Keyloggers are just one type of malware that threatens your computer. So it’s imperative you know what they are and how to detect a keylogger on a Mac.
Fortunately, keyloggers are easy to remove (with the right tools and knowledge). This article will provide you with everything you need to know.
What are keyloggers, and how do they work?
A Mac keylogger is a type of malware that, when it arrives on your device, begins detecting your keyboard activity. It sends a record of all of the keys pressed back to a third-party server owned by the keylogger’s maker.
Attackers don’t need to “hack” systems the way they used to, they just log in. Stolen credentials have become the easiest and most reliable way in, and the data shows it clearly.
In 2025, 22% of all breaches started with compromised credentials, making it the most common entry point, even ahead of phishing. What makes this worse is how quietly these attacks play out. Breaches involving stolen logins take around 292 days to detect and contain on average and cost close to $4.8 million per incident, giving attackers plenty of time to move through accounts and systems without raising alarms. And early signals from 2026 suggest this problem isn’t going away.
By logging all of your key presses, the hacker can see your usernames, passwords, credit card numbers, personal chat messages, and other sensitive private data you’ve inputted into a website.
It’s worth pointing out that keyloggers do also have legitimate uses. Some employers use them to ethically monitor their employees. Parents may also use them to keep an eye on their child’s computer usage.
However, the focus of this article is on keylogger malware.
Types of keyloggers: hardware vs software
Keyloggers can be hardware or software. A hardware keylogger is a small device that sits between the keyboard and computer, capturing keystrokes directly at the source. This makes them incredibly hard to detect with antimalware software. Plus, they require physical access to the device to remove them.
Software keyloggers, on the other hand, are a type of spyware that gets installed on a hacked device. They record your keystrokes through the operating system, sometimes including screenshots, clipboard data, and browser activity.
How do keyloggers get installed?
When it comes to software keyloggers, they get installed the same way as other types of malware that can infect your device, such as:
- Infected or malicious email attachments
- Fake or cracked software downloads
- Malicious browser extensions or plugins
- Compromised websites or drive-by downloads
- Social engineering tricks
- Trojanized or exploited legitimate apps
Known keylogger examples
Keyloggers are often part of much larger spyware or trojan campaigns designed to steal credentials and monitor user activity. This is why you might find the same few names repeated in surveillance news reports, as attackers continue to recycle the same functioning keyloggers. Some of these include:
- FinFisher (FinSpy): This is a commercial surveillance tool used by companies and governments to monitor agents. It includes keylogging, screen captures, and remote access features. It can be used on Windows, macOS, iOS, Android, and Linux devices.
- Zeus (Zbot): Part of a trojan malware package, it’s a banking trojan that targets banking applications and websites to steal online credentials. It uses man-in-the-browser attacks to collect user data before it’s encrypted via HTTPS.
- SpyEye: A primary competitor of Zeus, SpyEye also targets browsers rather than operating systems. It can infect Chrome, Safari, Opera, Edge, and Firefox, allowing attackers to steal users’ online credentials, usually their banking information.
- Ghost Keylogger: One of the first keyloggers to become widespread, it’s highly invasive and records all keystrokes, web activity, and application use, and can periodically send out logs to a pre-defined email address.
- Agent Tesla: Categorized as a remote access trojan (RAT), Agent Tesla can collect all sorts of data from infected devices, including browser activity and email clients used on the device.
How to detect a keylogger on a Mac
So, how do you find a keylogger on a Mac computer? The best option is to use our favorite Mac keylogger detector tool. But you can also check for a keylogger on a Mac manually, which is slightly less reliable.
Check for keyloggers with Moonlock

The best keylogger detection software for Mac is Moonlock. By scanning for keyloggers, it will pick up any hidden threats and securely remove them for you.
Later in this article, we’ll provide a step-by-step guide on how to do this with Moonlock.
Check your Applications folder for suspicious apps
Any malware, whether it’s a keylogger or something else, needs a location on your computer from which it can operate. This is often an app that has been installed on your Mac without your permission.
Look in your Applications folder and see if anything looks suspicious. It could be anything from the name to the quality of the app’s icon image. It could also simply be that you didn’t install it in the first place.
If you find anything, delete it immediately.
Keyloggers often come in a bundle with data stealers, downloaded as cracked apps, so keep an eye on what you install on your Mac.
Mykhailo Pazyniuk, Malware Analyst at Moonlock
Beyond the Applications folder, keyloggers often use system startup locations to hide and persist. Check ~/Library/LaunchAgents and /Library/LaunchDaemons for suspicious .plist files — these are common persistence locations that automatically launch code when your Mac starts. Use Finder > Go > Go to Folder to navigate directly to these directories. If you find any unfamiliar .plist files in these locations, they’re likely malicious and should be deleted immediately.
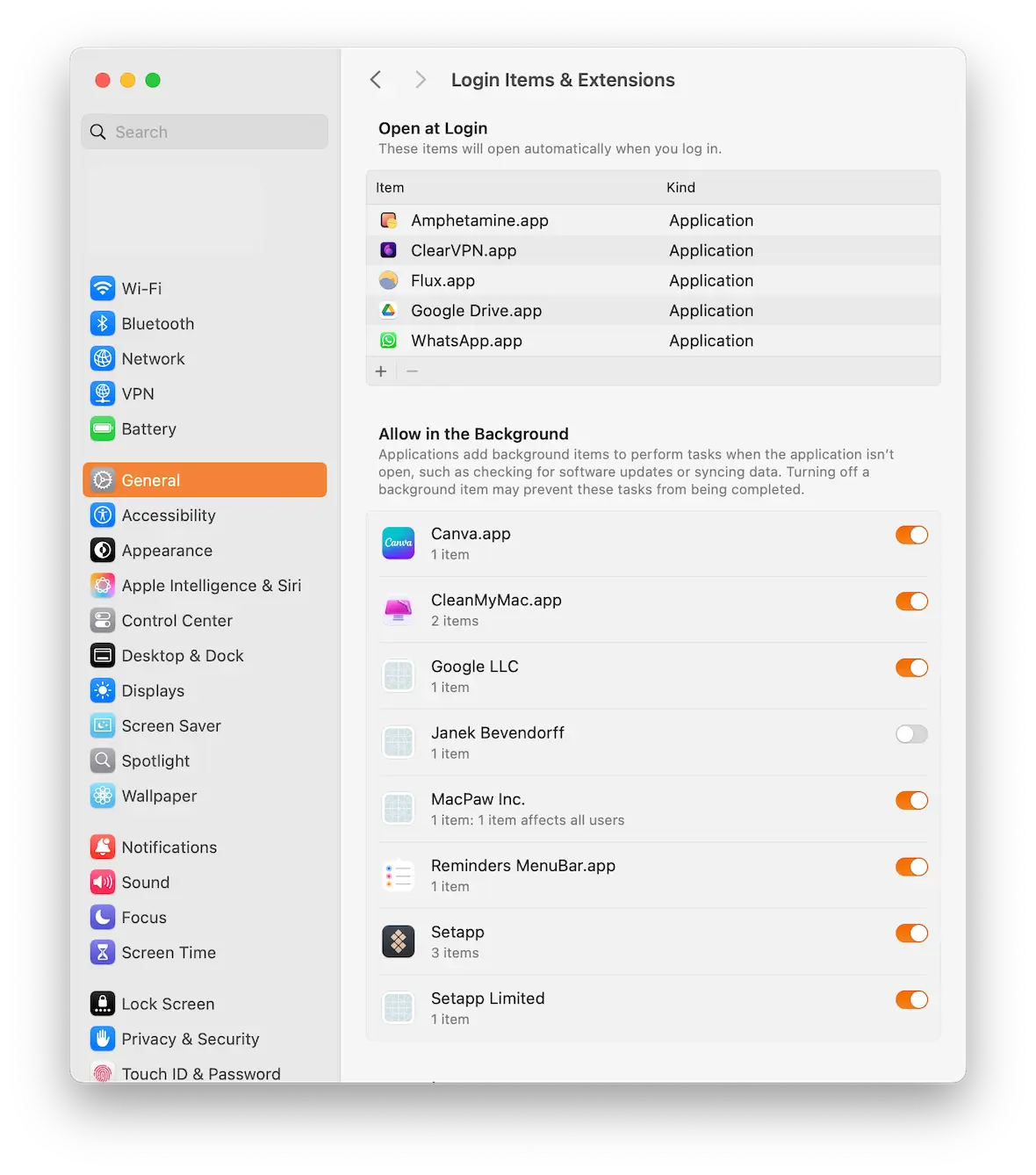
Review app permissions and login items
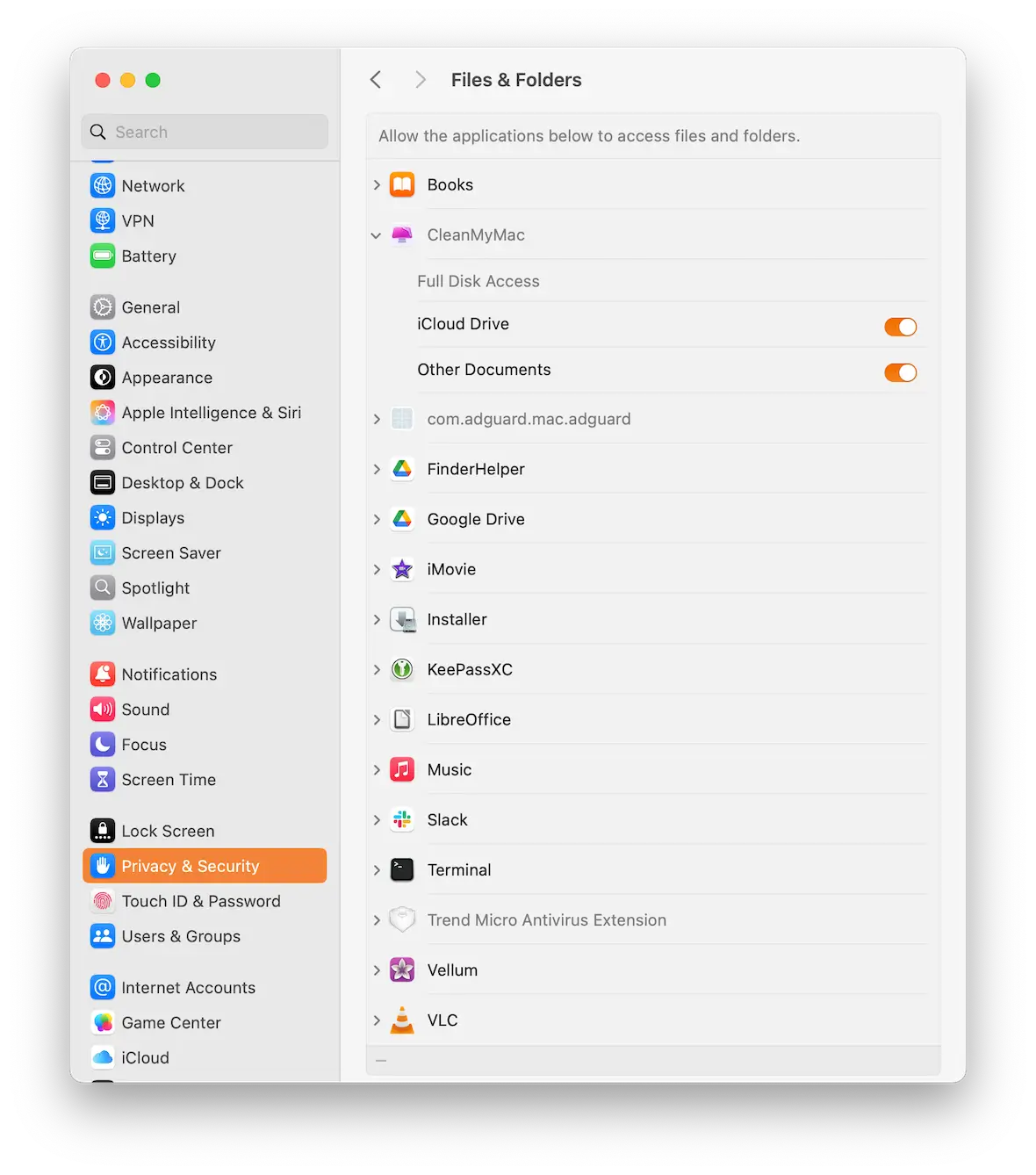
The next step in detecting keyloggers on a Mac is to go to System Settings and check app permissions and login items.
If you installed an app that you believed to be legitimate but turned out to be a keylogger, it may have given itself permissions that you didn’t approve of. The same applies to login items — programs that automatically start when the Mac boots up. A keylogger will try to make itself a login item.
To check app permissions, go to System Settings > Privacy & Security.
To check login items, go to System Settings > General > Login Items & Extensions.
Pay special attention to three permission categories most commonly exploited by keyloggers: Full Disk Access, Accessibility, and Input Monitoring. These three permissions give applications control over your keyboard input and file system — exactly what a keylogger needs to operate.
Look for large running programs in Activity Monitor
Another step in the Mac keylogger removal process is to look in Activity Monitor and check for suspicious processes.
Filter the CPU and memory lists so the higher values are at the top. Now, look at the top of the list. Which ones are taking up most of your CPU and memory? Run a web search for the name of the process to see if it’s known.
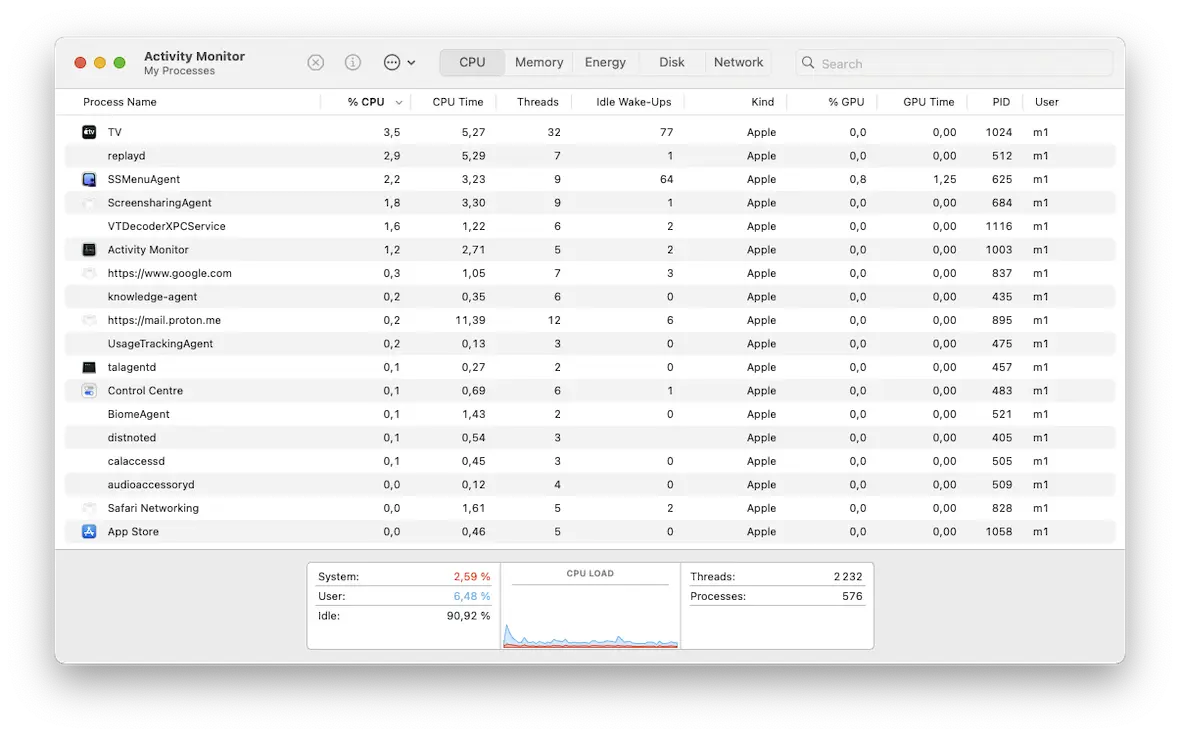
Most legitimate processes usually shouldn’t use huge amounts of CPU or memory, though some tasks – like system scans or having 200+ Chrome tabs open can temporarily be resource-intensive. Open Activity Monitor and watch for processes you don’t recognize, as these could be a sign of malware.
For example, the Spyrix keylogger may appear in Activity Monitor under the name “skm.” You’re unlikely to find spyware or malware operating under its “official” name. Generally, if you don’t recognize a process, you can open Terminal and type the command below to view its manual entry and function.
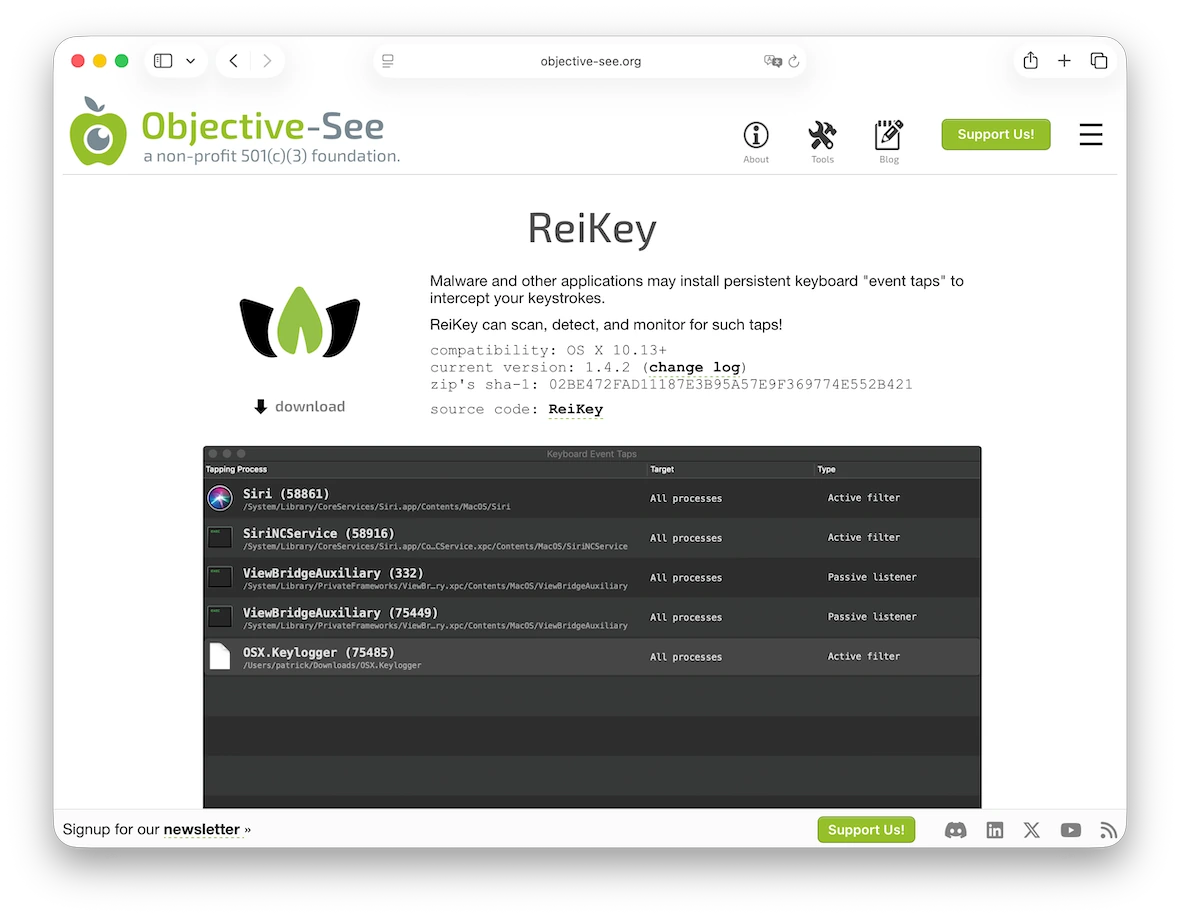
man [process name]You can also use Objective-See’s ReiKey, a free, open-source tool that monitors for keyboard taps, which is how most macOS keyloggers get installed. It’ll send out alerts as soon as it detects a tap, providing more information on it.
How else can you tell if there is a keylogger on your Mac?
The telltale signs, unfortunately, don’t stop there. Here are some more ways to tell if you have an intruder on your Mac.
Watch for unusual network activity
Keyloggers need to send your private data to a remote server, but if they only do it occasionally, you probably won’t notice any slowdowns in your Wi-Fi. A better approach is to watch for suspicious outgoing connections to unknown IP addresses or domains, which can be a sign that something is trying to steal your data.
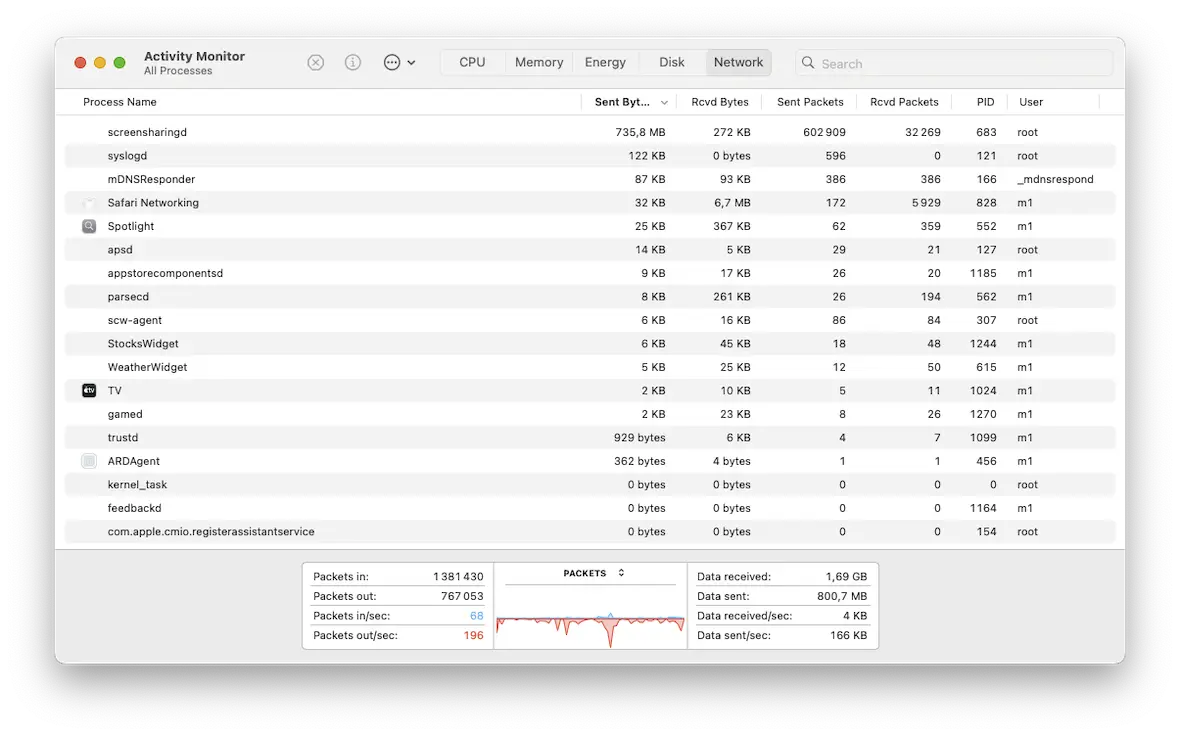
Instead of just turning off Wi-Fi, keep an eye on suspicious outgoing connections that could indicate a keylogger is sending your data somewhere.
There’s no need to manually monitor your connection. You can use Little Stitch by Objective Development to monitor application connections. It’s a host-based application firewall designed specifically for macOS that can alert you to background processes attempting to connect to unknown remote servers.

You’re getting 2FA codes sent to you
Since a keylogger will be sweeping up your keystrokes, it will start to collect your login details for various sites. If it attempts to infiltrate a site that is protected with 2-factor authentication, you may get 2FA codes sent to your email.
If you get 2FA codes for an account you haven’t logged into, investigate it immediately. Needless to say, don’t click confirmation links either.
Your other accounts are being hacked
The keylogger will eventually get lucky and find one of your accounts that is not protected by 2-factor authentication. In that case, the hacker is in, and it can start rummaging for useful information.
In the case of social media, they can also send messages from your account to your followers. If you suspect that you have a keylogger, then warn people immediately not to respond to messages.
Your computer is running slow
Some older or poorly designed malware, including keyloggers, can consume lots of power, slowing down your machine or even causing crashes. However, modern malware is often more sophisticated and designed to run quietly, using minimal CPU and memory so it’s harder to detect.
Close down all unknown processes and unneeded legitimate programs. Isolate the troublemaker.
Advanced keyloggers nowadays delay keystroke uploads, mimicking human activity patterns to evade anomaly detection.
Mykhailo Pazyniuk, Malware Analyst at Moonlock
How to remove a keylogger from your devices
Now it’s time to discuss the best Mac keylogger removal method. We’ll also cover how to do this on iPhone, since mobile devices are prime targets for keyloggers and other malware.
How to safely remove a keylogger from your Mac
Earlier, we mentioned that our top choice for detecting a keylogger and removing it is Moonlock. Here’s a step-by-step guide on how to use it:
- Sign up for a free trial of Moonlock and download it.
- Open Moonlock and click Malware Scanner on the left.
- If you’re using the software for the first time, select Deep scan and then click Configure in the dropdown menu. Select everything.
- Now that the setup has been dealt with, click Scan, and Moonlock will start going through your Mac, looking for keyloggers and any other threats on your MacBook.
- When keyloggers or other malware are found, Moonlock locks them away in Quarantine, so they can’t harm you. Select everything and click Remove.
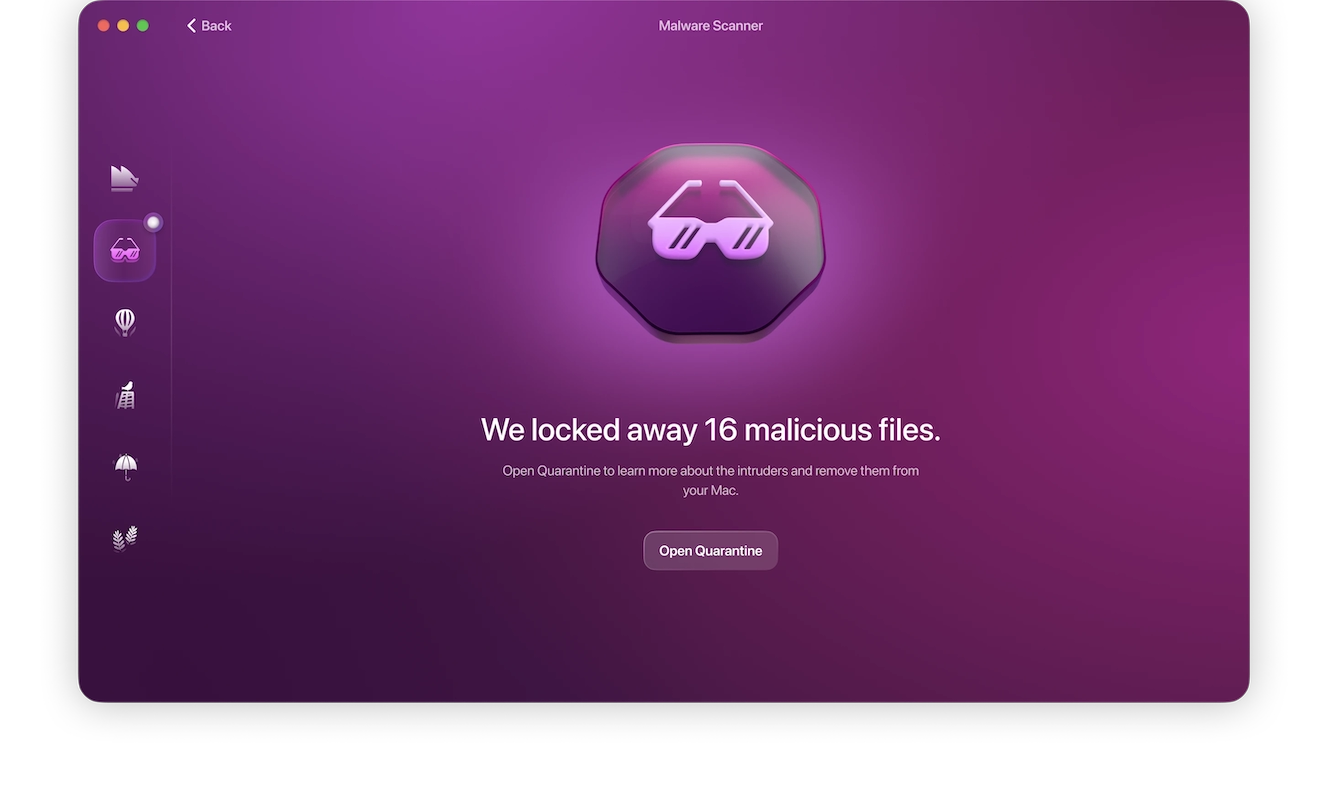
While you have Moonlock open, take an extra few minutes to use some of the other modules as well. System Protection and Security Advisor will give tips on how to make your macOS settings tighter and avoid malware in the future.
How to manually remove a keylogger from your Mac
If, for any reason, using Moonlock is not an option, the other alternative is to manually remove it. But this can be an unreliable process, as you won’t be certain that you got it all.
That said, if you want to remove a keylogger manually, here’s how:
- Watch for unusual outgoing network traffic, such as repeated or unexpected connections to unknown IP addresses or domains, which can be a sign of malware exfiltrating data.
- Go to the Applications folder, find any suspicious apps, and delete them.
- Check ~/Library/LaunchAgents and /Library/LaunchDaemons for unknown .plist files that may enable persistent processes.
- Check your settings to see if anything has been changed — your browser security settings, your firewall, FileVault, etc.
- Check for any unfamiliar or suspicious browser extensions in Safari, Chrome, and Firefox, and remove anything you don’t recognize.
- Remove all cookies, temporary files, and cache files.
- Check your email to see if 2-factor authentication has been disabled on any of your accounts.
- Install all available macOS updates and app updates.
- Reset your iCloud password.
- To be absolutely sure, consider wiping and resetting your Mac.
- If you end up performing a factory reset, avoid restoring your data using the latest Time Machine backup, as it may reintroduce the keylogger. Instead, manually copy your files from the backup and reinstall your apps one by one. Only pick the Time Machine backup if you know for sure the version is clean.
How to get rid of a keylogger on your iPhone
iPhones, like most Apple devices, are secure straight out of the box. However, your risks increase significantly if the device is jailbroken or running an outdated version of iOS. Typically, keyloggers on iPhones appear in the form of malicious custom keyboards, malicious configuration profiles, or spyware on jailbroken devices.
Here’s how to get rid of a keylogger on iPhone:
- Look at your list of installed apps and remove any that you didn’t install. If a keylogger is trying to hide by using a legitimate name, look to see if the icon for the real app is the same.
- Check your keyboard settings for anything suspicious. Go to Settings > General > Keyboard > Keyboards. You should only find Default and Emoji. Delete any unknown keyboards, especially if “Allow Full Access” is enabled.
- Check for and remove any suspicious configuration profiles. Go to Settings > General > VPN & Device Management. Delete any profiles you don’t recognize.
- Install any available iOS updates and app updates.
- Keep a close eye on your iPhone’s battery usage, as excessive draining could be a sign of background processes. Go to Settings > Battery and Settings > Cellular. There, you can see any apps using too much energy or data, as keyloggers show a spike in data usage when they send out their logs.
- Wipe your Safari browser settings.
- Reset your iCloud password.
- If you’re still not sure if you got it all, consider wiping and resetting your iPhone to its factory settings.
Keylogger FAQs: what they can do and how they affect your devices
The best way to keep yourself safe from keyloggers is to understand how they work.
Yes, a keylogger can capture everything you type on your Mac or iPhone, along with additional data. This includes your login credentials, credit card numbers, and private messages.
Look for unknown apps, custom keyboards you didn’t install from a trusted source, or unknown configuration profiles. Also, keep an eye out for unusual battery drain or spikes in data usage.
No, they can record data offline. However, they’ll need an internet connection to actually send the data.
Yes. Many keyloggers capture screenshots, clipboard data, and browser activity.
Yes. Through phishing, malicious downloads, or software vulnerabilities, attackers can install software keyloggers on your Mac.
macOS includes many built-in security features, but they’re not foolproof against more advanced or highly targeted threats.
How to protect your Mac from keyloggers
Once the keylogger is gone from your Mac, the next step is to ensure that it never happens again. You can increase your safety by observing the following rules.
Never click on links from people you don’t know or trust
Receiving a link from a relative or trusted friend is fine. But if you get sent a link from someone you barely know, or a complete stranger, then err on the side of caution and don’t click it. Unsolicited links could lead to malware-infected websites that host download links for viruses.
Never open email attachments from unknown senders
The same rule applies for email attachments. Never open email attachments from people you don’t know or barely know. There are an increasing number of PDF viruses, so keep a close eye on email attachments.
Limit your app downloads to the Mac and iOS stores
A keylogger could appear in the form of a trojan that hides behind legitimate software. Once you install the software, the trojan covertly installs itself, too.
You can remove this risk by restricting your app downloads to the Mac App Store (or the iOS App Store for iPhone). Apps there are strictly monitored and vetted for any malicious processes.
Change your passwords
As we indicated, a keylogger for Mac is going to scoop up every key you press, so your usernames and passwords will be compromised. The next step will be to change all your passwords. Yes, this can be tedious beyond belief. But it has to be done.
To make this process easier and more secure, use a password manager like 1Password or iCloud Keychain to generate and securely store strong, unique passwords for each account. A password manager eliminates the temptation to reuse passwords and ensures each account is protected with a randomly generated string.
Always enable 2-factor authentication
Finally, if you haven’t done so already — or if it was disabled by the keylogger — enable 2-factor authentication on all your web accounts.
A keylogger can steal your login details, but what it can’t get are single-use temporary codes from your other device. Multi-factor or 2-factor authentication can literally make or break your security.
It’s natural to panic when malware of any kind appears on your device. It can feel like a direct attack on you, with all of your private data suddenly up for grabs. But if you take a deep breath and follow the instructions laid out here, you’ll soon be destroying those keyloggers and sending the hackers packing.
This is an independent publication, and it has not been authorized, sponsored, or otherwise approved by Apple Inc. Mac, iPhone, and macOS are trademarks of Apple Inc.