)
Start with:
- The compromised account
- Your primary email account
- Apple ID
- Bank accounts or financial accounts
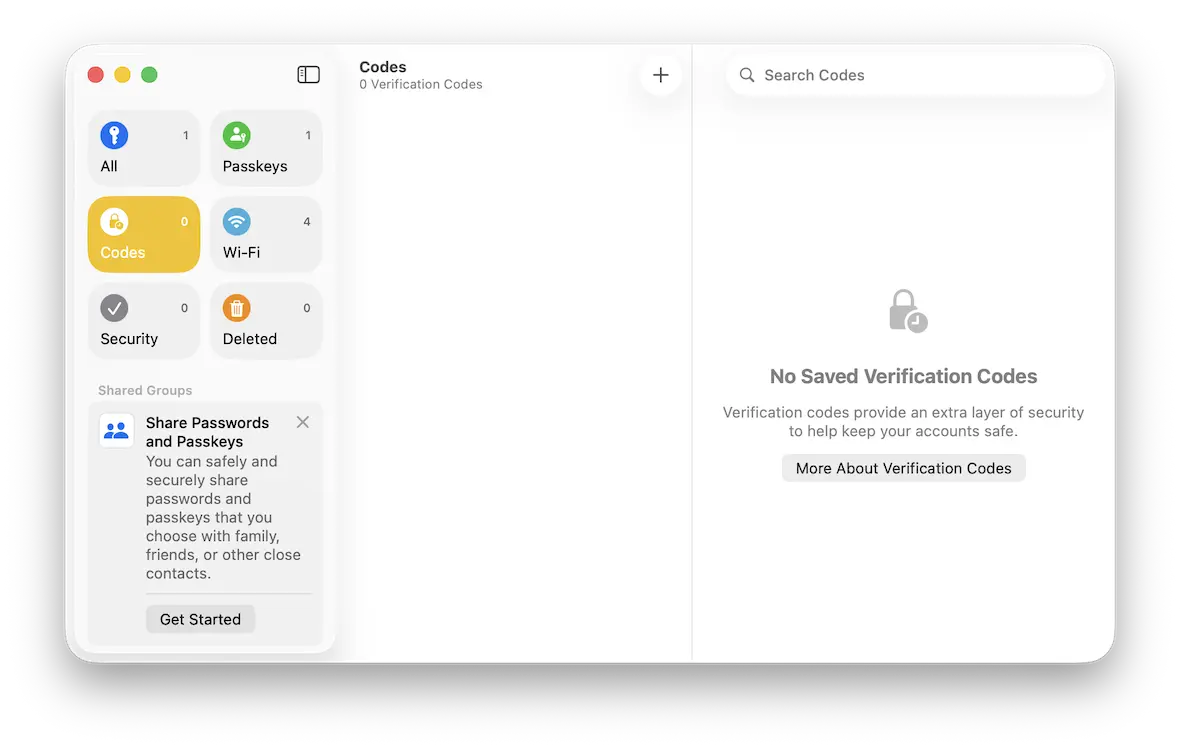
Step 4: Use an authenticator app and password manager
- Use an authenticator app instead of text message codes for stronger protection.
- When possible, use a password manager to create and safely store unique passwords for each account.
Step 5: Monitor your accounts
Although there is nothing amiss on the surface, do not think that you are in the clear. Phishing attacks frequently result in delayed account compromise.
Here are a few red flags:
- Unusual login alerts
- Password reset attempts
- New recovery email addresses
- Unrecognized financial transactions
Step 6: Report the phishing attempt
Reporting assists in the reduction of attacks in the future. Here’s what you should do:
- Send the address of the phishing email to your provider.
- Report the phishing of an Apple ID to [email protected].
- Inform your bank if financial information was involved.
In the event that this happens at the workplace, inform your IT department.
Why do scammers spread phishing links?
Phishing isn’t random. It’s profitable. Attackers enjoy sending and spamming phishing links with the intention to:
- Steal login credentials
- Access financial accounts
- Commit identity theft
- Deploy ransomware
- Sell stolen information on the black markets
Some campaigns are mass-distributed. Others are very specific and personalized, referred to as spear phishing. Attackers rely on the data concerning your occupation, your social media presence, or recent communications to make the message sound legitimate. The objective is simple: make it urgent, so you click without thinking.
Where do phishing attacks happen most often?
Phishing isn’t just limited to emails. It happens in various channels:
- Email messages
- SMS and iMessage texts
- Social media direct messages
- Fake tech support pop-ups
- Search engine ads
- QR codes in public spaces
United States authorities have also cautioned users about advanced campaigns based on QR, such as an FBI warning about North Korean QR phishing. Always take a moment before clicking a link to ensure that it is legitimate.
How to verify a suspicious link before clicking
Hover before clicking
Move the cursor over the link to check the whole URL and verify the destination before clicking.
Check the domain carefully
Attackers often use typosquatting by creating lookalike web addresses with small letter changes to make fake sites appear legitimate, a common phishing tactic.
Avoid logging in through email links
Rather than clicking on a link in an email or a text message, open a new browser and go to the official site. This will eliminate the possibility of going to a fraudulent login page.
Be cautious about urgency
Phishing messages usually generate a false sense of urgency to coerce you into acting without thinking.
When a message requires urgent action, pause and cross-examine the message to ensure that it is from the actual sender and is legitimate before clicking.
Phishing FAQs: Everything you should know after clicking a phishing link
Once you have clicked a phishing link, the next essential action is to determine your real risk. We provide the answers to the most frequently asked questions.
Yes, especially if malware downloads or you enter credentials.
Nothing will normally occur; however, it is always a good idea to scan your device.
Immediately change the compromised passwords, turn on multi-factor authentication (MFA), and look through the recent logins to detect any unauthorized access.
Disconnect from the internet and scan your device for malware.
Perform a complete malware scan and delete any threats detected, then change your passwords.
iPhone infections caused by phishing links are uncommon. Still, take a look at your General settings to see if there are unknown configuration profiles and watch out for unusual login activities on your accounts.
Report it to your email provider, Apple, or the appropriate financial institution.
How to reduce your risk of phishing scams
Phishing is effective because it plays on human psychology and behavior. To reduce your exposure:
- Update macOS and iOS operating systems routinely.
- Always use strong and unique passwords with 8 characters or more.
- Enable multi-factor authentication (MFA).
- Do not use login links sent through spam email.
- Check related applications on a regular basis.
- Use real-time protection such as Moonlock.
Clicking a phishing link doesn’t automatically mean your Mac is compromised, but ignoring it might. The difference between a minor scare and a serious breach often comes down to how quickly you respond. Scan your system, secure your accounts, and assume exposure if you entered credentials. Phishing succeeds when it goes unchecked. Make sure yours doesn’t.
To have round-the-clock protection against phishing, malware, and other emerging social engineering attacks, begin by scanning all your systems with the free trial Moonlock for Mac and make sure your system is clean before moving forward.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Apple Inc. Mac and macOS are trademarks of Apple Inc.